Authentication and cipher key negotiation method under multi-server architecture
A key agreement, multi-server technology, applied in electrical components, transmission systems, etc., can solve problems such as difficulty in server update, achieve the effect of achieving anonymity, reducing storage overhead, and protecting privacy
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0037] In order to make the technical means, creative features, goals and effects achieved by the present invention easy to understand, the present invention will be further described below in conjunction with specific illustrations.
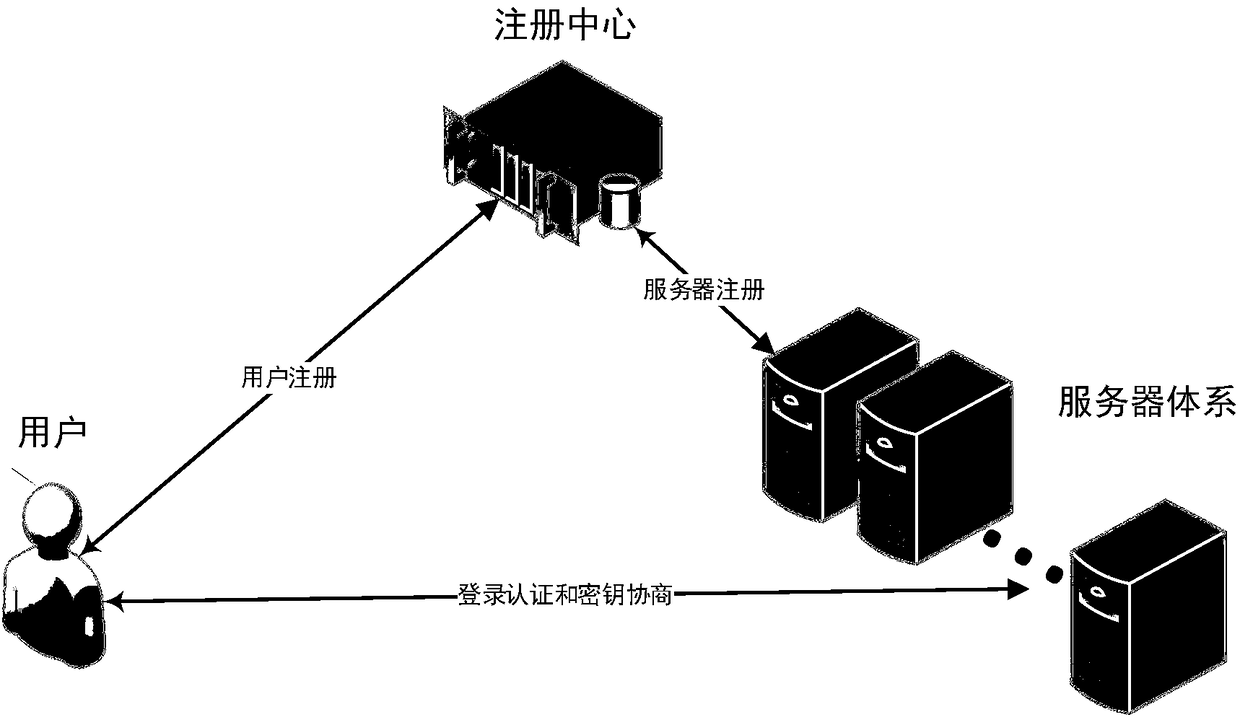
[0038] see figure 1 and figure 2 , shown in the figure is an authentication and key agreement method under a multi-server architecture of the present invention, comprising the following steps:
[0039] Step 101, system establishment
[0040] In this embodiment, the SM3 algorithm is selected as the hash function h, and the key derivation function KDF is constructed using the SM3 algorithm, and the selected function is made public.
[0041] Step 102, user registration
[0042] User U selects ID, password PW, extracts biometric value BIO, and calculates P=h(PW||BIO), and then submits ID and P to registration center RC through a secure channel.
[0043] After the registration center RC receives the ID and P, it calculates A=h(ID||x), C=h(ID||h(...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More