Database audition method
A database and data packet technology, applied in the field of network security, can solve problems such as low audit efficiency, and achieve the effects of improving audit efficiency, reducing processing capacity, and eliminating load
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0014] The following will clearly and completely describe the technical solutions in the embodiments of the present invention with reference to the drawings in the embodiments of the present invention.
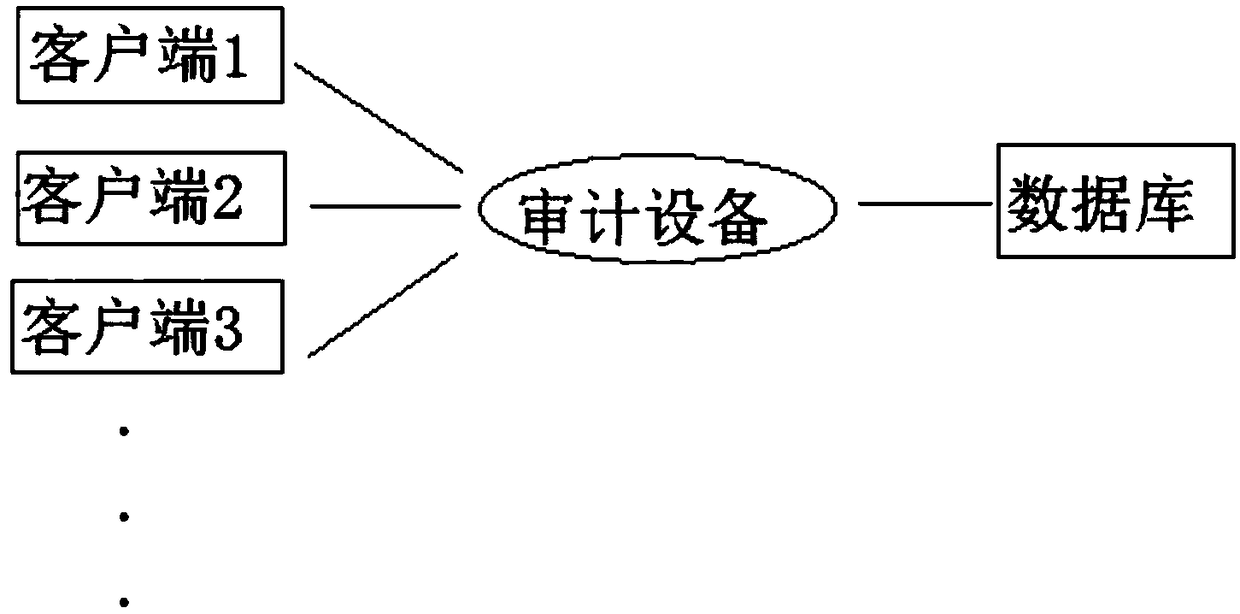
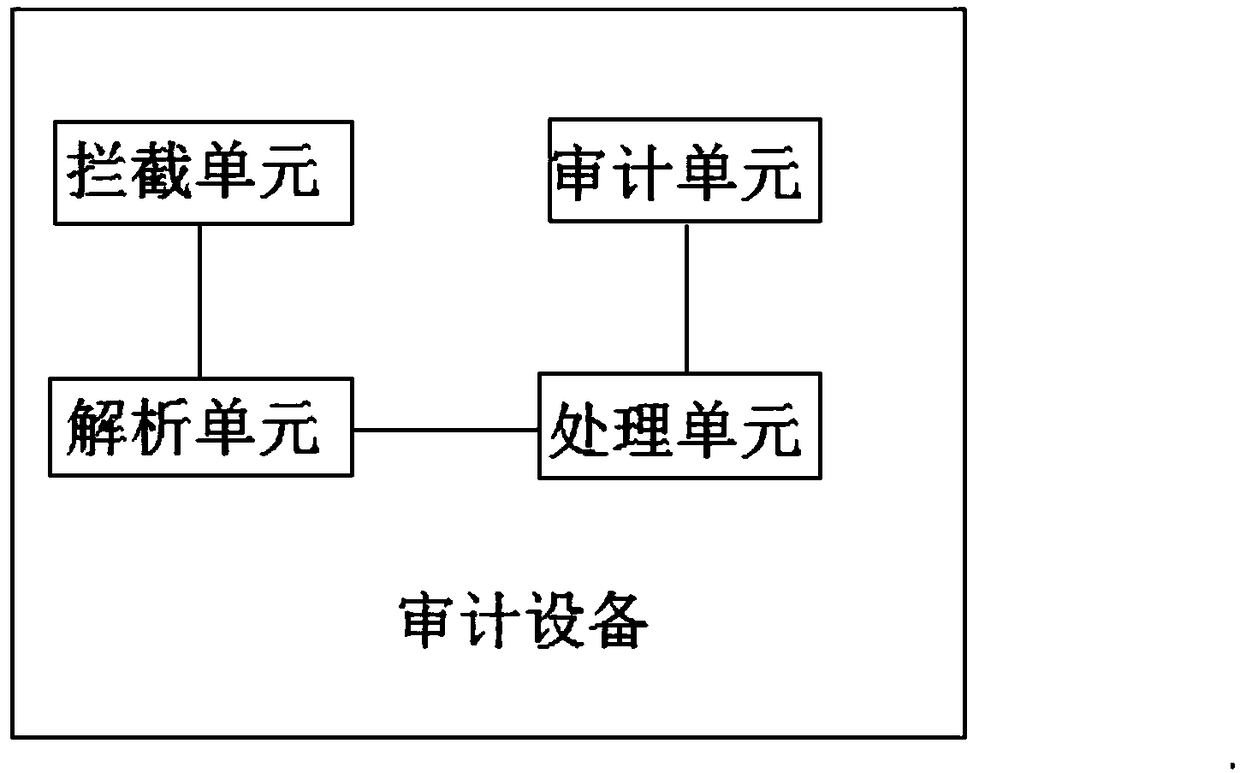
[0015] The embodiment of database auditing method of the present invention: as Figure 1-Figure 2 As shown, the database auditing method comprises the following steps, 1) the auditing device intercepts the interactive data packet between the database client and the database server, and resolves the interactive content between the data client and the database server from the interactive data packet; 2 ) The audit device generates a session log containing the processing result of the interactive data packet, and adds a session ID corresponding to the database access session in the session log; 3) Grouping the session log according to the session ID for the preset audit user to perform database auditing.
[0016] The auditing device intercepts the interactive data packets between...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More