Method for acquiring linkage information in database safety audit
A technology for connecting information and security auditing, which is applied in the network field and can solve problems such as leaking secrets and generating security risks
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
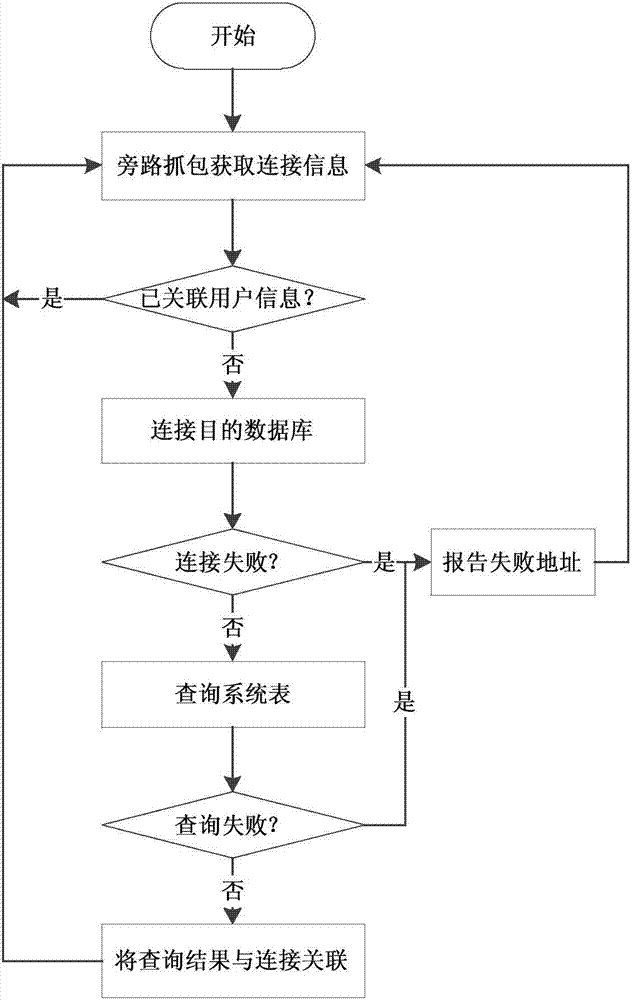
[0014] The following will clearly and completely describe the technical solutions in the embodiments of the present invention with reference to the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments are only some, not all, embodiments of the present invention. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without creative efforts fall within the protection scope of the present invention.
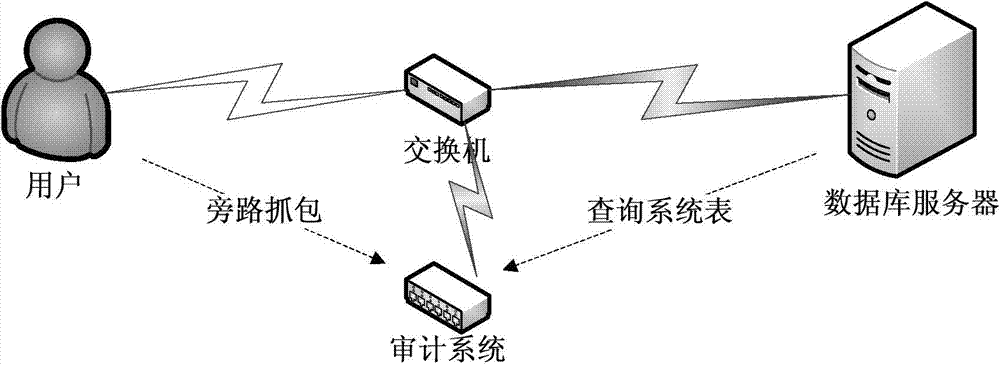
[0015] In order to solve the shortcomings or insufficiencies in the security of decrypting the connection information of the access database in the prior art, the present invention adopts a method of directly obtaining the connection information from the database and matching the existing connection, thereby realizing the effective identification of the connection user while ensuring security sex.
[0016] Principle of the present invention:
[0017] 1. The source...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More