A dos/ddos attack detection method
An attack detection and purpose technology, applied in the network field, to meet the real-time requirements and prevent harm
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0015] The present invention will be further elaborated below in conjunction with specific examples.
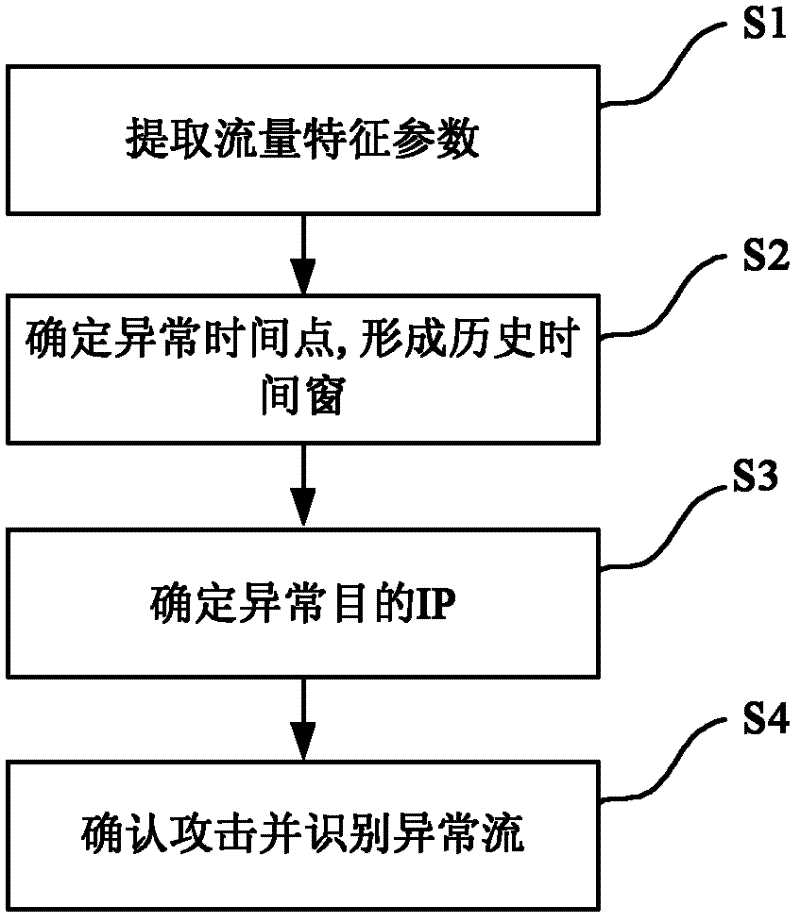
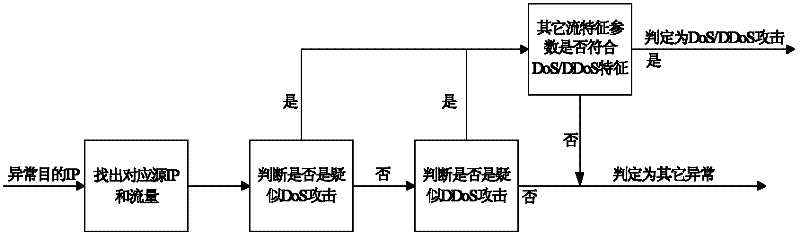
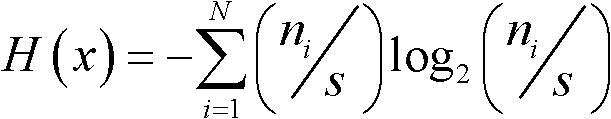
[0016] The DOS / DDOS attack detection method of the present invention firstly extracts the required traffic characteristic parameters, and calculates the information entropy, according to extracting the traffic characteristic parameters-determining the abnormal time point-determining the abnormal destination IP-identifying the abnormal flow and distinguishing the attack type The detection of DoS / DDoS attacks and the identification of abnormal flows are completed sequentially. The specific flow diagram is as follows figure 1 shown.
[0017] Specifically include the following steps:
[0018] S1. Obtain flow data in the network from network devices, and extract flow characteristic parameters from the flow data;
[0019] S2. Process the traffic characteristic parameters extracted in step S1, determine the abnormal time point, and expand according to the abnormal time point to fo...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More