Method and device for detecting security flaws of software source codes
A detection device and source code technology, applied in the field of software security, can solve the problems of insufficient comprehensive detection, limited detection methods, inability to effectively detect security vulnerabilities, etc., and achieve the effect of avoiding malicious manipulation and enhancing security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0045] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below with reference to the accompanying drawings and examples.
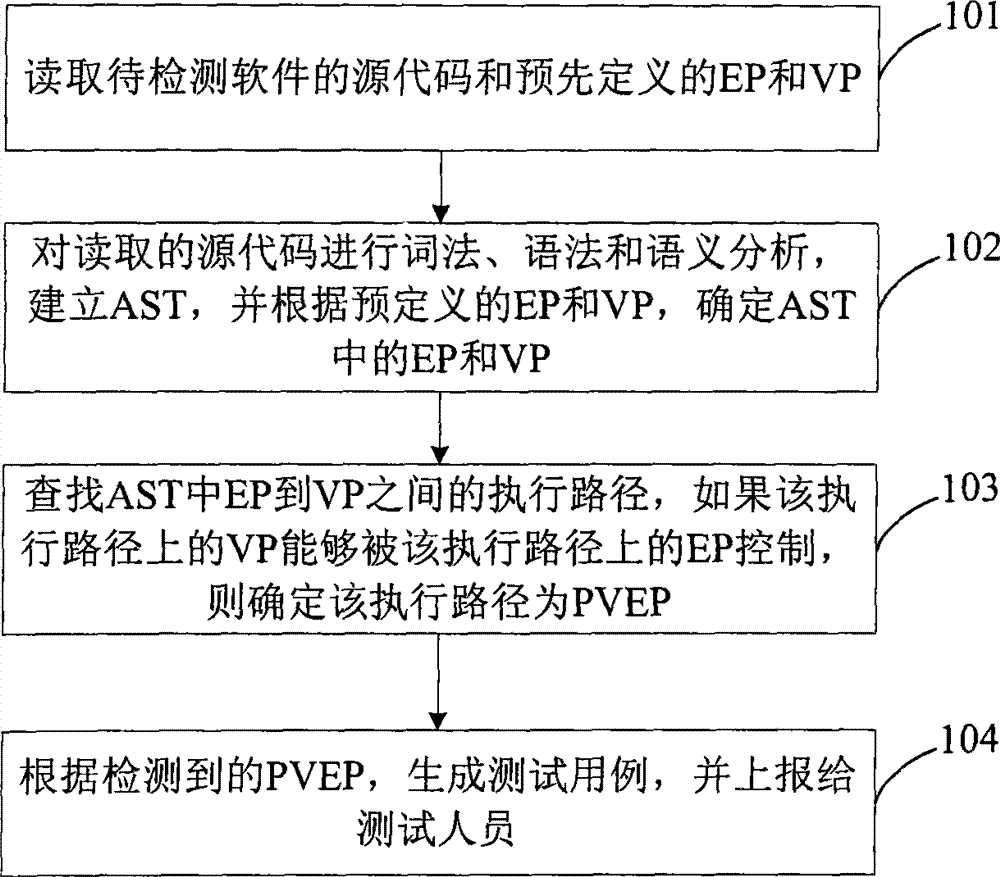
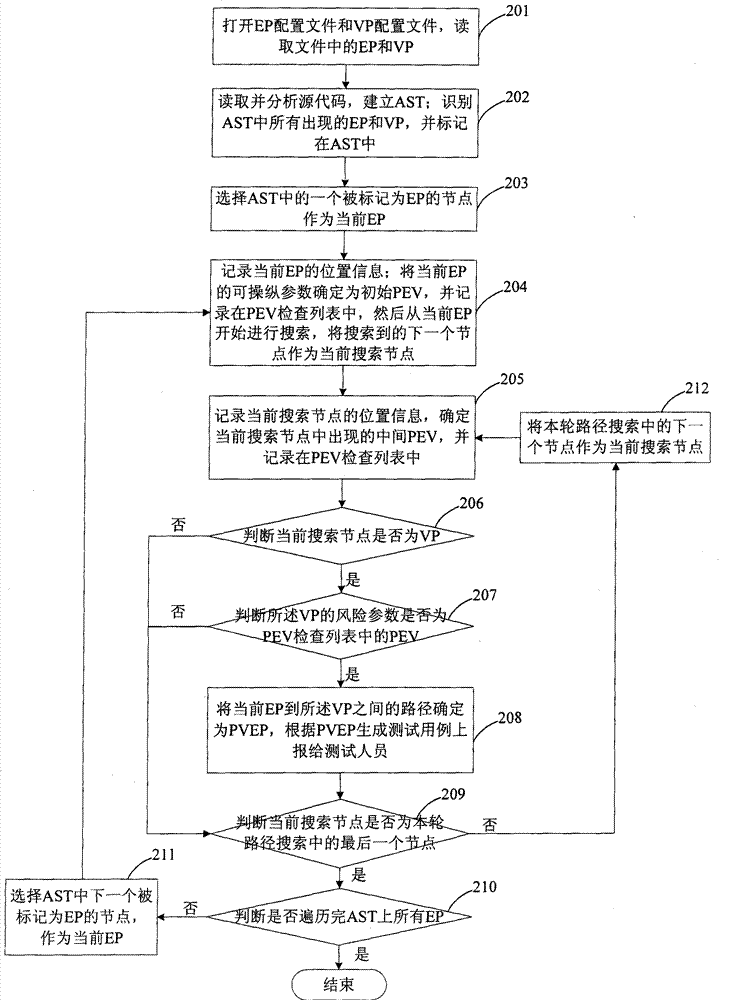
