A key security signature method based on block chain technology
A blockchain and security technology, applied in the blockchain field, can solve the problems of automatic operation and maintenance of unfavorable systems, reduce security, and low security, and achieve the effect of automatic operation and maintenance management, protection of security, and improvement of security.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0037] The specific embodiments of the present invention will be further described below in conjunction with the accompanying drawings.
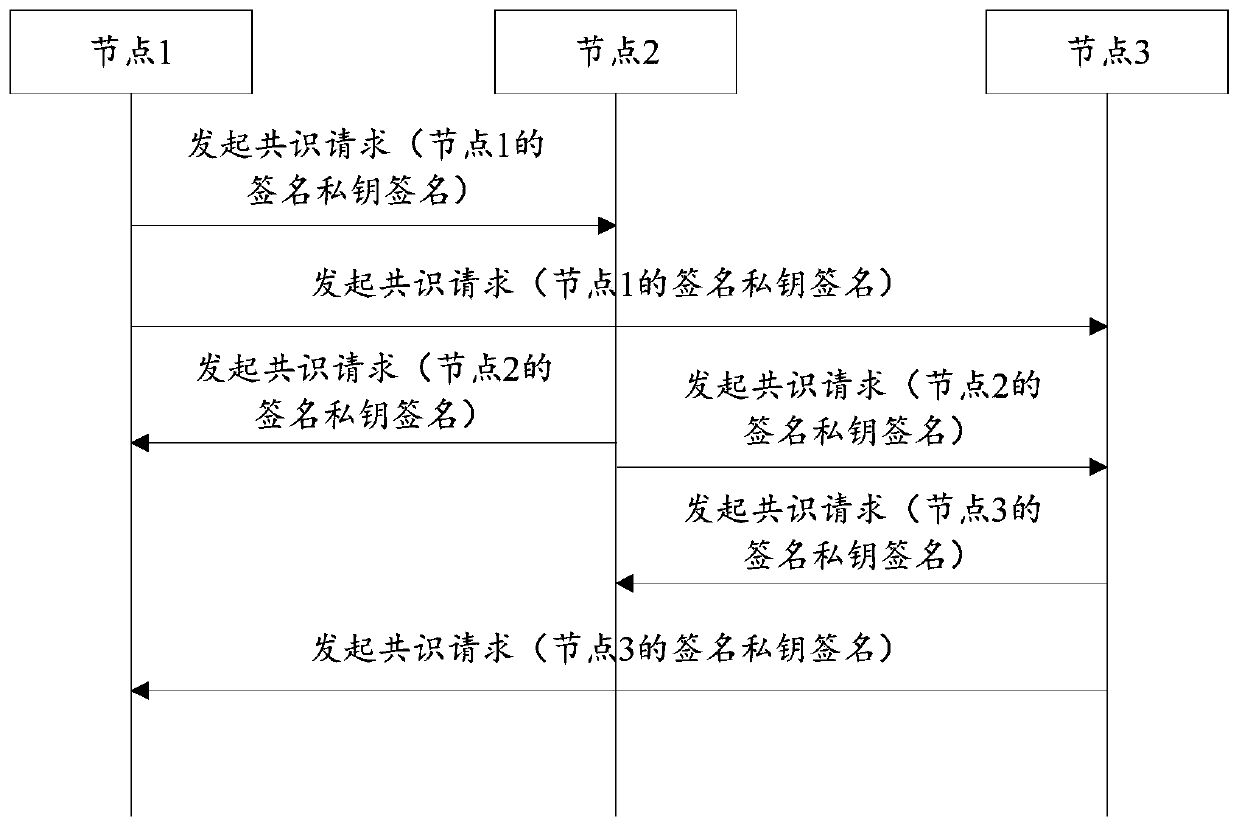
[0038] This application discloses a key security signature method based on blockchain technology. The method is used in a blockchain system. The blockchain system includes several nodes, usually at least three, and each node communicates with each other in pairs. Establish a communication connection. The nodes here can be various devices such as computers, servers, workstations, and printers. This method can be executed by any node in the blockchain system. This method mainly includes key import and key application. part.
