Novel unwanted code detecting method based on characteristics of function call relationship graph
A function call relationship, malicious code detection technology, applied in electrical digital data processing, instrument, platform integrity maintenance, etc., can solve the problem that users cannot deal with security threats in time, reduce detection effect, and local characteristics are not fixed.
Active Publication Date: 2011-04-27
SICHUAN UNIV
View PDF2 Cites 66 Cited by
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
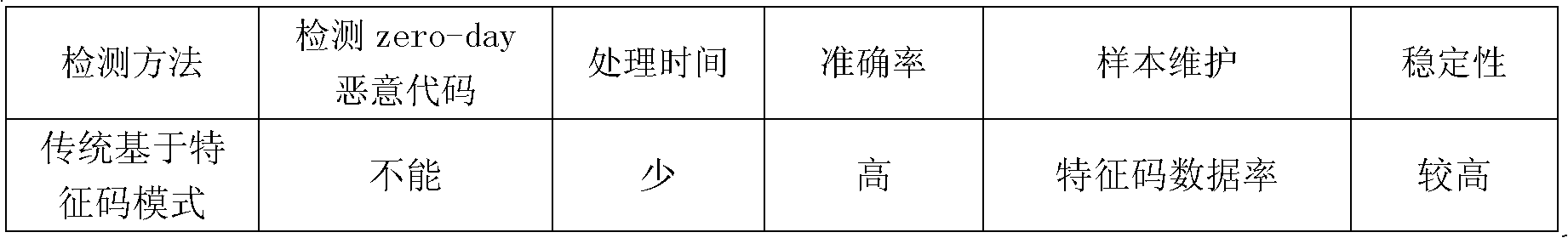
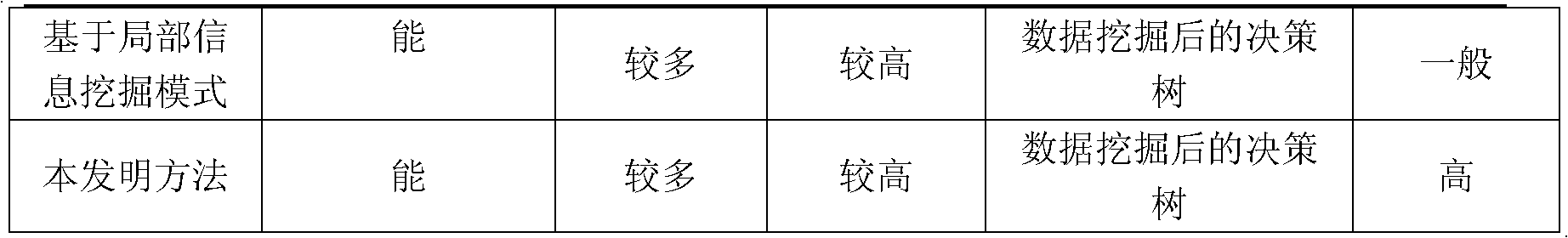
[0006] First, the detection method based on the signature needs to obtain the signature of the malicious code, and transfer the ever-increasing signature to the database of the client, and the maintenance of the increasingly large database becomes the price paid by the user
The biggest disadvantage of this detection method is that it is difficult to detect unknown malicious codes, and users cannot deal with new security threats in a timely manner.
[0007] Second, heuristic analysis or software behavior-based detection methods are used to classify software by obtaining special local information of codes, but for malicious codes that use fuzzy and polymorphic codes, such local features are often not fixed, so the detection method Insufficient accuracy in judging these malicious codes
[0008] Third, using standard format information to distinguish software detection methods uses the external description information of the software. Most of this information does not directly involve the behavior of the software. For malicious code designers familiar with this method, they can use the special format information processing to greatly reduce the detection effect of the method
Method used
the structure of the environmentally friendly knitted fabric provided by the present invention; figure 2 Flow chart of the yarn wrapping machine for environmentally friendly knitted fabrics and storage devices; image 3 Is the parameter map of the yarn covering machine
View moreImage
Smart Image Click on the blue labels to locate them in the text.
