A DEM Fragile Watermark Integrity Authentication Method Considering Terrain Features
A fragile watermark and terrain feature technology, applied in the field of geographic information security, can solve the problem that DEM data cannot be directly transplanted
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
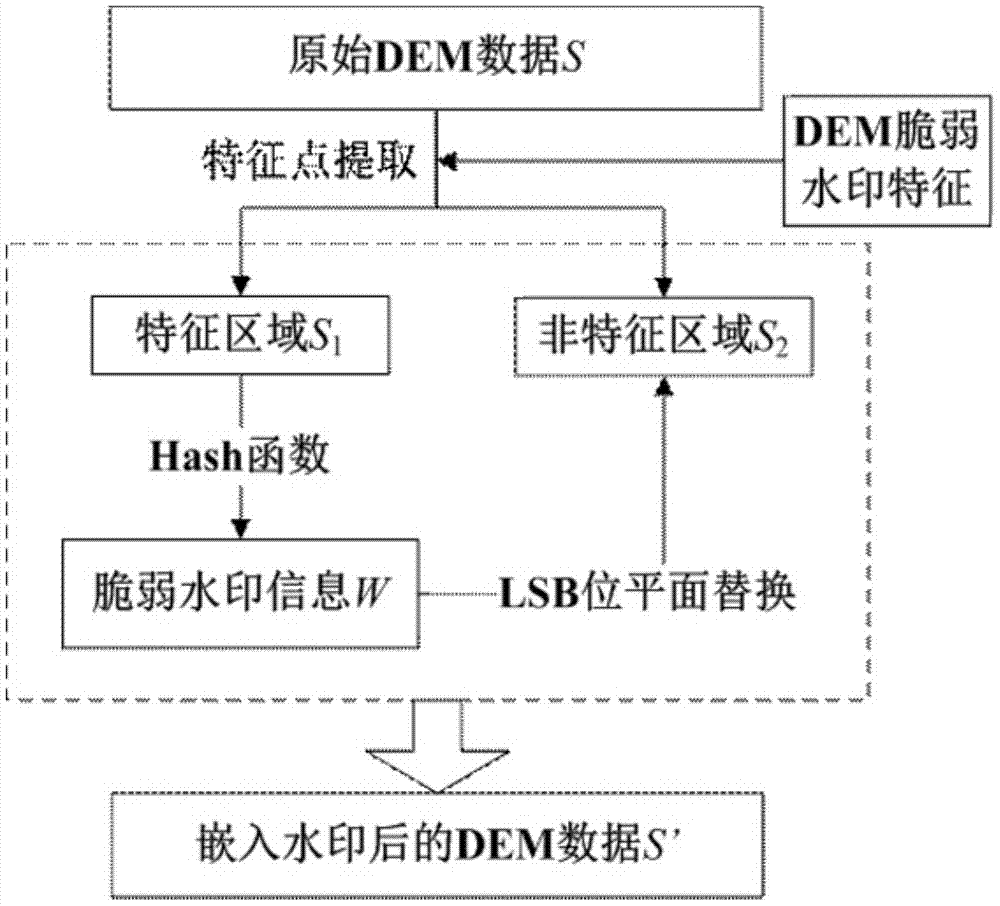
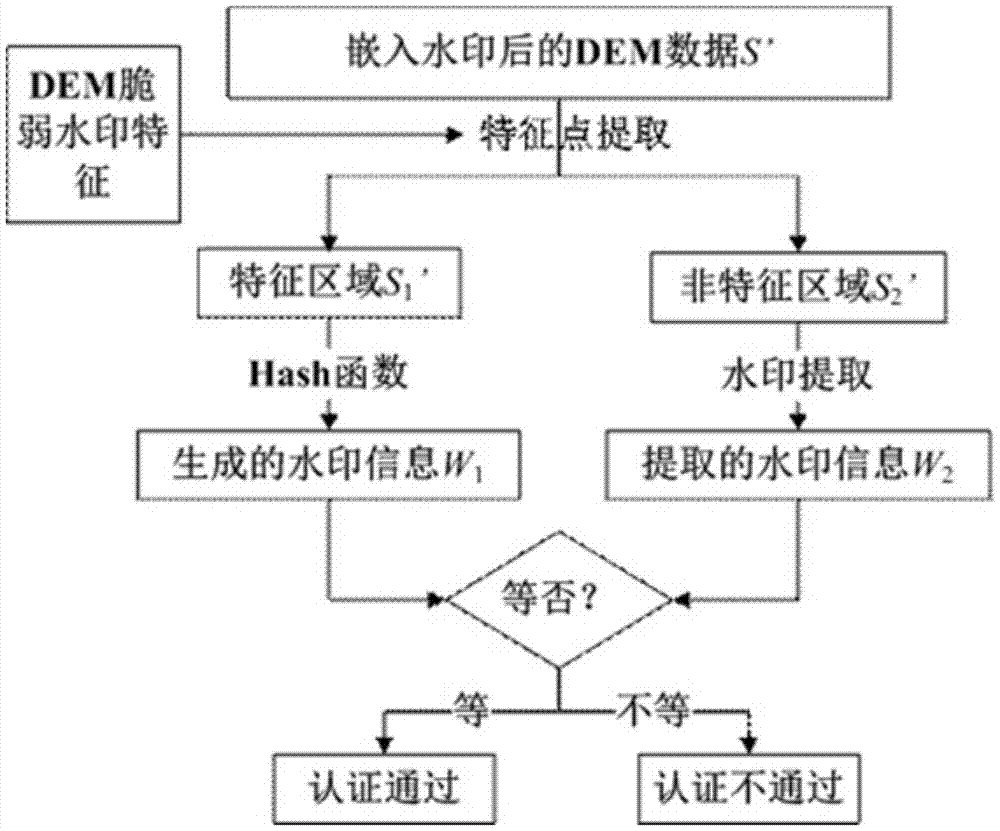
Method used
Image
Examples
Embodiment Construction
[0043] The present invention will be described in further detail below in conjunction with the accompanying drawings and embodiments.
