Secure memory data protection method and device
A technology for storing data and protecting devices, applied in the field of information security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0041] In order to make the object, technical solution and advantages of the present invention more clear, the present invention will be further described in detail below in conjunction with the examples. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
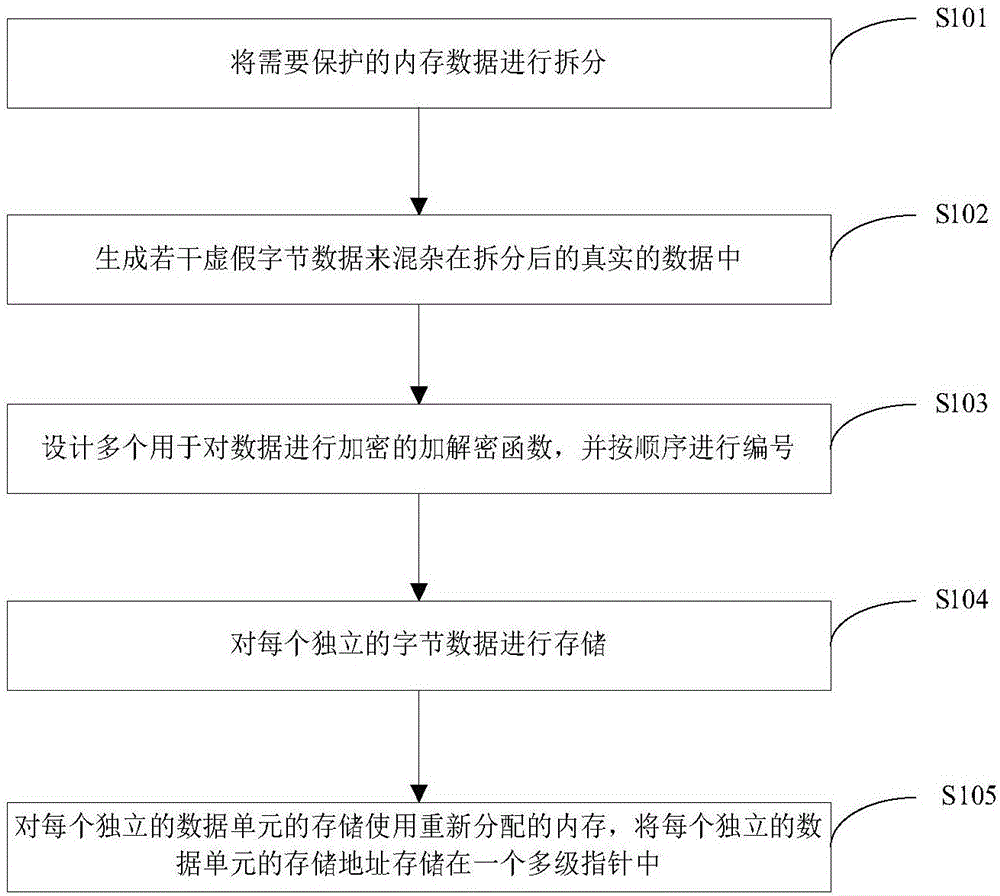
[0042] Such as figure 1 As shown, a safe memory data protection method includes the following steps:
[0043] S101) splitting the memory data to be protected into independent byte data one by one;
[0044] The data protection algorithm of this application will disassemble the entire data into individual bytes, and each independent byte will be encrypted and stored separately;
[0045] S102) Generate some false byte data and mix in the real data split in the previous step;
[0046] This application generates some fake data to be mixed with the real data, so that it becomes more difficult to call out the real data separate...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More