Android authority management method and system based on calling chain
A technology of rights management and call chain, applied in the direction of digital data authentication, etc., can solve problems such as application loss of rights, affecting normal operation, single consideration, etc., to avoid redundancy, avoid rights escalation attacks, and ensure the effect of terminal privacy and security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0052] The technical solutions in the embodiments of the present invention will be clearly and completely described below in conjunction with the accompanying drawings in the embodiments of the present invention. It should be understood that the described embodiments are only some of the embodiments of the present invention, not all of them. example. Based on the embodiments of the present invention, all other embodiments obtained by those skilled in the art without making creative efforts belong to the protection scope of the present invention.
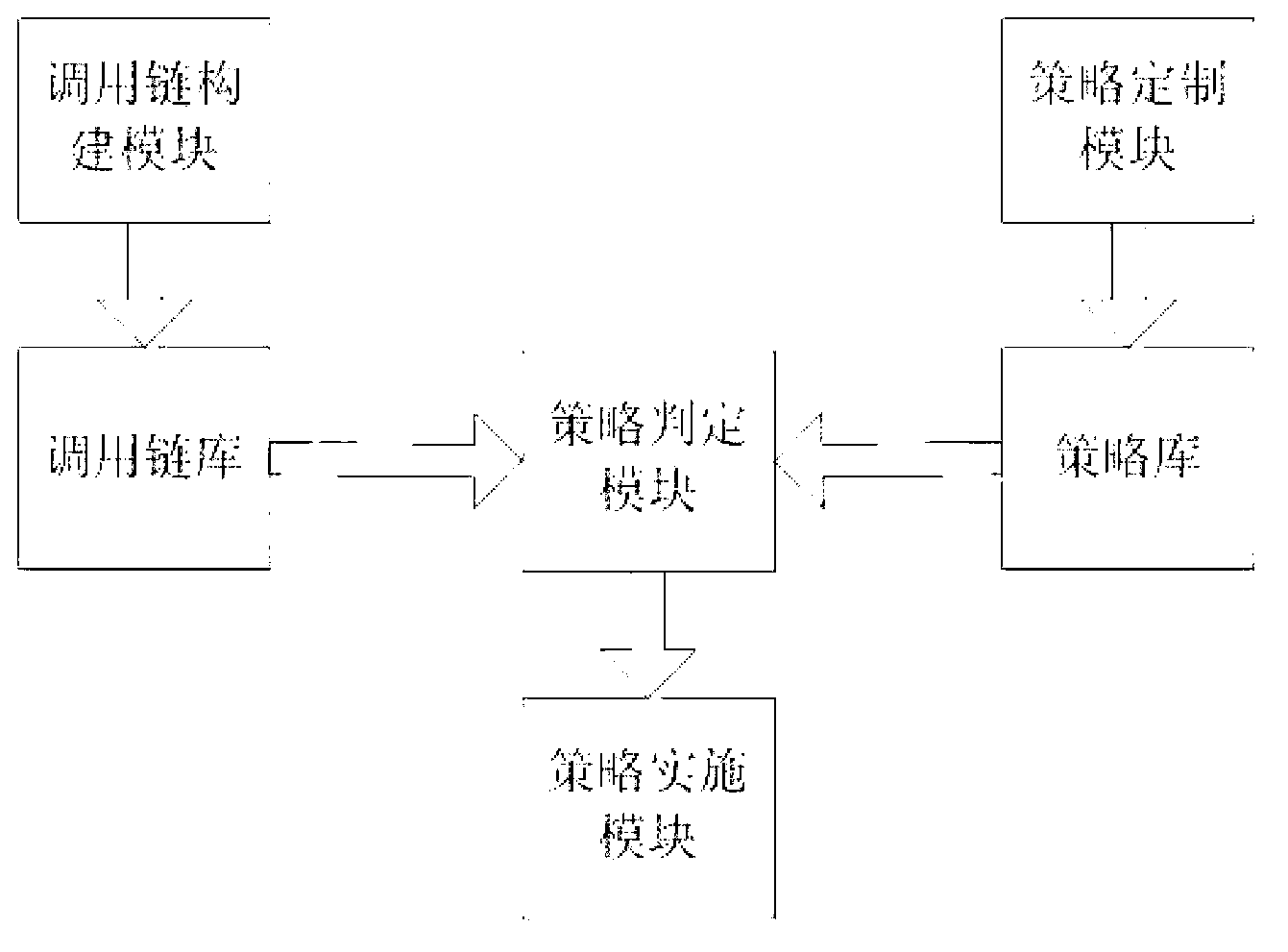
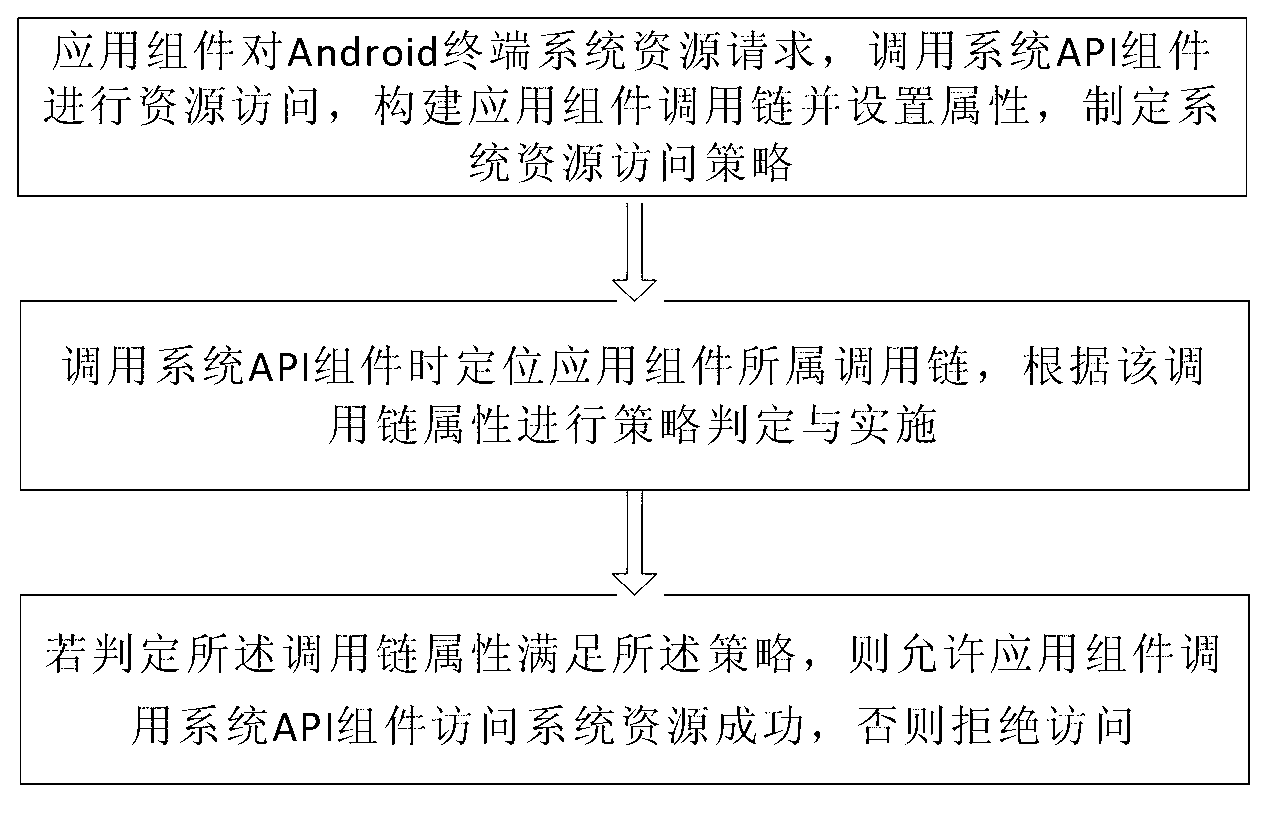
[0053] Such as figure 2 As shown, it is a schematic flow chart of the rights management method in the embodiment of the present invention. Embodiments will now be given to describe the method of the present invention in detail. The authority management method of the present invention mainly involves the following three links:
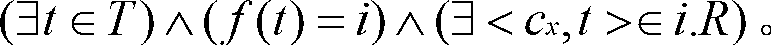
[0054] (1) Call chain construction. During the running of the application components, there will be a c...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More