User autonomy-based identity authentication implementation method
A technology of identification authentication and user identification, applied in the field of identification authentication system, can solve the problems of no unified management, application restrictions, complex key relationship, etc., and achieve the effect of simple structure and strong anti-attack ability.
Inactive Publication Date: 2015-09-09
赵捷 +1
View PDF4 Cites 15 Cited by
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
The main problem of this system is that it is a completely independent and open system without unified management, resulting in complex key relationships, it is difficult to prove the authenticity of the public key subject, and the application is greatly restricted
Method used
the structure of the environmentally friendly knitted fabric provided by the present invention; figure 2 Flow chart of the yarn wrapping machine for environmentally friendly knitted fabrics and storage devices; image 3 Is the parameter map of the yarn covering machine
View moreImage
Smart Image Click on the blue labels to locate them in the text.
Smart ImageViewing Examples
Examples
Experimental program
Comparison scheme
Effect test
Embodiment Construction
[0082] The above descriptions are only preferred embodiments of the present invention, and are not intended to limit the present invention. Obviously, those skilled in the art can make various changes and modifications to the present invention without departing from the spirit and scope of the present invention. Thus, if these modifications and variations of the present invention fall within the scope of the claims of the present invention and their equivalent technologies, the present invention also intends to include these modifications and variations.
the structure of the environmentally friendly knitted fabric provided by the present invention; figure 2 Flow chart of the yarn wrapping machine for environmentally friendly knitted fabrics and storage devices; image 3 Is the parameter map of the yarn covering machine
Login to View More PUM
 Login to View More
Login to View More Abstract
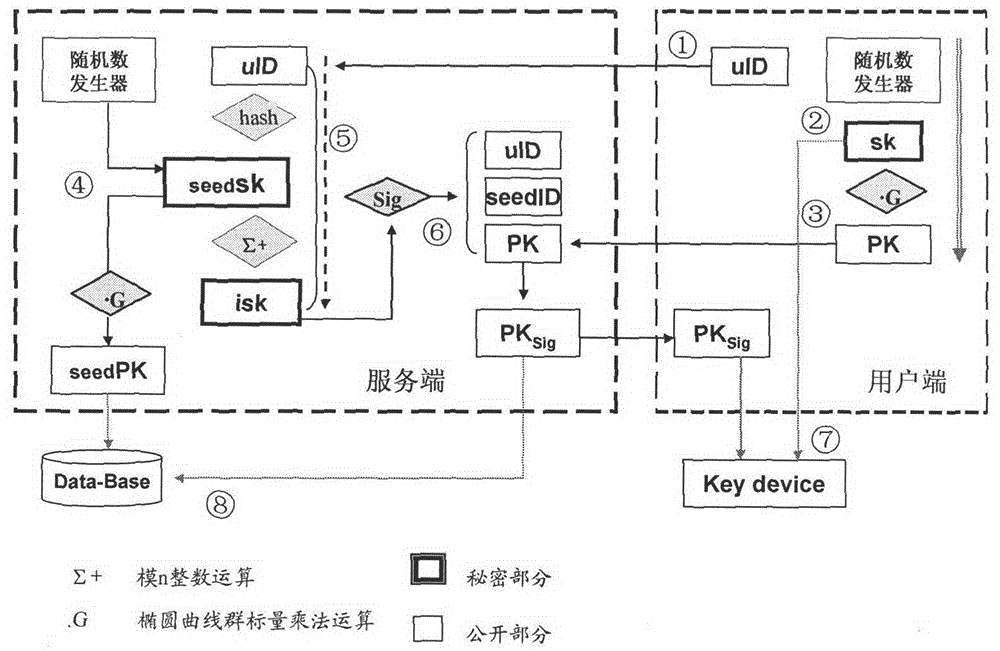
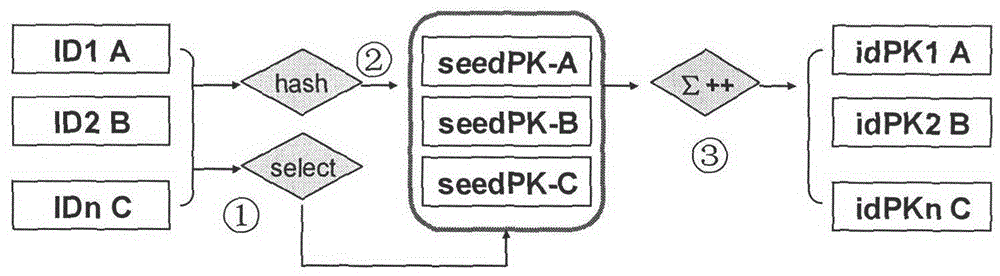
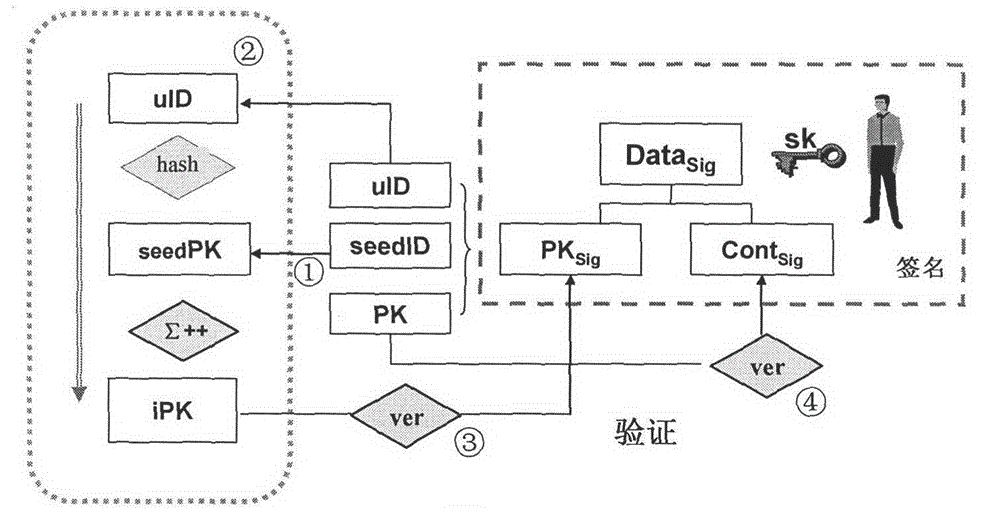
