Partially blind signature method based on identity on lattice
A partially blind, identity technology, applied in the field of information security, to achieve the effect of improving computing efficiency and computing efficiency
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
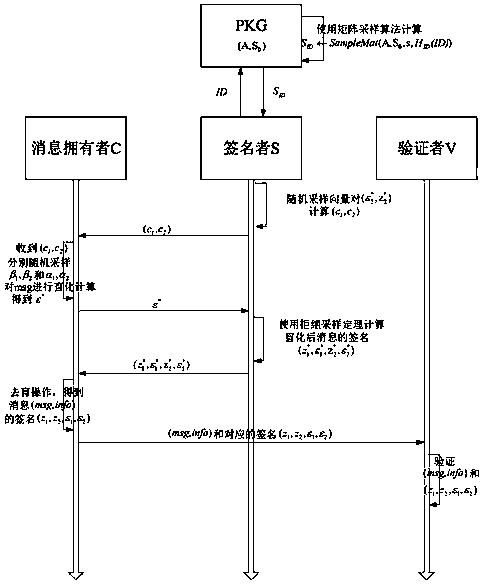
[0021] The present invention will be further described below in conjunction with embodiment and accompanying drawing.
[0022] The present invention is divided into four stages: a Setup (establishment) stage, a KeyGen (key establishment) stage, an Issue (release) stage, and a Verify (verification) stage. The method includes 3 cryptographic hash functions: H msg :{0,1} * →{-1,0,1} k ,
[0023] Setup: private key generator PKG (private key generator), with the security parameter λ as input, using the trapdoor generation algorithm TrapGen(1 λ ) generating matrix and the corresponding short base in is the system master key, and A is the system public key.
[0024] KeyGen: PKG using own private key S 0 , and the received identity information ID, and the system public parameter Param={n,m,A,q,s,k,H ID ,H msg ,H info}, where s is the sampling standard deviation, using the matrix sampling algorithm SampleMat(A,S 0 ,s,H ID (ID)) output the private key corresponding to...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com