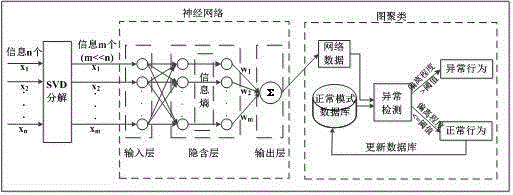
User abnormal behavior detection method based on neural network clustering
A neural network and behavioral technology, applied in the field of information security credibility, can solve problems such as high false alarm rate, achieve the effect of improving decomposition speed and signal-to-noise ratio
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
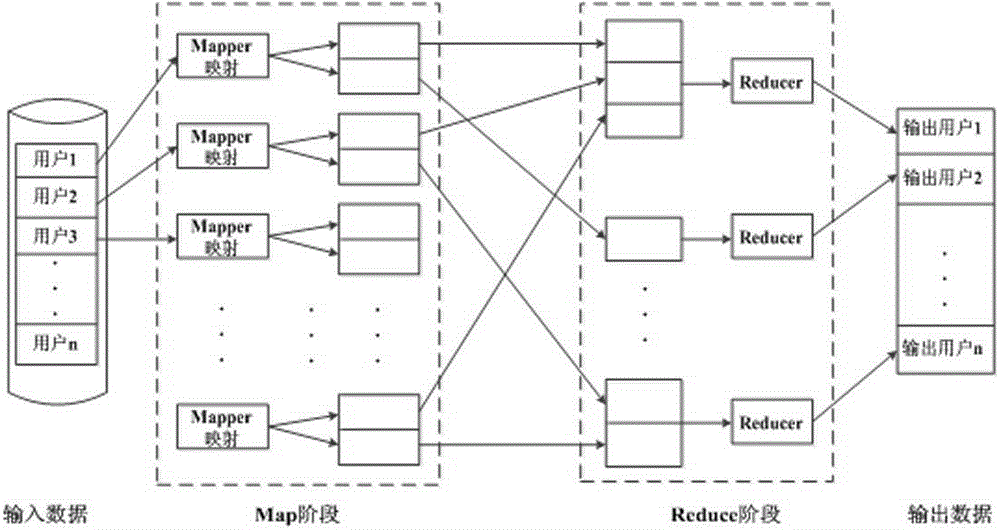
Method used
Image
Examples
Embodiment Construction
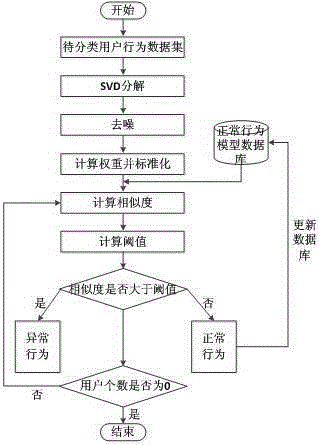
[0028] As shown in the figure, a method for detecting abnormal user behavior based on neural network clustering is characterized in that it includes the following steps:
[0029] Step 1. Assuming that each user is an object, the behavior data of the object is used as the attribute of the object, and the matrix real matrix A of n*m dimensions is expressed as an object-attribute structure, and the matrix A is expressed as ,in, Expressed as the jth attribute of the ith object;
[0030] Step 2. Use the matrix A in step 1 to use the formula A=USV T Perform SVD decomposition, where U=(u 1 ,u 2 ,...,u m ), V=(v 1 ,v 2 ,...,v n ), , , (i=1,2,...,r), for A T All the non-zero eigenvalues of A, arranged in descending order, are the singular values of A;
[0031] Step 3. Calculate the effective rank order of the decomposed SVD matrix according to the following formulas (1)-(3) to denoise user behavior information
[0032] (1),
[0033] (2),
[0034] (3), wh...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More