A lightweight BLE wearable device security authentication method
A wearable device, security authentication technology, applied in security devices, digital data authentication, computer security devices, etc., can solve problems such as increasing the hardware cost and development cost of wearable devices
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0025] The present invention will be further described below in conjunction with the accompanying drawings and specific embodiments.
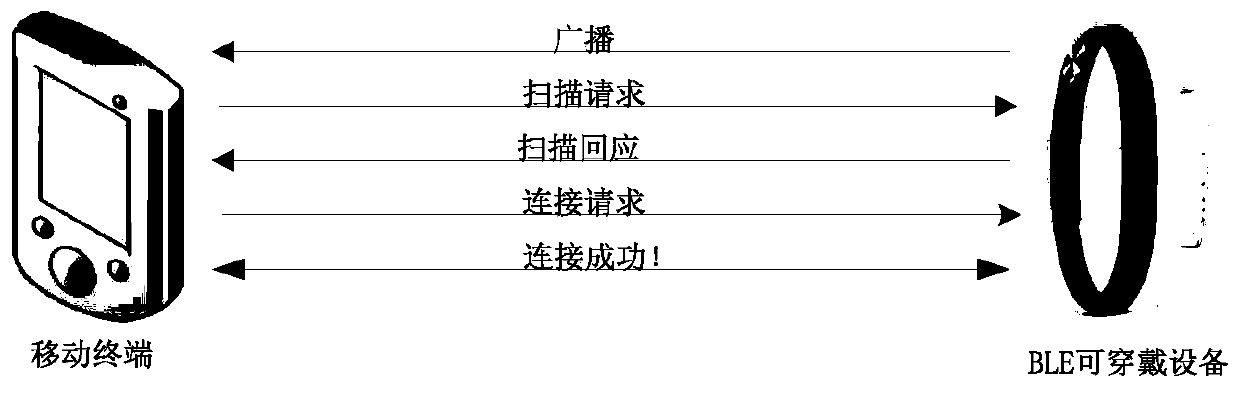
[0026] During the use of the existing BLE wearable device, it needs to work with other mobile terminals to process the data recorded in the BLE wearable device. Therefore, the device security authentication method of the present invention is based on the information interaction between the BLE wearable device and the mobile terminal, such as figure 1 . After the device connection is established, it needs to be authenticated according to the authentication method of the present invention. Here, the entire security authentication is divided into two stages: the initial connection security authentication stage, and the reconnection security authentication stage.
[0027] In the initial connection security authentication stage, that is, at this time, the BLE wearable device does not perform any security settings, and the BLE wearable device and m...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More