A method and device for securely processing network data streams
A security processing and data flow technology, which is applied in the field of network data flow security processing, can solve the problem of being unable to block malicious applications, achieve the effects of reducing response time, improving visualization, and solving static identification
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0040] The specific embodiments of the present invention will be further described below in conjunction with the accompanying drawings. The following examples are only used to illustrate the technical solution of the present invention more clearly, but not to limit the protection scope of the present invention.
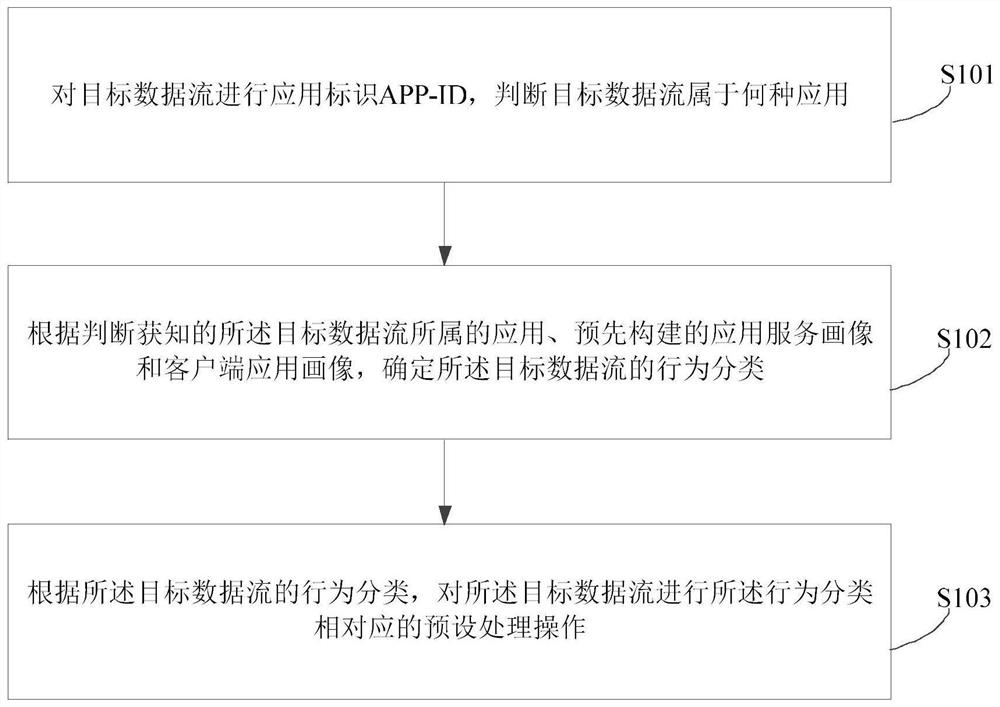
[0041] figure 1 It shows a schematic flowchart of a method for securely processing network data streams provided by an embodiment of the present invention, as shown in figure 1 As shown, the security processing method of the network data flow in this embodiment includes:
[0042] S101. Perform an application identification APP-ID on the target data flow, and determine which application the (network) target data flow belongs to.
[0043] Specifically, according to the characteristic value of the data of the application, the decryption and encryption of the TLS (Transport Layer Security) / SSL (Secure Sockets Layer) protocol and SSH (File Transfer Protocol), and the dec...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More