A ransomware defense method and system
A software and operating system technology, applied in instruments, computing, electrical and digital data processing, etc., can solve problems such as loss, and achieve the effect of ensuring zero loss, less system consumption, and protecting data and property safety.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0035] In order to enable those skilled in the art to better understand the technical solutions in the embodiments of the present invention, and to make the purpose, features and advantages of the present invention more obvious and easy to understand, the technical core of the present invention will be further described in detail below in conjunction with the accompanying drawings and examples instruction of.
[0036] In the present invention, a set of reliable and effective ransomware defense system is designed, which can effectively solve the above-mentioned existing problems, and the system includes as follows:
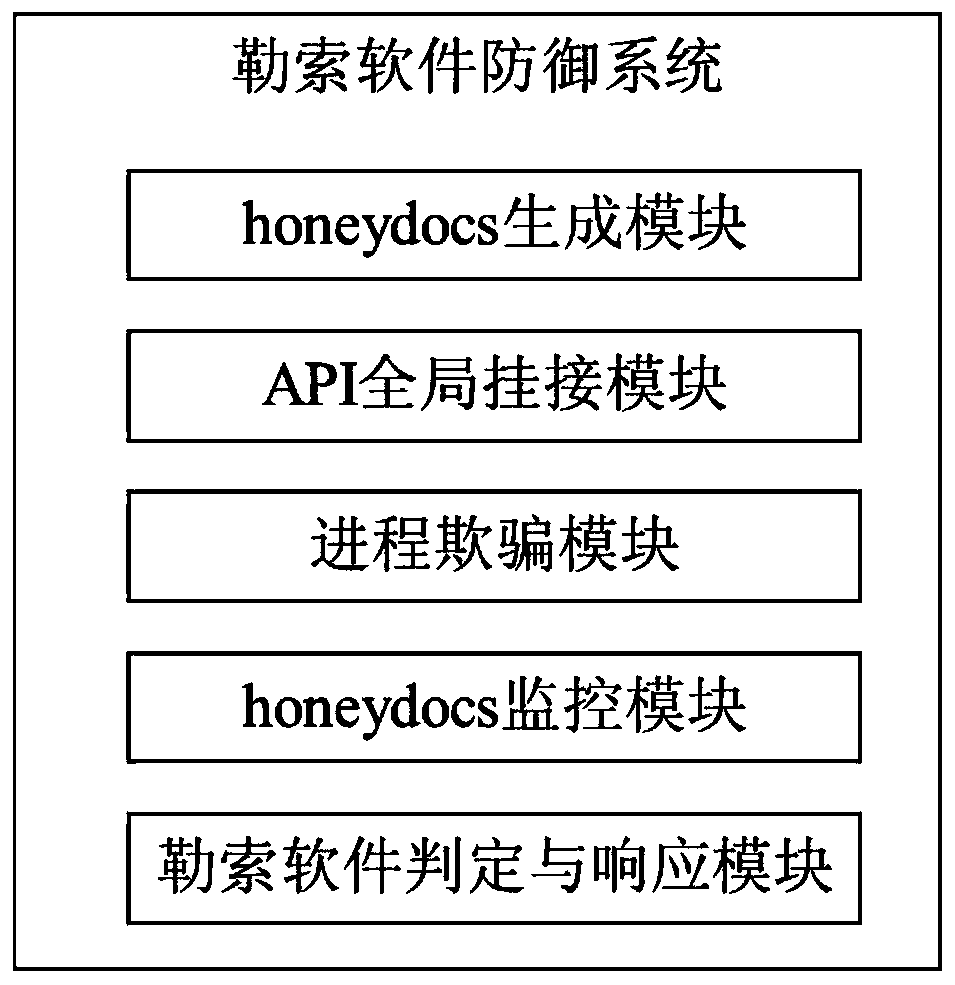
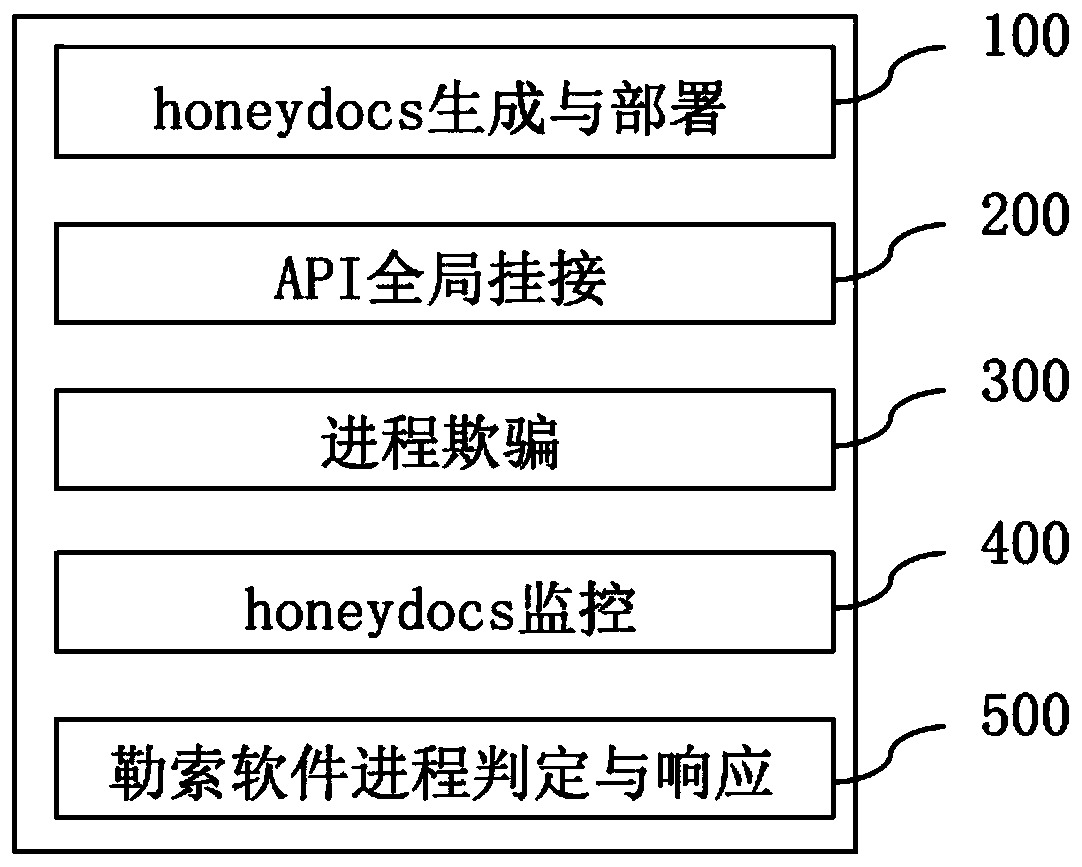
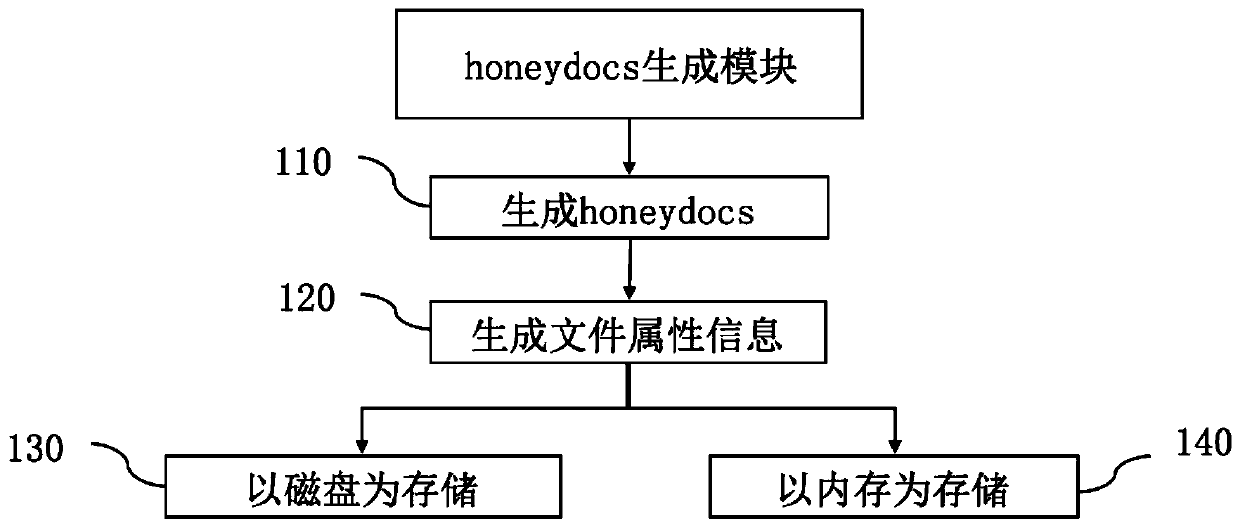
[0037] Such as figure 1 As shown, it is a schematic diagram of the module composition of the system. The system is divided into five modules, which are the honeydocs generation module (that is, the fraudulent data generation module), the API global mount module, the process fraudulent module, and the honeydocs monitoring module (that is, the fraudulent data monitor...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More