[0046] In practice, the attacker makes the software execute according to a certain path by inputting carefully designed specific data, which eventually leads to security problems such as buffer overflow and code injection. These execution paths that threaten software security are called Potentially Vulnerable Execution Paths (PVEP, Potential Vulnerable Execution Path), which are the targets of attackers. Therefore, the present invention achieves the purpose of detecting security loopholes by searching potential risk execution paths in software source codes.
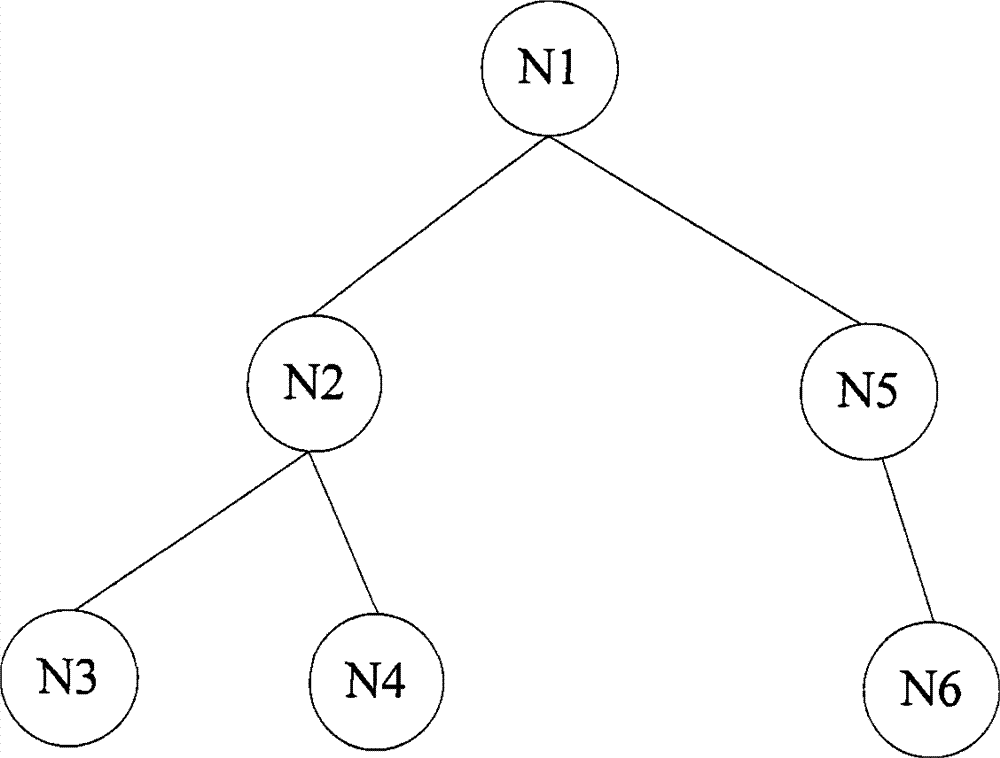
[0047]Based on the above considerations, the present invention provides a detection scheme for software security vulnerabilities. The scheme establishes an Abstract Syntax Tree (AST, Abstract Synta...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More