Method and system for realizing distribution of smart cards
A technology of smart cards and instructions, applied in the field of smart cards, can solve problems such as data tampering
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0067] The technical solutions of the present invention will be described in detail below in conjunction with the accompanying drawings and preferred embodiments. It should be understood that the following examples are only used to illustrate and explain the present invention, but not to limit the technical solution of the present invention.
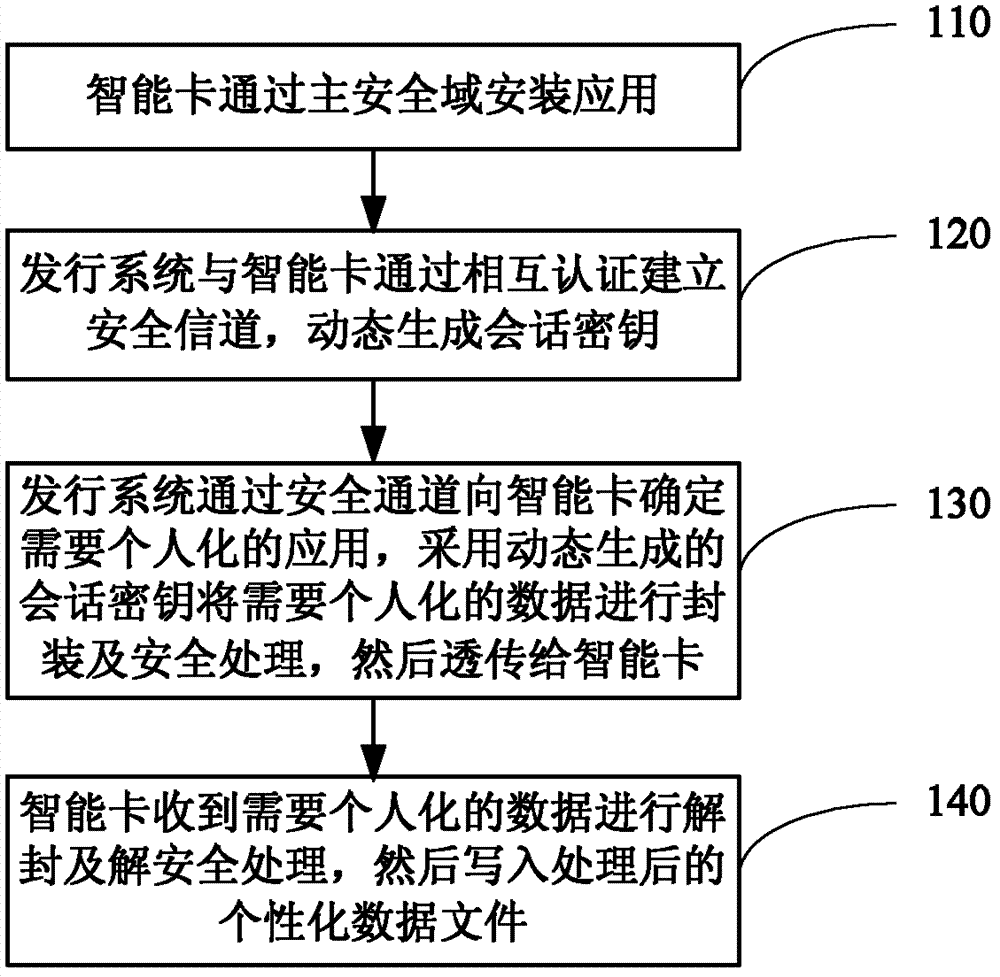
[0068] Such as figure 1 As shown, it is the flow process of the embodiment of the method for realizing smart card issuance provided by the present invention, including the following steps:
[0069] 110: The smart card installs the application through the main security domain;
[0070] When the installed application is not associated with the primary security domain (ISD) (for example, there are multiple providers of the installed application), it is also necessary to associate the installed application with the ISD.
[0071] For example, through the application of the ISD installation card of the (U)SIM of the private network, the appl...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More