AES (Advanced Encryption Standard) key extension method
A key expansion and key technology, applied in the field of information security, can solve problems such as the inability to guarantee the security of key expansion, increasing system hardware requirements, and system security risks.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0065] The specific embodiment of the present invention will be further described below in conjunction with accompanying drawing:
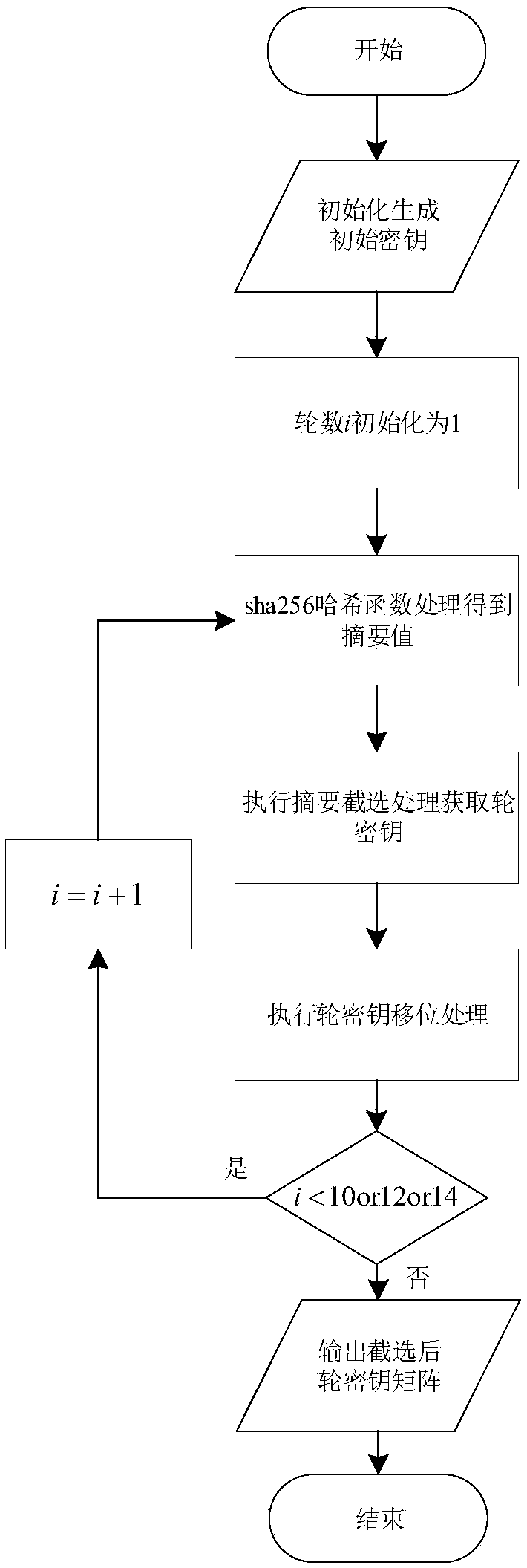
[0066] The specific flow of the round key extension of the present invention is as attached figure 1 As shown, its specific steps have the following 6 steps.
[0067] 1. According to the key length of the selected AES algorithm, use a pseudo-random number generator to generate a random number with the required number of bits, and then obtain an initial key, and store it as a key for encryption and decryption.
[0068] 2. Since the key length of AES is different, the number of rounds required for key expansion is different. Therefore, after obtaining the initial key, the number of key rounds i needs to be initialized to 1. For a key with a length of 128 bits and a length of 192 bits key and 256-bit key, the number of key expansion rounds are 10, 12 and 14 rounds respectively.
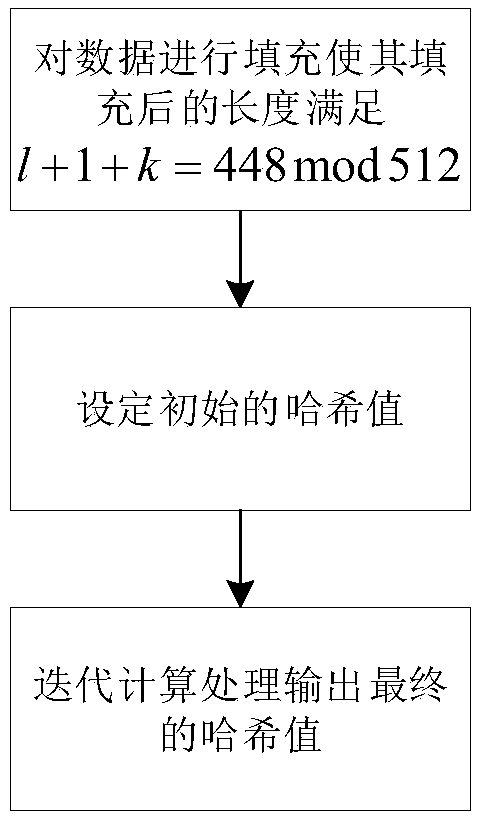
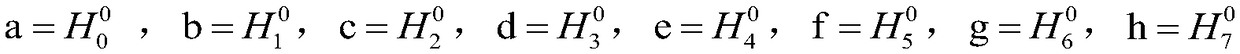
[0069] 3. After obtaining the initial key, you can use the sha256 has...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More