Hotel public network wired/wireless unified authentication roaming method
A public network and wireless technology, applied in wireless communications, transmission systems, electrical components, etc., can solve the problems of inconvenience, cumbersome use, and inability to achieve diversified network access control requirements, and achieve the effect of simplifying the authentication process
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
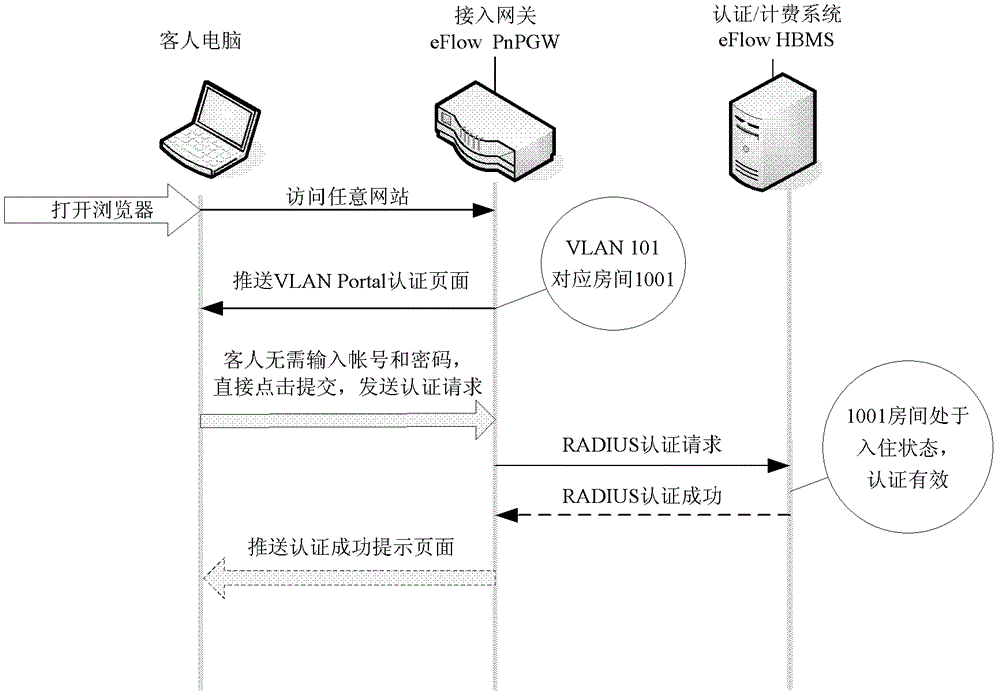
[0040] as attached figure 2 , this embodiment provides a VLAN Portal authentication method, which greatly simplifies the authentication process when a hotel guest accesses the wired network port of the guest room to surf the Internet.
[0041] When networking on the second floor, configure a unique 802.1Q VLAN number for the wired network port of each guest room, and configure other VLANs different from the wired network of the guest room for meeting rooms, business centers and other public wireless coverage areas. All VLANs are terminated at Access port of HSIA.
[0042] For example, in Room 1001, when a guest's computer or other terminal equipment is connected to the wired network port of the room, HSIA judges whether the access of the computer or other terminal equipment has passed the authentication and is within the set validity period:
[0043] If it has passed the authentication and is within the set validity period, then allow access to the network; otherwise, perfor...
Embodiment 2
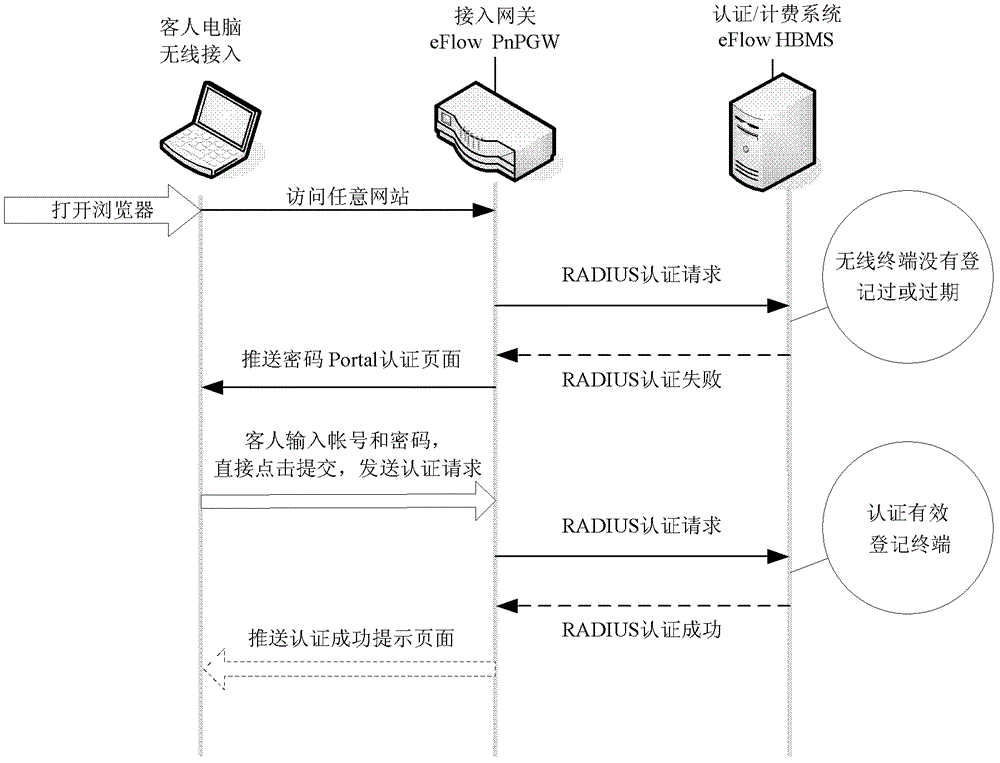
[0046] as attached image 3 , this embodiment provides a wireless network VLAN Portal authentication method.
[0047] When networking on the second floor, configure a unique 802.1Q VLAN number for the wired network port of each guest room, and configure other VLANs different from the wired network of the guest room for meeting rooms, business centers and other public wireless coverage areas. All VLANs are terminated at Access port of HSIA.
[0048] When a guest's computer or other terminal equipment accesses the wireless network port, HSIA judges whether the access of the terminal equipment has been authenticated and is within the set validity period:
[0049] If it has passed the authentication and is within the set validity period, then allow access to the network; otherwise, perform authentication,
[0050] HSIA pushes the Portal authentication page to the guest's computer or other terminal devices for password Portal authentication.
Embodiment 3
[0052] as attached Figure 4 , this embodiment provides a wired / wireless MAC authentication method for hotel guests.
[0053] When networking on the second floor, configure a unique 802.1Q VLAN number for the wired network port of each guest room, and configure other VLANs different from the wired network of the guest room for meeting rooms, business centers and other public wireless coverage areas. All VLANs are terminated at Access port of HSIA.
[0054] On the basis of Embodiment 1 or 2, further, after the guest computer or other terminal equipment is authenticated to access the wired / wireless network port, HSIA can record the MAC address of the guest computer or other terminal equipment wired / wireless network card, and make Authentication records, pushing the Portal authentication success page, the authentication system regularly updates and refreshes the MAC address within the validity period to the gateway, if the guest's computer is within the set validity period, such...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More