Smart ImageViewing Examples
Examples
Experimental program
Comparison scheme
Effect test
specific Embodiment
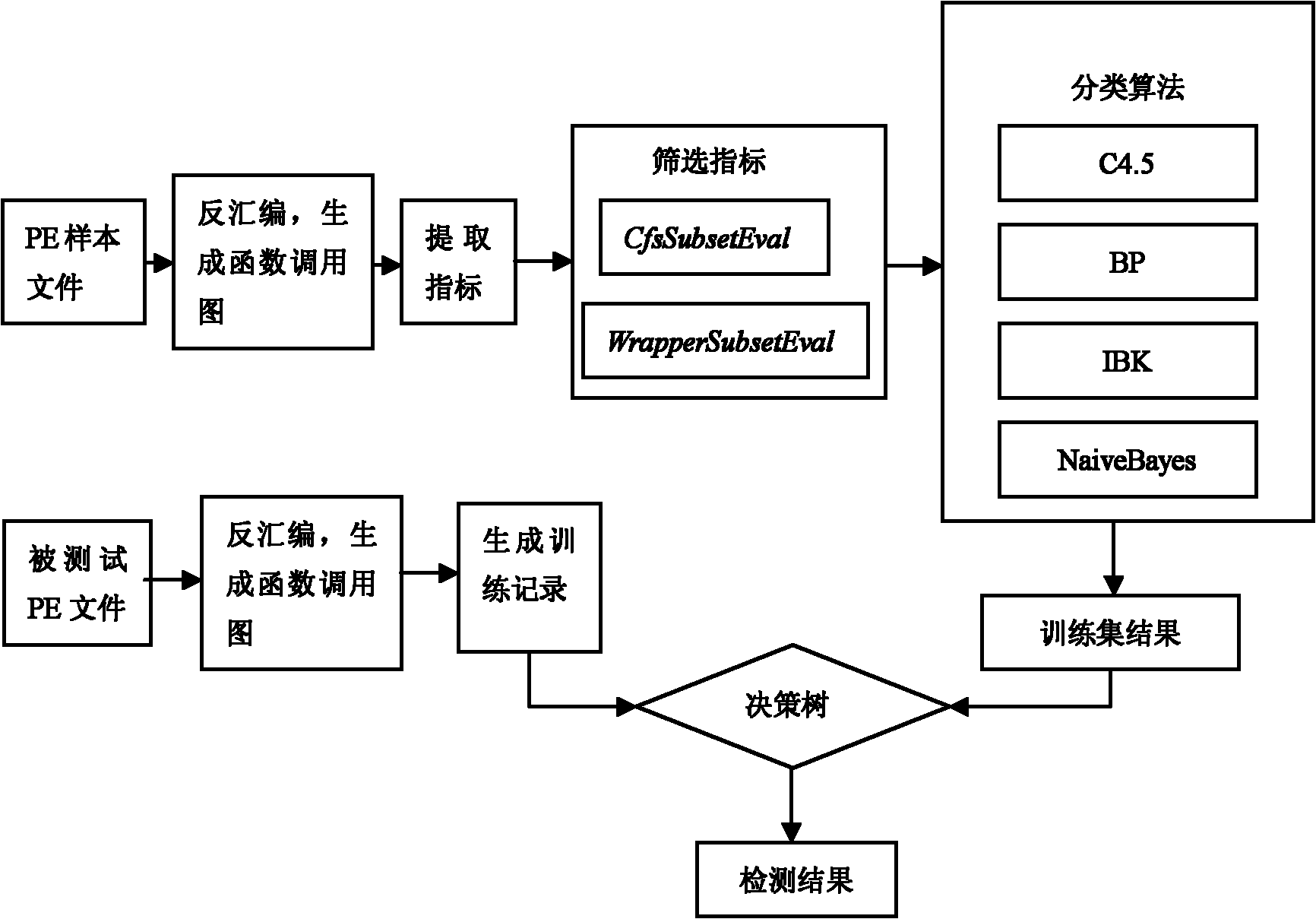
[0154] Brief information on the experimental datasets employed in the method of the present invention is described in Table 2. The normal files of the experimental data set are the system files and applications in Windows XP sp3 collected in the laboratory; the malicious codes are some virus files downloaded from the Malfease datasets website. The process of sample file processing includes disassembly, generating a function call graph, extracting graph feature indicators from it, and saving these data in arff type files. In the verification process of the method of the present invention, 10 fold cross-validation is adopted, and different classification algorithms are used in the testing process.
the structure of the environmentally friendly knitted fabric provided by the present invention; figure 2 Flow chart of the yarn wrapping machine for environmentally friendly knitted fabrics and storage devices; image 3 Is the parameter map of the yarn covering machine
Login to View More PUM
 Login to View More
Login to View More Abstract
The invention discloses a novel unwanted code detecting method based on the characteristics of a function call relationship graph. The traditional feature code detection technique which judges software by local characteristics has the drawback that a detecting tool is required to maintain a large amount of prior feature codes and the drawback that detecting schemes lack necessary stability and reliability. The method detects unwanted codes by extracting graph characteristic information on the basis of the function call relationship graph and the research results in existing software network. The main process of the method consists of three steps: 1, establishing a software function call graph; 2, extracting characteristic indexes from the graph; and 3, differentiating unwanted software and normal software by an effective data mining algorithm. The method can effectively detect common zero-day unwanted code and well detect unwanted codes adopting a fuzzy and polymorphic technique and can keep high stability in case of a calculated attack.
Description
technical field [0001] The invention relates to malicious software detection in computer information security, in particular to a novel and practical malicious code detection method based on the feature of software function call relation graph. Background technique [0002] With the wide application of computer science in various fields of society, the security of computer software has attracted more and more attention. Establishing a trusted software system has become an effective means to maintain computer information security, and the detection of malicious code has become the core research direction of software credibility analysis. [0003] The traditional signature-based detection method needs to be updated and maintained through a dedicated database to extract relevant signatures in advance, use the scanning engine to find the local information of the software, and use the string matching method to compare the similarity between these information and signatures. Accor...
Claims
the structure of the environmentally friendly knitted fabric provided by the present invention; figure 2 Flow chart of the yarn wrapping machine for environmentally friendly knitted fabrics and storage devices; image 3 Is the parameter map of the yarn covering machine
Login to View More Application Information
Patent Timeline
 Login to View More
Login to View More IPC IPC(8): G06F21/00G06F21/56
Inventor 王俊峰赵宗渠白金荣刘达富方智阳
Owner SICHUAN UNIV