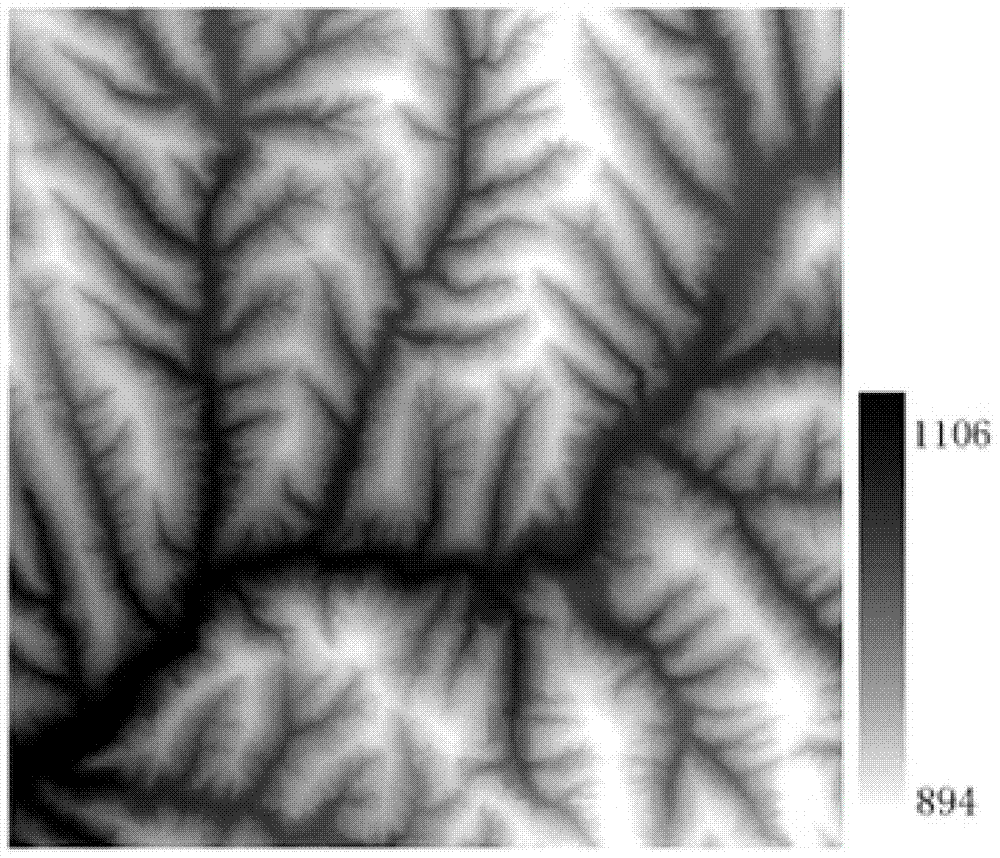
[0044] Select a 1:10,000 grid DEM experimental data with a size of 509×515, a resolution of 5m, and floating-point elevation data ( image 3 ), for the whole process of watermark information generation, embedding and detection, an embodiment of the method of the present invention is given, and the present invention is further described in detail.
[0045] 1. Watermark information generation:
[0046] Step 1: Select the integer part of the DEM data to be embedded in the watermark, use the D8 algorithm to extract the terrain feature points of the data, and obtain the feature area and non-feature area of the data;
[0047] Step 2: Perform MD5 Hash calculation on the extracted data feature area to obtain the watermark sequence to be embedded.
[0048] 2. Watermark information embedding:
[0049] Step 1: Perform binary conversion on the two di...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More