Implementation method for memory data encryption protection
A data encryption and implementation method technology, applied in the direction of digital data protection, electronic digital data processing, internal/peripheral computer component protection, etc., can solve the problems of low encryption performance, etc., to solve data theft, ensure encryption, area The effect of low power consumption
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0023] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings and embodiments. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
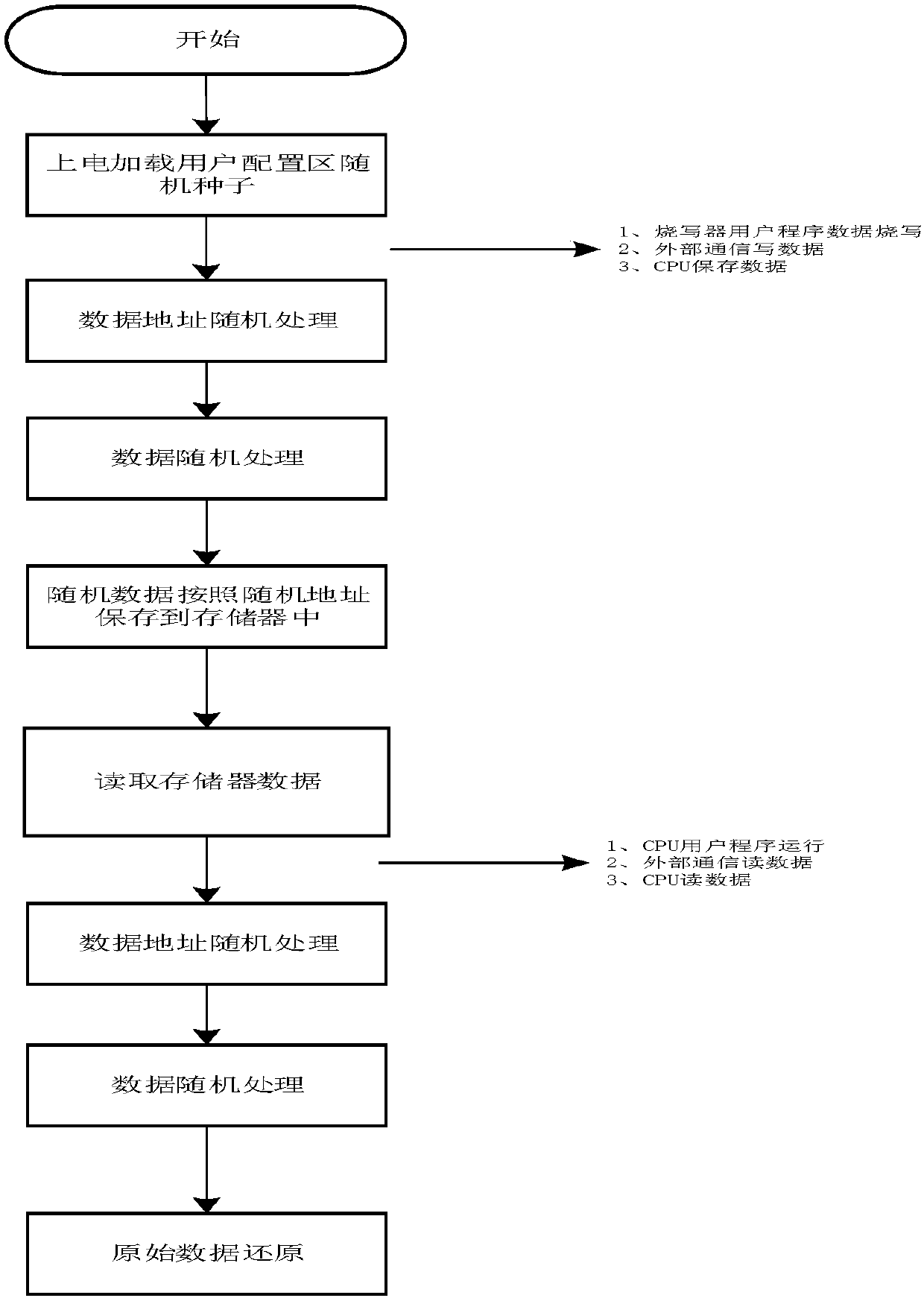
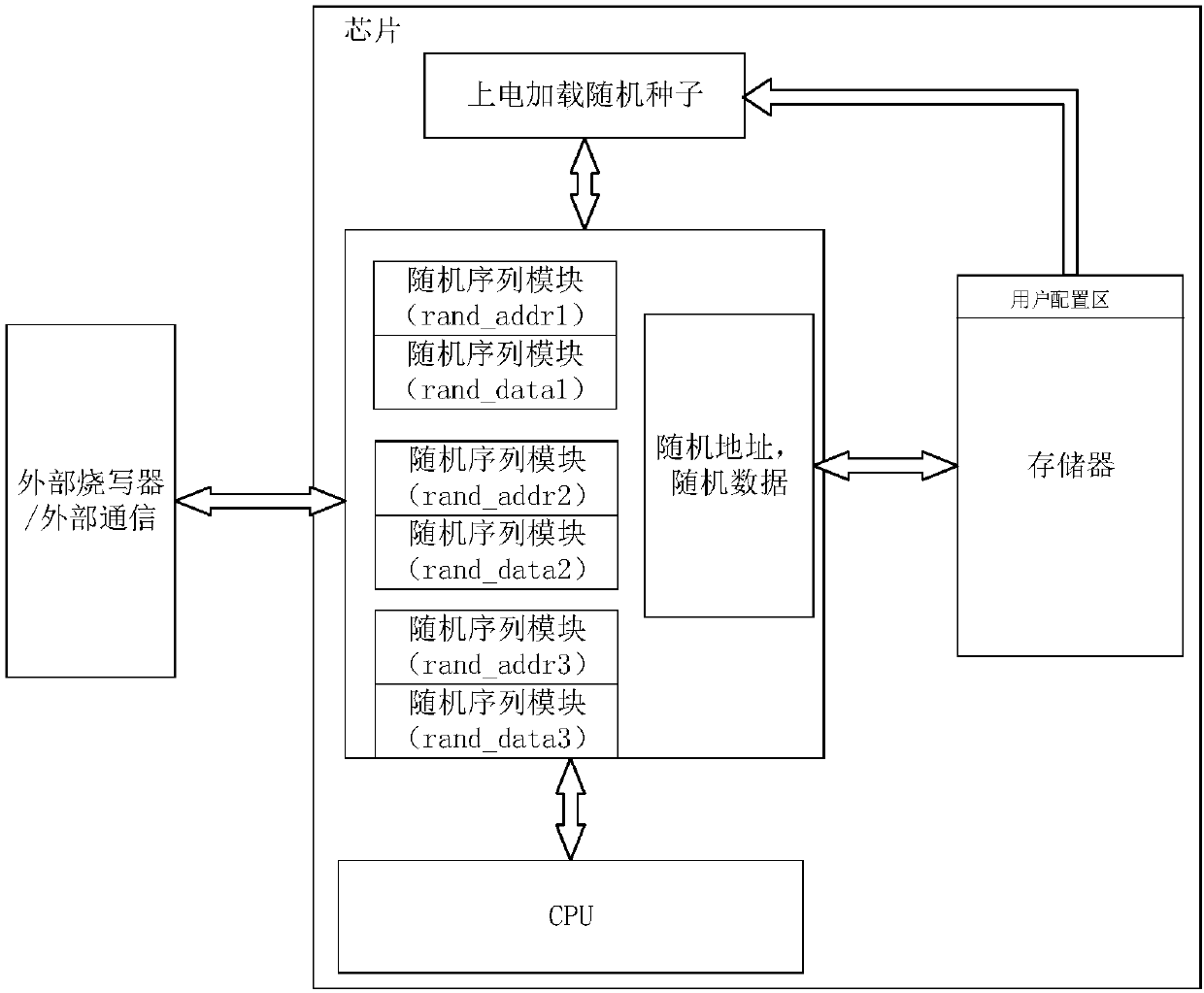
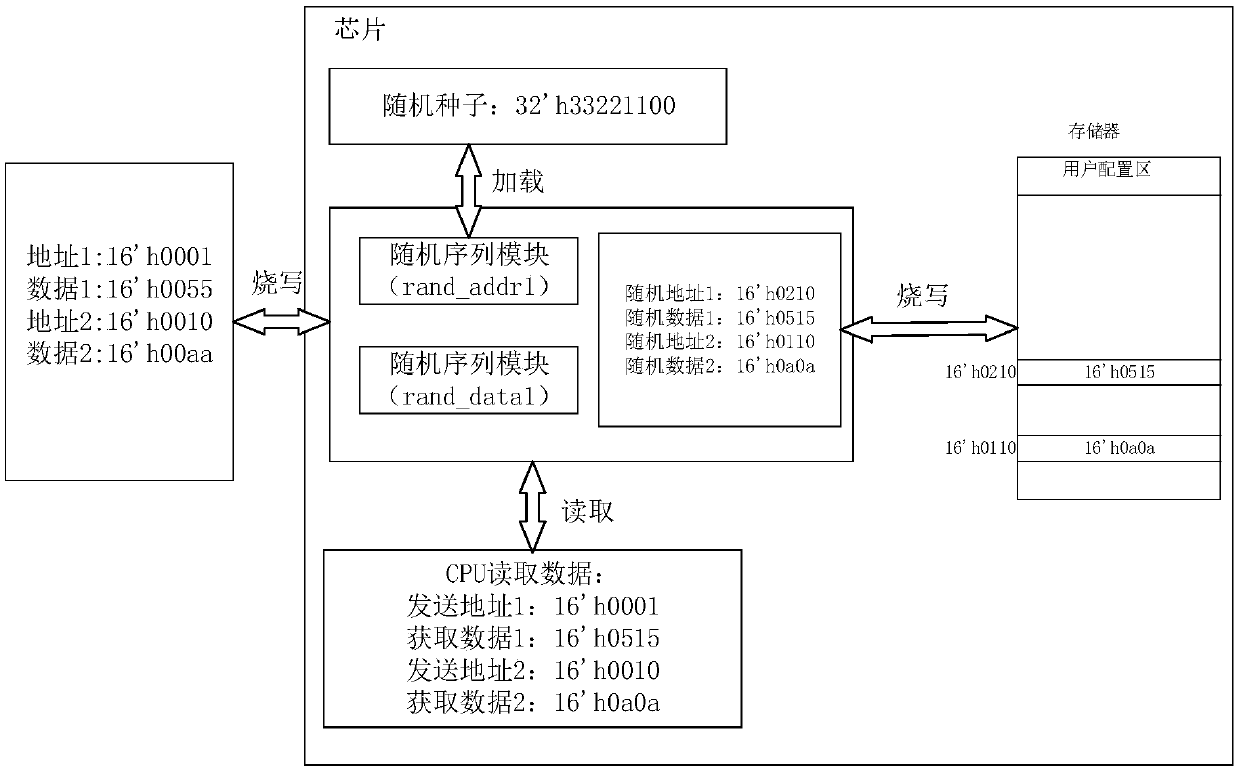
[0024] figure 1 , figure 2 Shown is the implementation method of the memory data encryption protection realized by the present invention, as shown in the figure. The memory first needs to open up a user configuration area and configure random seeds.
[0025] S101. Realize the random sequence module, using the shift register sequence (m sequence), for example, select the m sequence primitive polynomial x^24+x^7+x^2+x+1.
[0026] S102. Design a random seed for the user configuration area. Set the random seed to 32 bits, and the encryption effect is higher. At the same time, the random seed need...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More