Automatic loophole classification method based on word frequency statistics and simple Bayesian fusion model
A fusion model and Bayesian technology, applied in the field of information security, can solve problems such as classification accuracy needs to be improved
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0125] The technical solutions of the present invention will be described in detail below in conjunction with the accompanying drawings and embodiments.
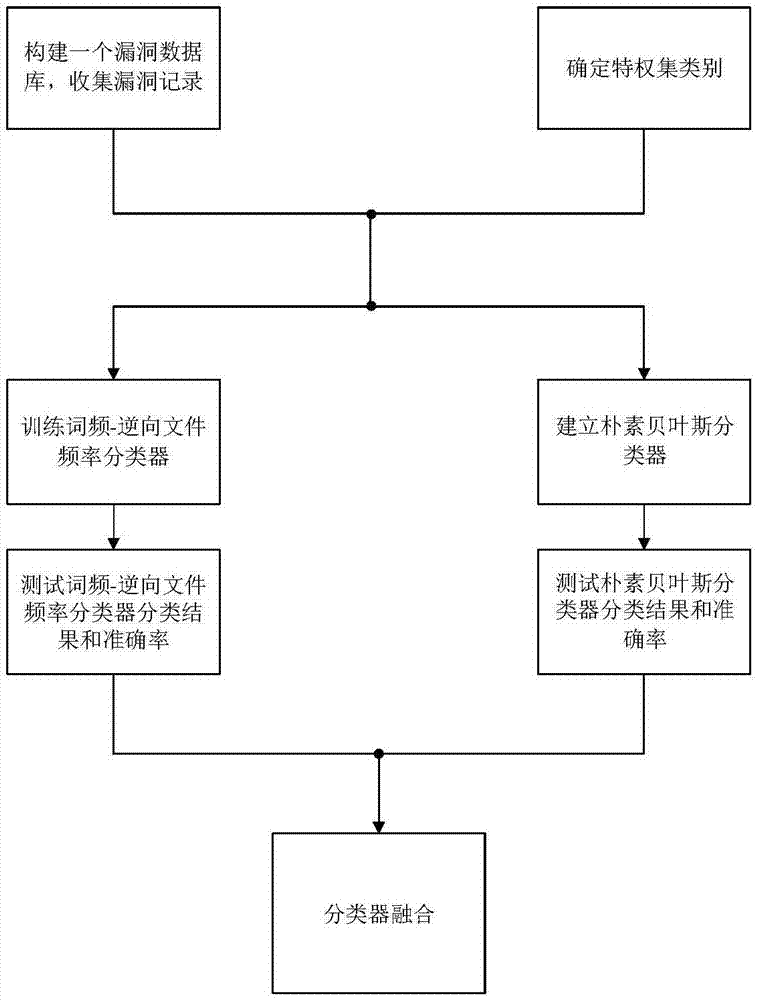
[0126] Using the vulnerability automatic classification method proposed by the present invention based on word frequency-reverse file frequency and naive Bayesian fusion model to classify vulnerabilities and obtain the operation process of the relationship between the vulnerabilities is as follows figure 1 As shown, the specific operation steps are:
[0127] Step 1. Build a vulnerability database, download the vulnerability data from 2010 to 2016 from the National Vulnerability Database (NVD), select the vulnerability data under linux and filter the fields and import it into the local database.
[0128] The fields of the local vulnerability database are shown in Table 1.
[0129] Table 1 Vulnerability database field table
[0130] Field Name
Chinese name
field source
CVE_ID
Common Vulnerability ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More