Authentication method and system
An identity verification method and identity verification technology, applied in the direction of digital data authentication, etc., can solve the problems of complex use of verification technology, easy to be simulated by programs, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
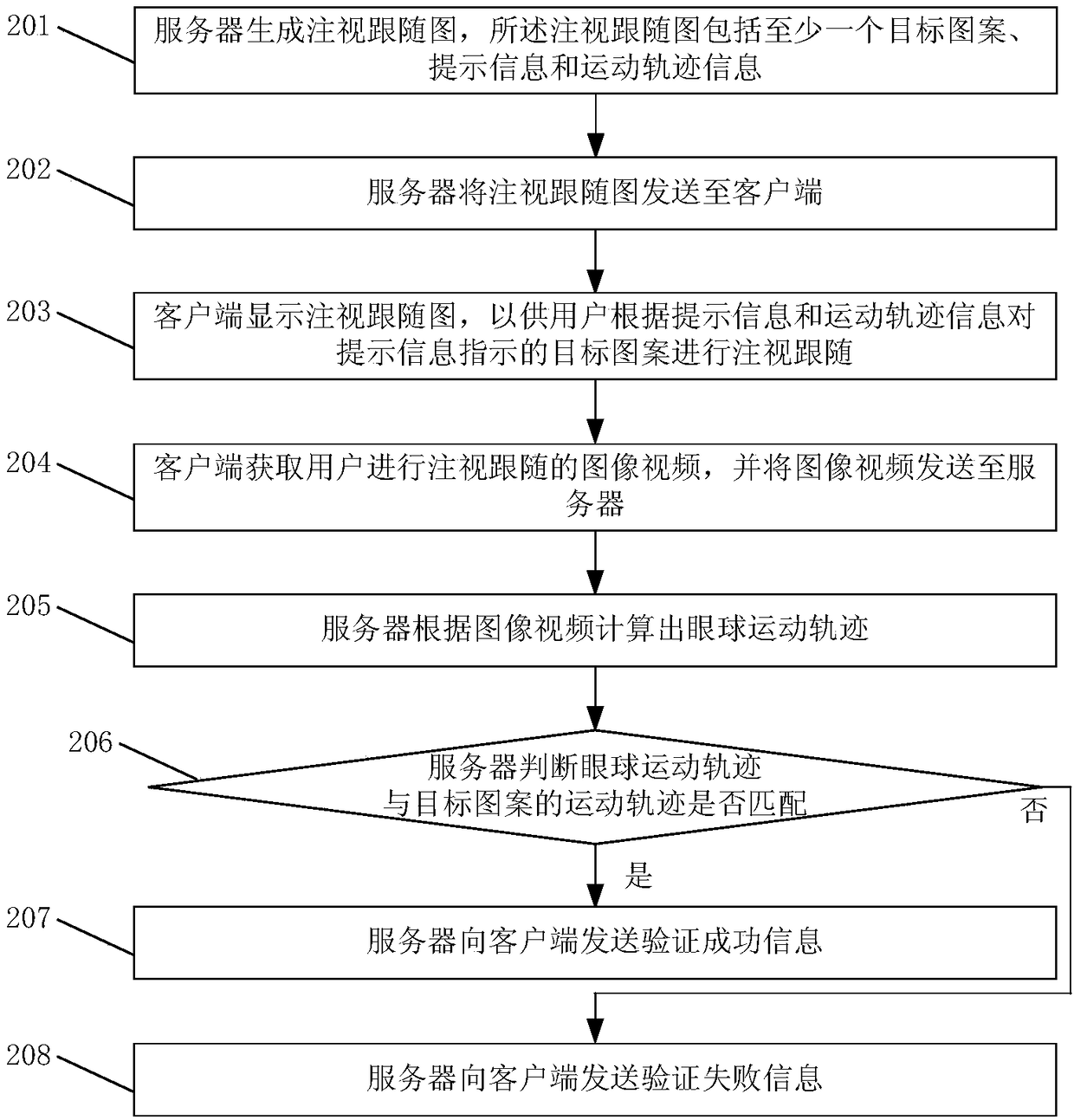
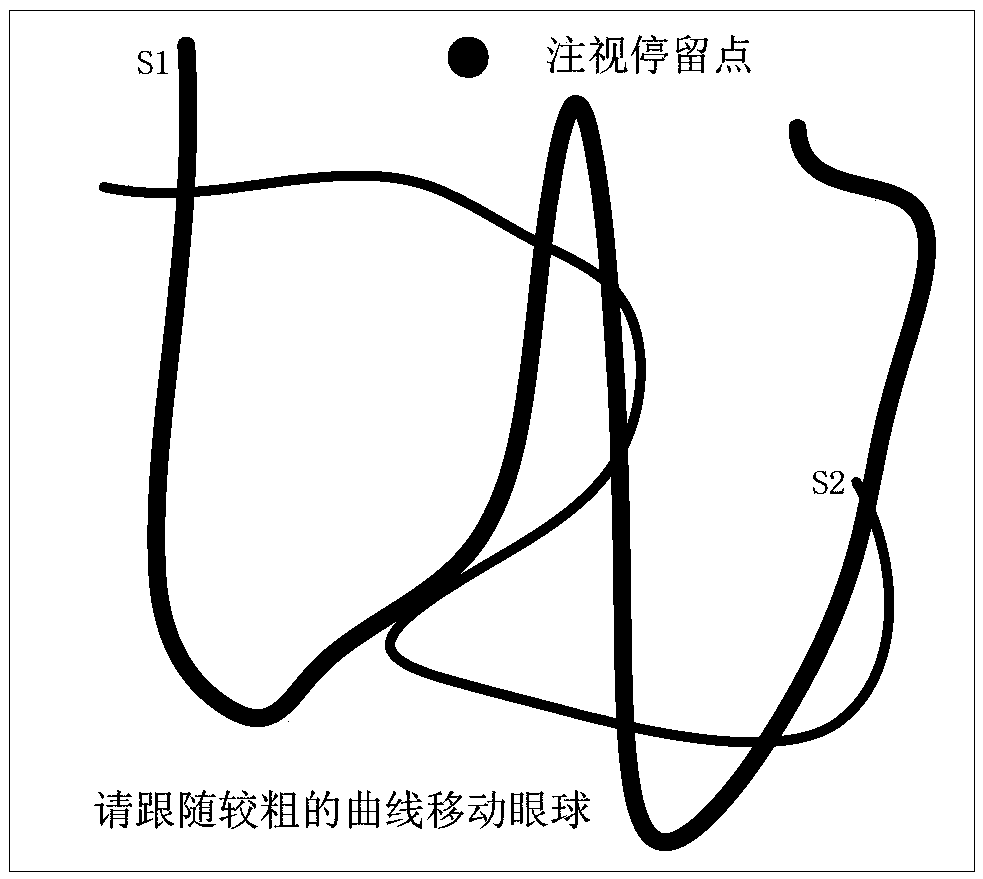
[0034] In order to enable those skilled in the art to better understand the technical solution of the present invention, the identity verification method and system provided by the present invention will be described in detail below in conjunction with the accompanying drawings.
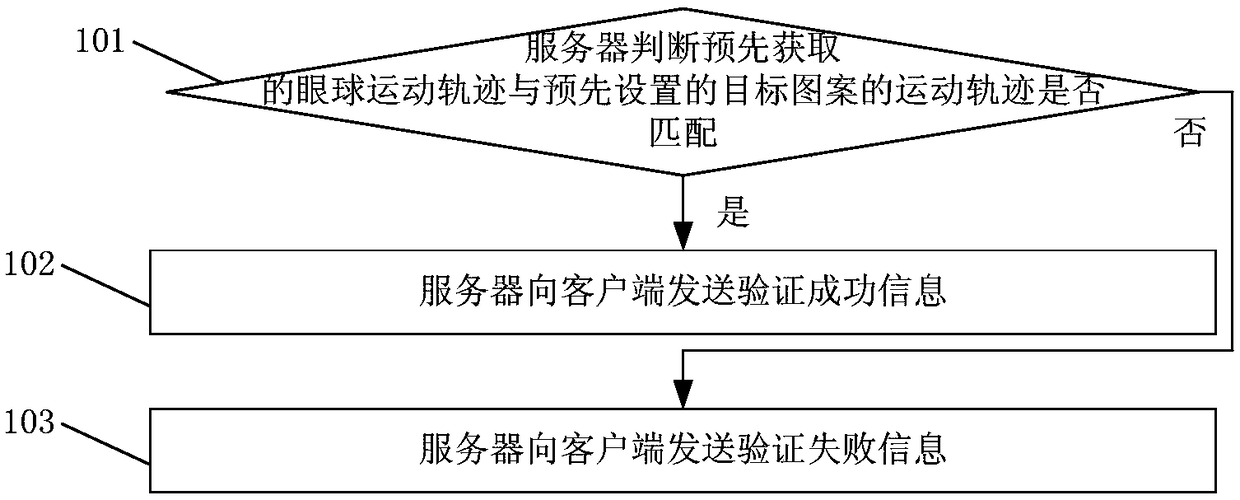
[0035] figure 1 A flow chart of an identity verification method provided by Embodiment 1 of the present invention, such as figure 1 As shown, the method includes:
[0036] Step 101, the server judges whether the pre-acquired eyeball movement trajectory matches the preset target pattern movement trajectory, if yes, execute step 102; if not, execute step 103.
[0037] Step 102, the server sends verification success information to the client, and the process ends.
[0038] Step 103, the server sends verification failure information to the client, and the process ends.
[0039] In the technical solution of the identity verification method provided in this embodiment, if the server judges that the pre-...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More