Method and device for protecting/ restoring multicast tree
A recovery method and a multicast tree technology, which are applied in the branch office to provide special service devices, digital transmission systems, data exchange networks, etc., can solve the problems of large resource occupation and low protection efficiency, and achieve large waste of resources and low protection efficiency , time-saving and resource-saving effects
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
no. 1 example
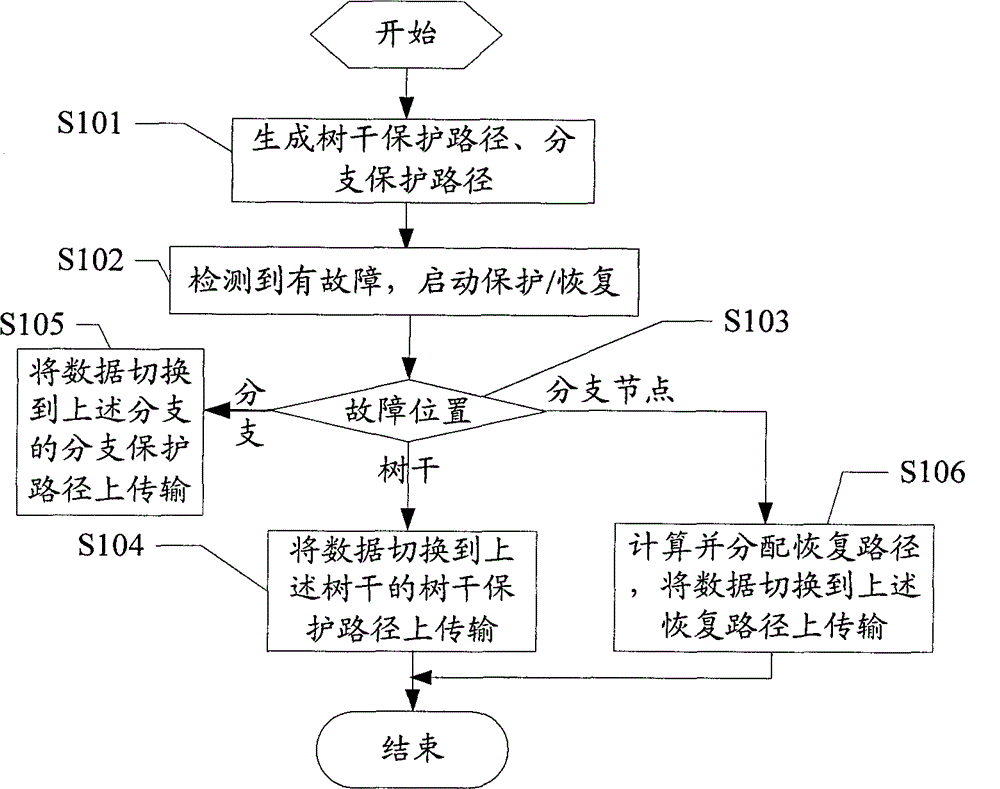
[0037] Such as figure 1 Shown is the flow chart of the first embodiment of the method of the present invention, including:
[0038] S101: Generate a trunk protection path for the trunk between every two adjacent branch nodes of the multicast tree; generate a branch protection path for the branches of the multicast tree;
[0039] The aforementioned branch nodes include a root node.
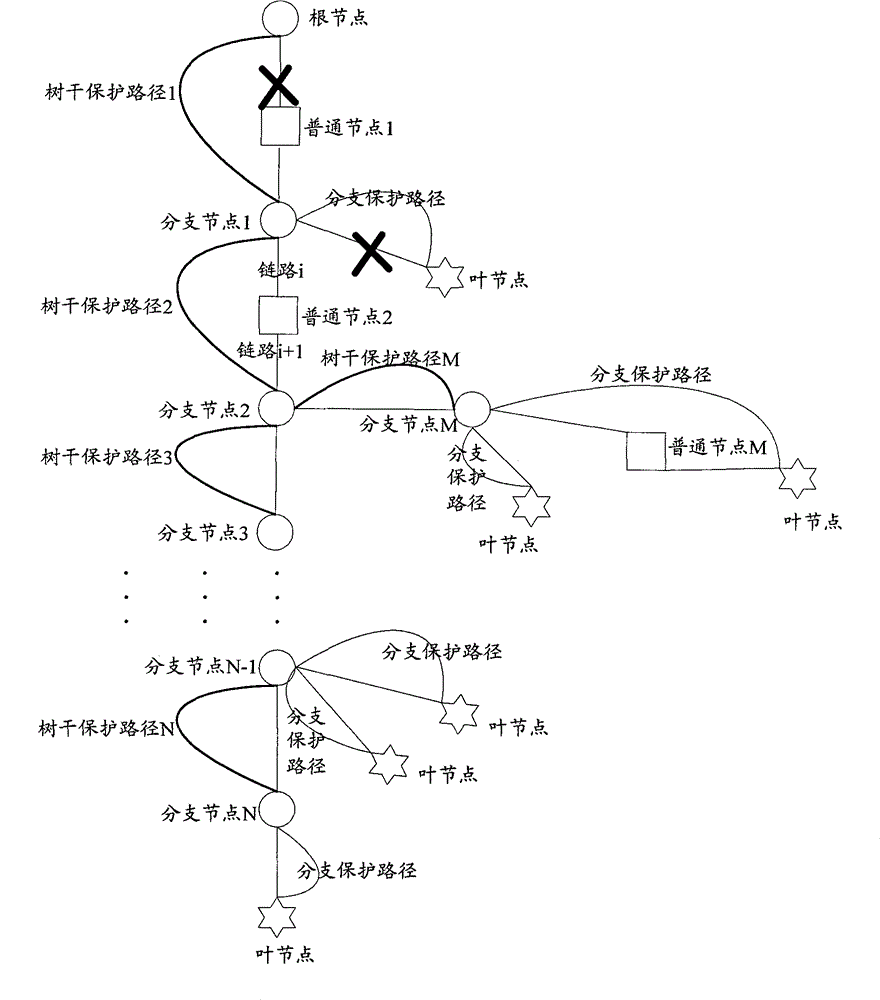
[0040] In a multicast tree, the link between the root node and the first (N=1) branch node downstream is called a "complete trunk", which is shared by all multicast members of the multicast tree. Once a failure occurs, all The data reception of multicast members; and the link between the Nth (N>=1) branch node and the N+1 branch node is called "partial trunk", which is common to all downstream nodes of the above N branch nodes , when a failure occurs, it will affect the data reception of all nodes downstream, and the "complete trunk" and "partial trunk" are collectively referred to as the trunk. ...
