Trusted device management method based on decentralized network
A device management and decentralization technology, applied in data exchange network, secure communication device, user identity/authority verification, etc., can solve problems such as low security protection strength and lack of flexibility in management
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0034] All features disclosed in this specification, or steps in all methods or processes disclosed, may be combined in any manner, except for mutually exclusive features and / or steps.
[0035] Any feature disclosed in this specification, unless specifically stated, can be replaced by other alternative features that are equivalent or have similar purposes. That is, unless expressly stated otherwise, each feature is one example only of a series of equivalent or similar features.
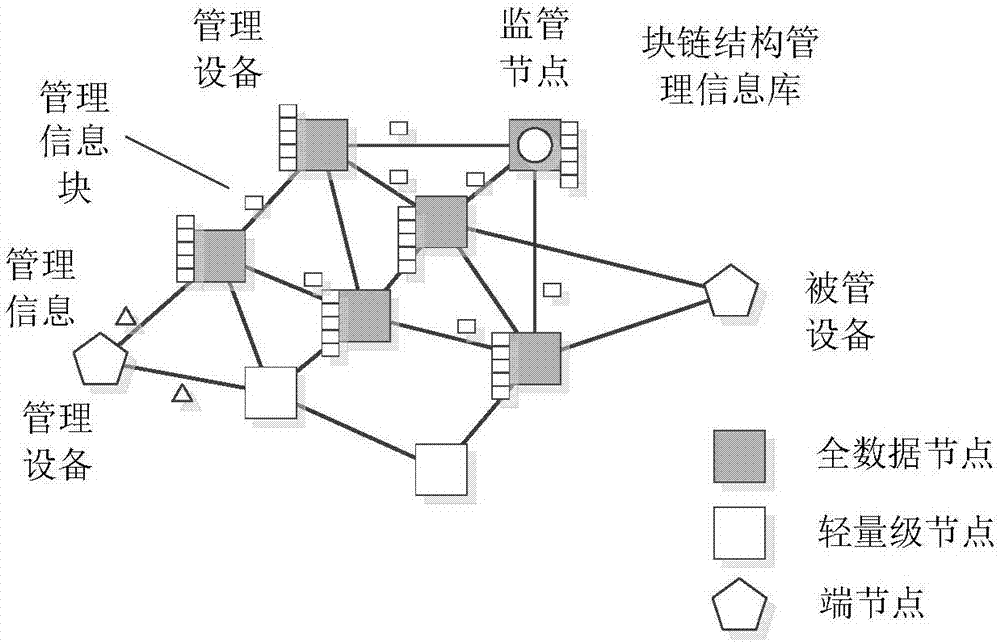
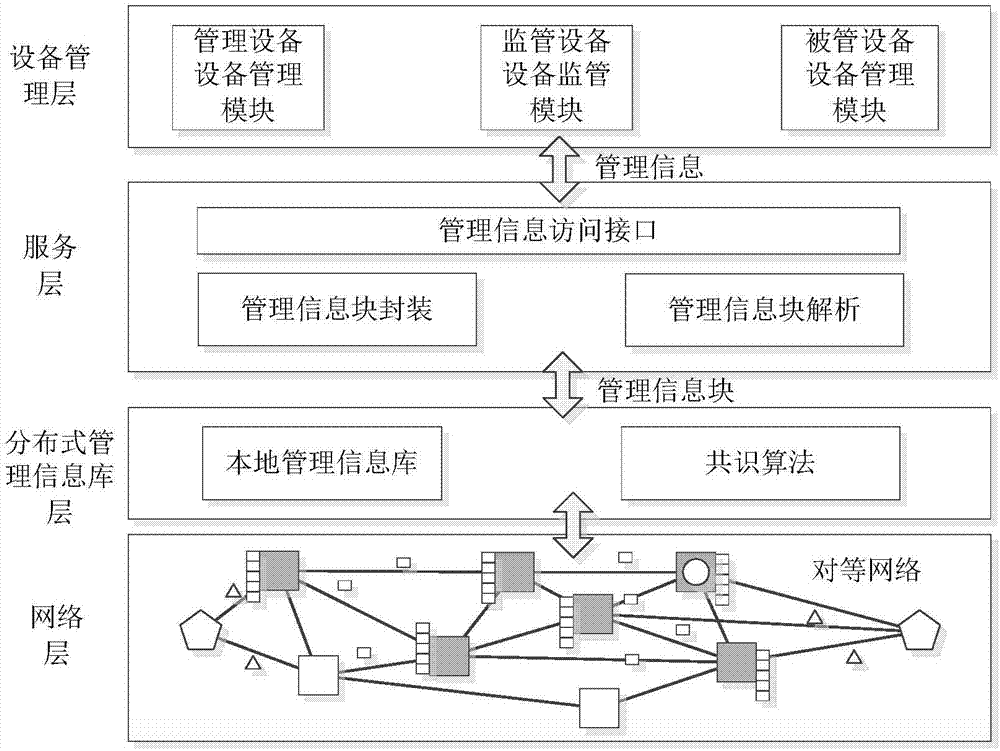
[0036] (1) Device management network construction
[0037] All nodes participating in device management form a peer-to-peer network including nodes with different roles according to the P2P protocol; each node forwards management information or management information blocks to its adjacent nodes according to role requirements and policies;
[0038] Nodes in the network have a public-private key pair and an address generated by the public key.
[0039] The management node uses a cryptographic algorit...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More