The invention discloses a user autonomy-based identity authentication implementation method. In a system, both an identity and a key are defined by a user, and real-name and anonymous authentication, and autonomous control and management of the key are supported; a user public key is digitally signed and verified through generation of a user identity key with a seed key, so that binding and proving of the user identity and the key are realized; and direct cross-domain cross authentication among different trust domain users is realized through construction and management of a seed pubic key set. The system is simple, flexible and suitable for anonymous authentication, supports real-time authentication, and can be used for constructing a diversified identity-based authentication service system.
Description
technical field [0001] The invention relates to an identification authentication system, provides a method for realizing an identification authentication system based on user autonomy, and belongs to the technical field of cyber security. Background technique [0002] As network and information technology gradually enter people's production and life, protecting the authenticity, privacy, and responsibility (non-repudiation) of information has become a common concern of the government and society. In view of the fact that all entities in real space in cyberspace are also the main body of information activities, and they are all expressed in abstract signs. By binding the signs and entities through authentication technology, building a sign authentication system that supports digital signature and key exchange has become an important way to realize the Internet. The foundation of security (cyberspace security). At the same time, according to the provisions of the Electronic S...
Claims
the structure of the environmentally friendly knitted fabric provided by the present invention; figure 2 Flow chart of the yarn wrapping machine for environmentally friendly knitted fabrics and storage devices; image 3 Is the parameter map of the yarn covering machine
Login to View More Application Information
Patent Timeline
 Login to View More
Login to View More IPC IPC(8): H04L9/32H04L9/30
Inventor 赵捷陈晰
Owner 赵捷