Malicious code behavior feature extraction method
A malicious code and feature extraction technology, applied in the field of malicious code behavior feature extraction, can solve problems such as increasing the difficulty of malicious code detection, and achieve accurate representation, accurate analysis and detection
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0025] All features disclosed in this specification, or steps in all methods or processes disclosed, may be combined in any manner, except for mutually exclusive features and / or steps.
[0026] Any feature disclosed in this specification (including any appended claims, abstract and drawings), unless expressly stated otherwise, may be replaced by alternative features which are equivalent or serve a similar purpose. That is, unless expressly stated otherwise, each feature is one example only of a series of equivalent or similar features.
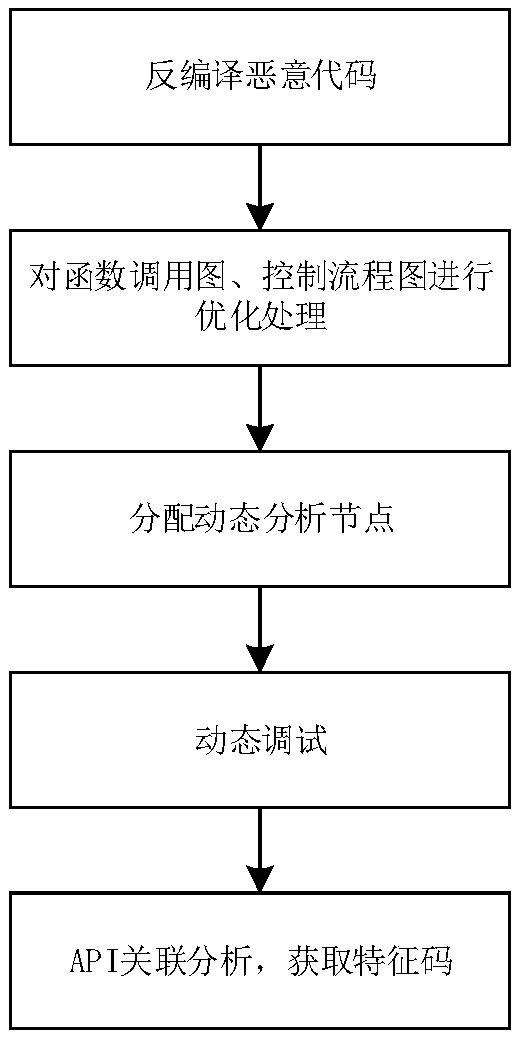
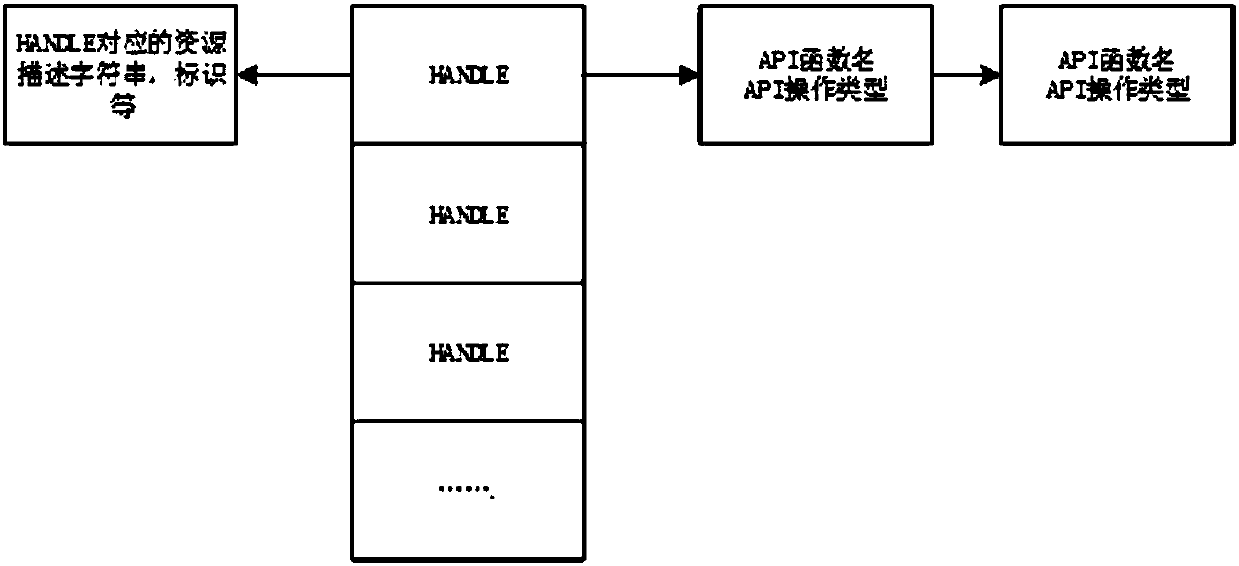
[0027] The specific implementation manners of the present invention will be described in detail below in conjunction with the drawings and embodiments.
[0028] In the following detailed description, numerous specific descriptions are set forth for purposes of explanation in order to provide a thorough understanding of the disclosed embodiments, however, it can be evident that one or more embodiments can be practiced without these specific des...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More