Protection method of mobile security data
A technology of secure data and public parameters, applied in secure communication devices, digital transmission systems, user identity/authority verification, etc., can solve problems such as illegal user revocation identity-based encryption system problems, achieve revocation problems and improve security Effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0018] The present invention will be further described below in conjunction with the accompanying drawings.
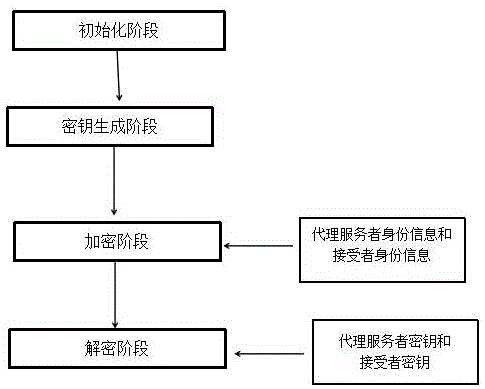
[0019] A method for protecting mobile security data, the specific steps are as follows:
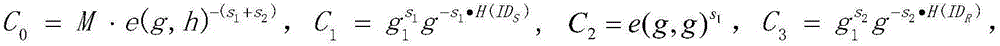
[0020] (1) Initialization phase: a trusted central organization inputs a security parameter Apply the bilinear group generation algorithm to generate bilinear groups of prime order (e,p,G,G T ). Suppose g, h are the generators of the cyclic group G, H is a collision-resistant hash function, Z p is a finite field composed of modules. The central organization randomly selects α∈z p , and calculate g 1 =g α . The master key of the system is α, and the public parameters are (e,p,G,G T ,g,g 1 , h).
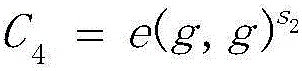
[0021] (2) Key generation phase: when user U uses identity ID U When joining the system, the central agency first verifies the legitimacy of its identity, and then randomly selects r U ∈ z p ,calculate User U's key is SK U =(r U ,h U ). The central authority will send t...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com