Information hiding method based on local histogram
A histogram and partial technology, applied in the field of information security processing, can solve the problems of carrier distortion, small embedding capacity, and small embedding capacity of information hiding algorithm, so as to achieve the effect of improving embedding capacity and avoiding distortion
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0032] The present invention will be further described in detail below in conjunction with specific embodiments, which are explanations of the present invention rather than limitations.
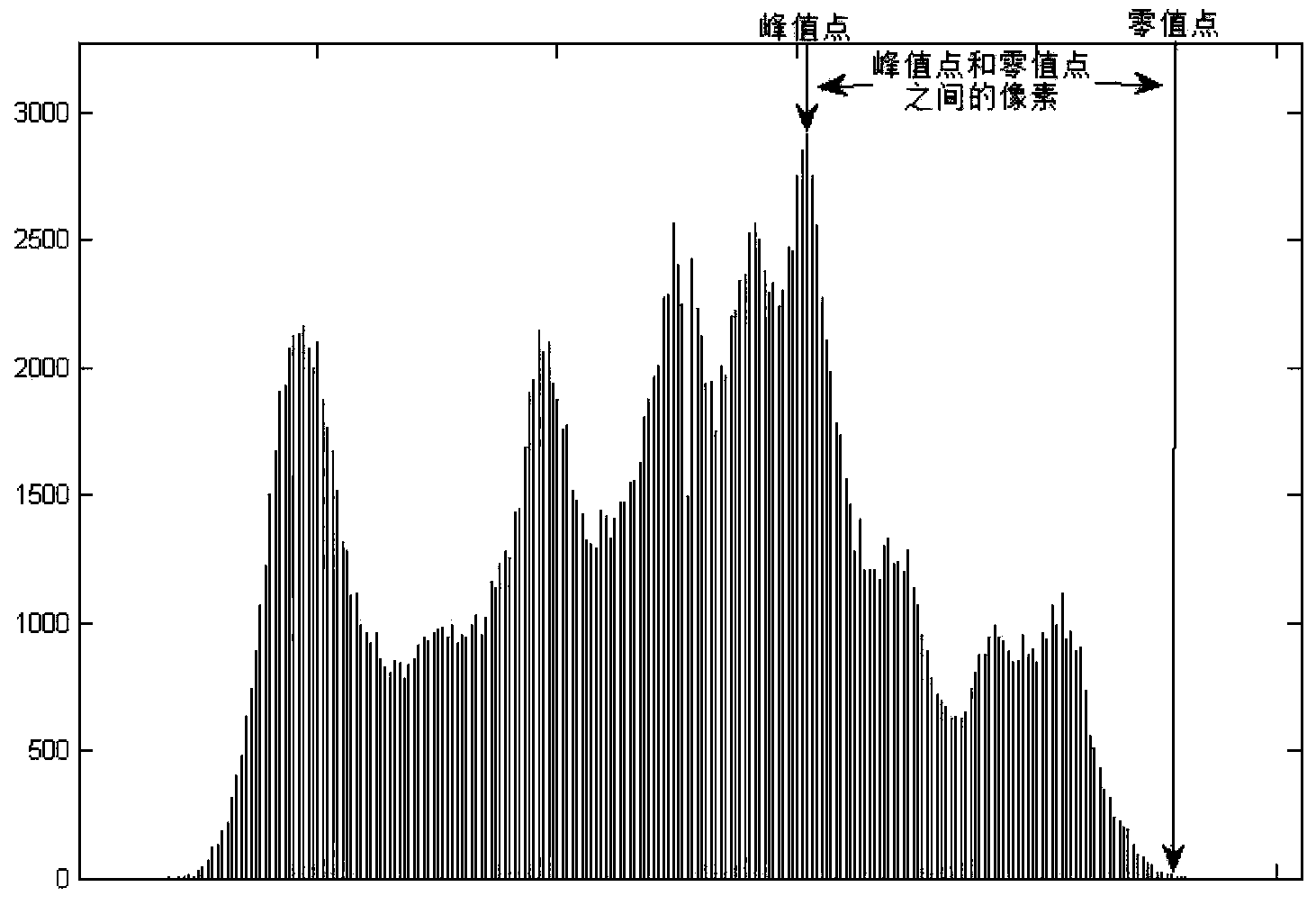
[0033] see image 3 and Figure 4 , the information embedding module of the present invention mainly uses boundary points and extreme value points to replace peak points and zero value points, and uses boundary points to carry out information embedding, where the boundary point information embedding is divided into single boundary point information embedding, and double boundary point information Embedding, the advantage of single boundary point information embedding is that the distortion of the carrier image is small, and the visual effect of the carrier image after embedding information is good; the advantage of double boundary point information embedding is that the embedding capacity is large, and which method to use for information embedding depends on actual needs. If the visual effec...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More