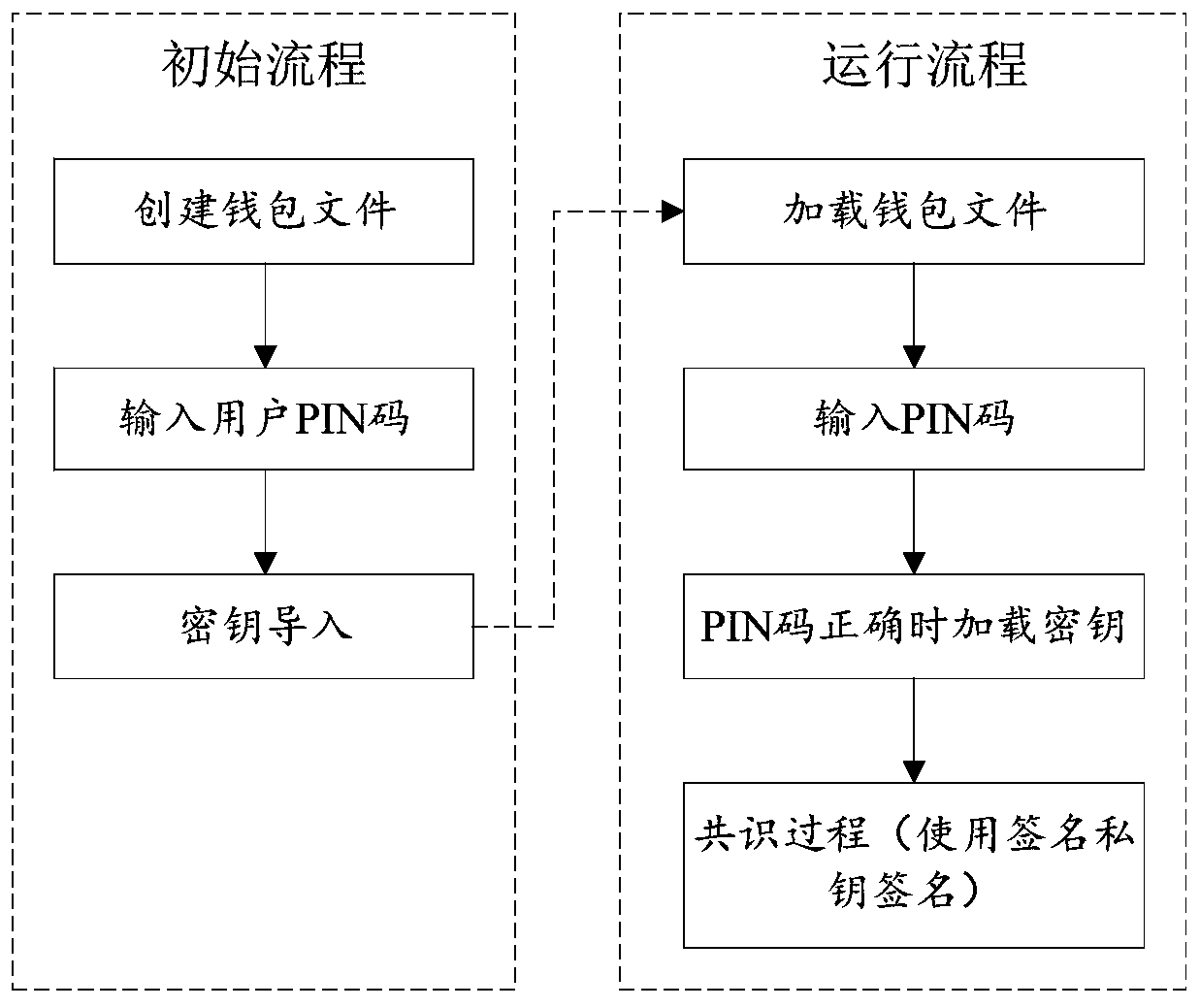
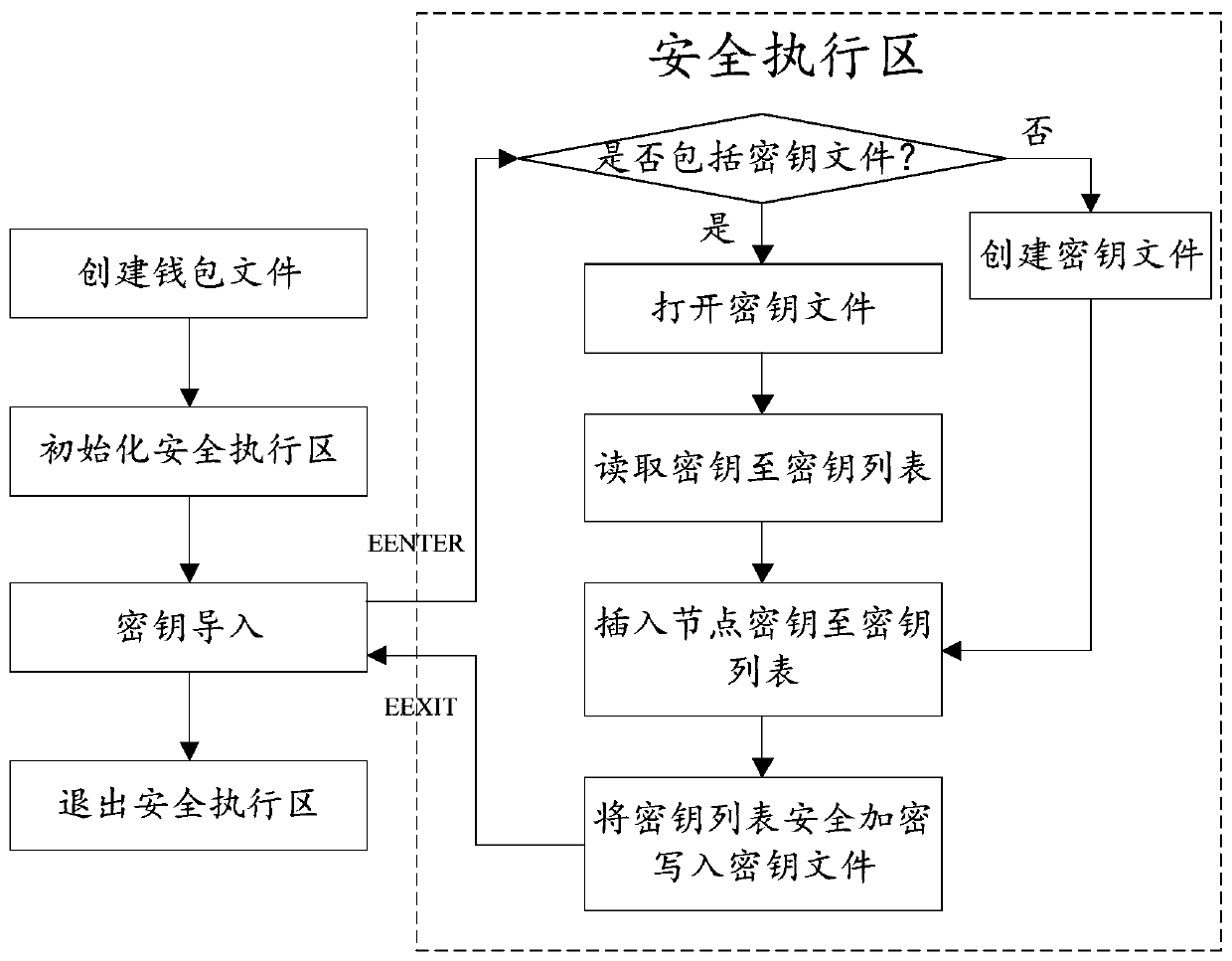
[0039] The first part is to execute the key import part when deploying the blockchain system on the node for the first time. This part includes the following steps, such as image 3 Shown:
[0040] First, create a wallet file. The wallet file includes at least the node key. The wallet file usually includes the wallet ad...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More