Business processing security verification method and device
A business processing and security verification technology, which is applied in the field of business processing security verification methods and devices, can solve problems such as abnormal result display and transaction failure, and achieve the effect of increasing cracking costs and improving security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0023] In order to make the purpose, technical solutions and advantages of the embodiments of the present invention more clear, the embodiments of the present invention will be further described in detail below in conjunction with the accompanying drawings. Here, the exemplary embodiments and descriptions of the present invention are used to explain the present invention, but not to limit the present invention.
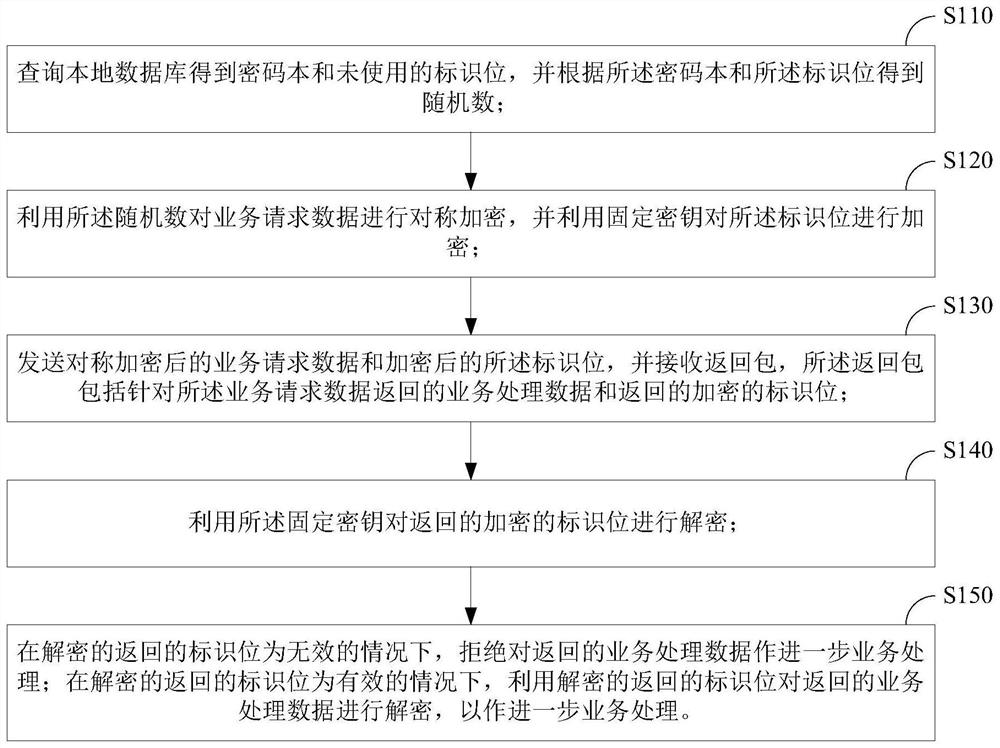
[0024] figure 1 It is a schematic flowchart of a business processing security verification method according to an embodiment of the present invention. Such as figure 1 As shown, the business processing security verification method of this embodiment may include:
[0025] Step S110: Query the local database to obtain the codebook and unused identification bits, and obtain random numbers according to the codebook and the identification bits;
[0026] Step S120: use the random number to symmetrically encrypt the service request data, and use a fixed key to encrypt the...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More