no. 2 example
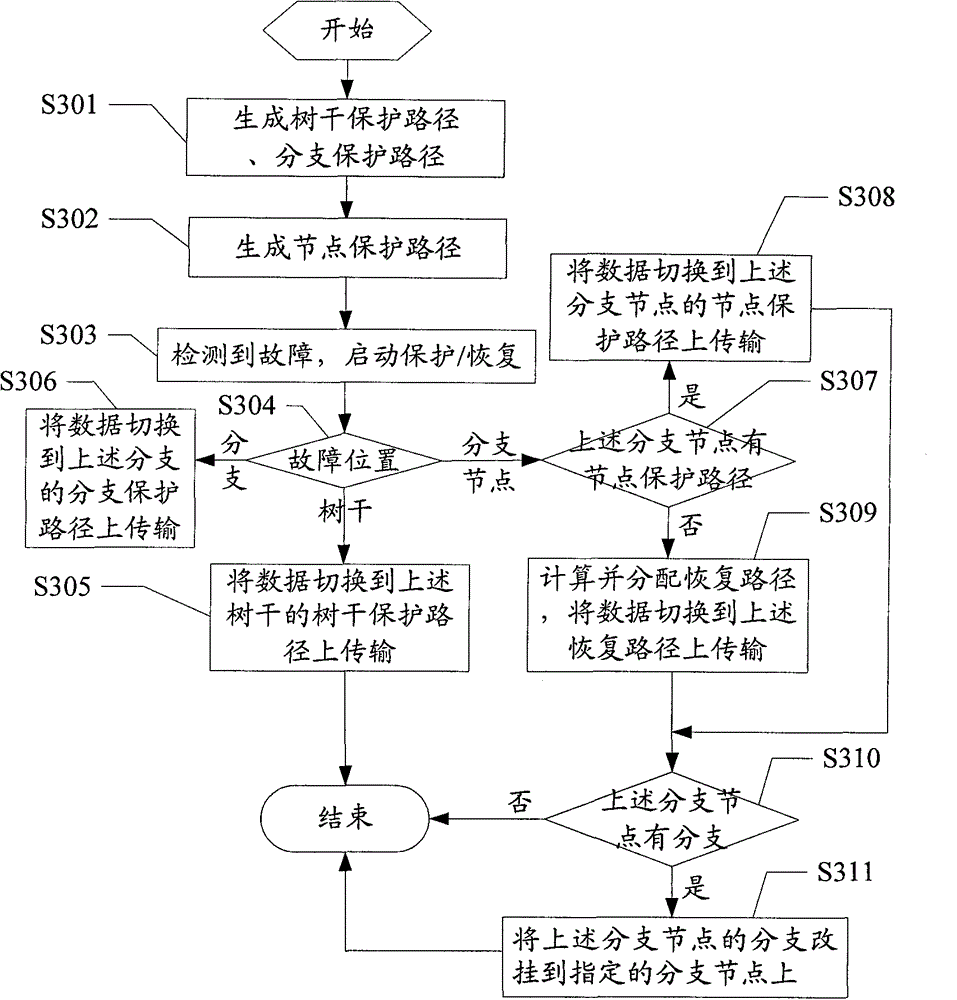
[0051] Such as image 3 Shown is the flow chart of the second embodiment of the method of the present invention, including:
[0052] S301: Generate a trunk protection path for the trunk between every two adjacent branch nodes of the multicast tree; generate a branch protection path for the branches of the multicast tree;
[0053] S302: Generate a node protection path for the specified branch node of the above multicast tree;
[0054] Such as Figure 4 Shown is a schematic diagram of a multicast tree with node protection paths. Taking this figure as an example, the process of generating node protection paths is as follows:
[0055] According to the user policy, it is assumed that the specified branch nodes are: root node, branch node 1, branch node 2, branch node 3, ..., branch node N-1, branch node N. Starting from the root node, search the above-mentioned branch nodes along the multicast tree. After the search is completed, a node protection path 1 is generated between the...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More