Method, system and device for identifying user's identity
An identity and user technology, applied in the field of information security, can solve the problems of low global versatility, long operation time, and high card operator charges.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0154] Hereinafter, various specific embodiments of the present invention will be described in detail with reference to the accompanying drawings.
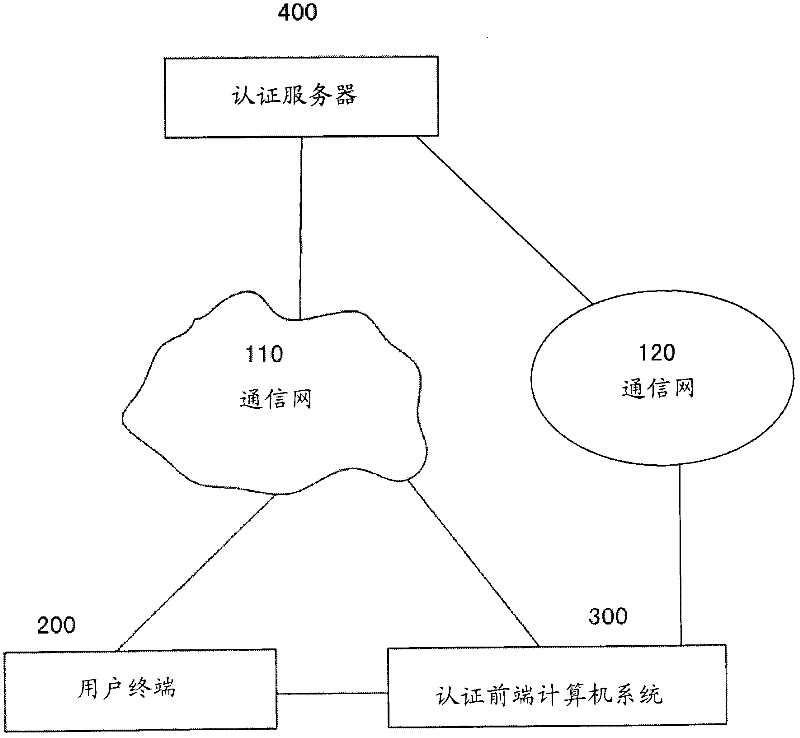
[0155] figure 1 A block diagram of a system for authenticating user identities according to an embodiment of the present invention is schematically shown. As shown in the figure, an authentication system according to an embodiment of the present invention includes an optional communication network 110 , a communication network 120 , a user terminal 200 , an authentication front-end computer system 300 and an authentication server 400 . The communication network 110 may be a wireless communication network or a wired communication network or a combination of the two, or a local area network (LAN), a metropolitan area network (MAN) or a wide area network (WAN), or a combination of two or even three of them. The communication network 120 may be a wireless communication network or a wired communication network or a combination of the ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com