Identity-based generalized multi-recipient anonymous signcryption method
A multi-receiver, receiver technology, applied in the field of identity-based generalized multi-receiver anonymous signcryption
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
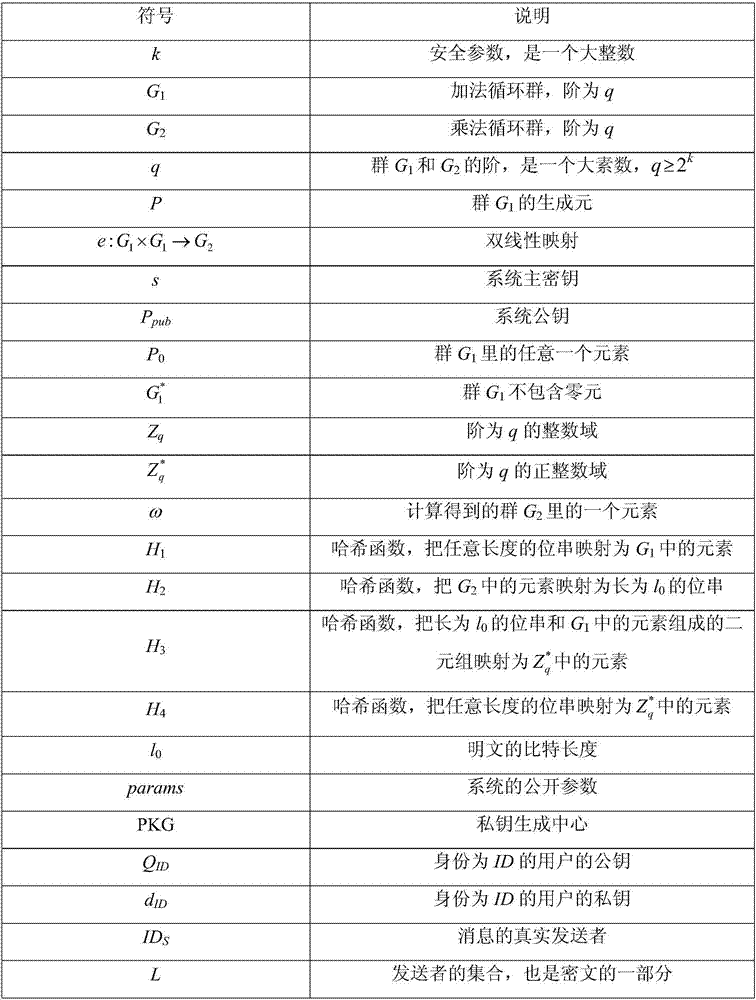
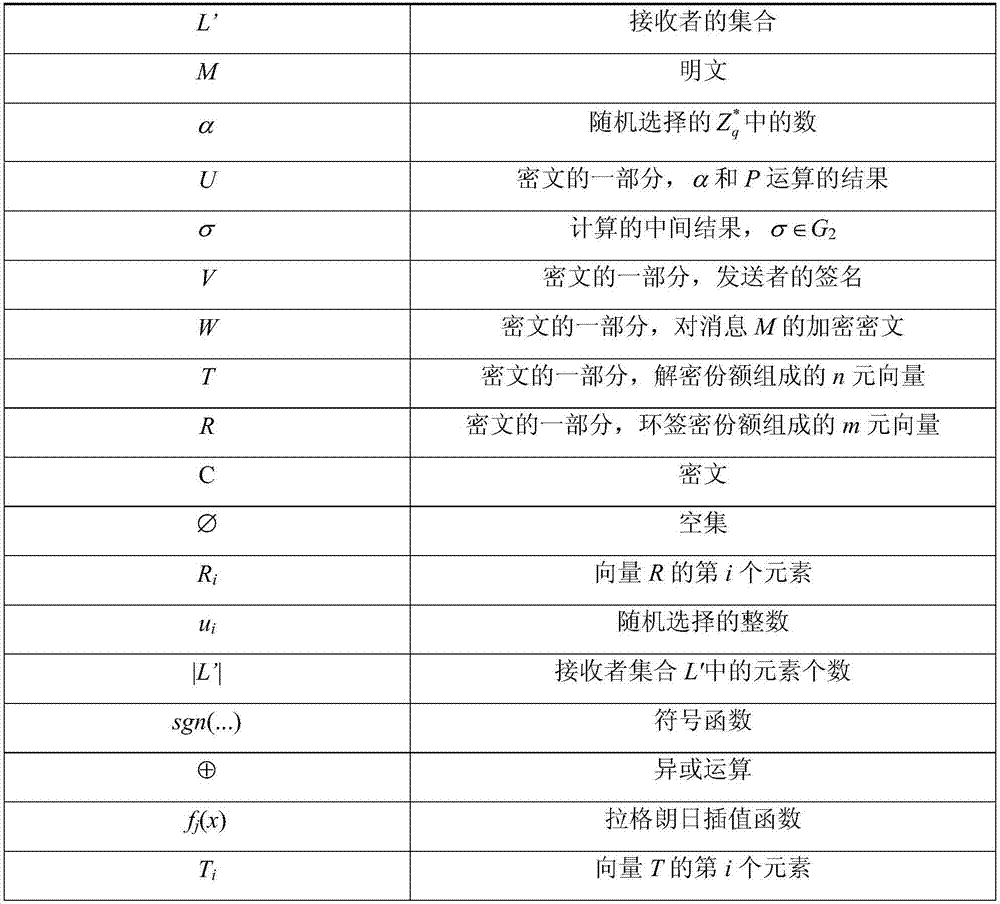
[0048] Symbolic descriptions of variables and operations in this embodiment.
[0049]
[0050]
[0051] This example implements an identity-based generalized multi-receiver anonymous signcryption method for the application occasion of group-oriented cloud service customization. The present invention will be described in detail below:
[0052] The specific steps of the identity-based generalized multi-receiver anonymous signcryption method of the present invention are as follows:
[0053] Step 1: Establish system parameters. This step is performed by a private key generation center (Private Key Generator, PKG).
[0054] Choose security parameter k, let G 1 and G 2 are additive cyclic groups and multiplicative cyclic groups of order q, respectively, where q≥2 k is a prime number, let P be G 1 The generator of , choose a bilinear map e:G 1 ×G 1 →G 2 ; choose an integer at random As the system master key, let P pub =sP∈G 1 is the system public key. In addition, ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More