Prompt information push method and device, service platform and storage medium
A technology for prompting information and geographical location, applied in the field of information security, can solve the problems of information harassment, limited efficiency of security awareness, lack of pertinence, etc., and achieve the effect of small information interference and good security warning effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
example 1
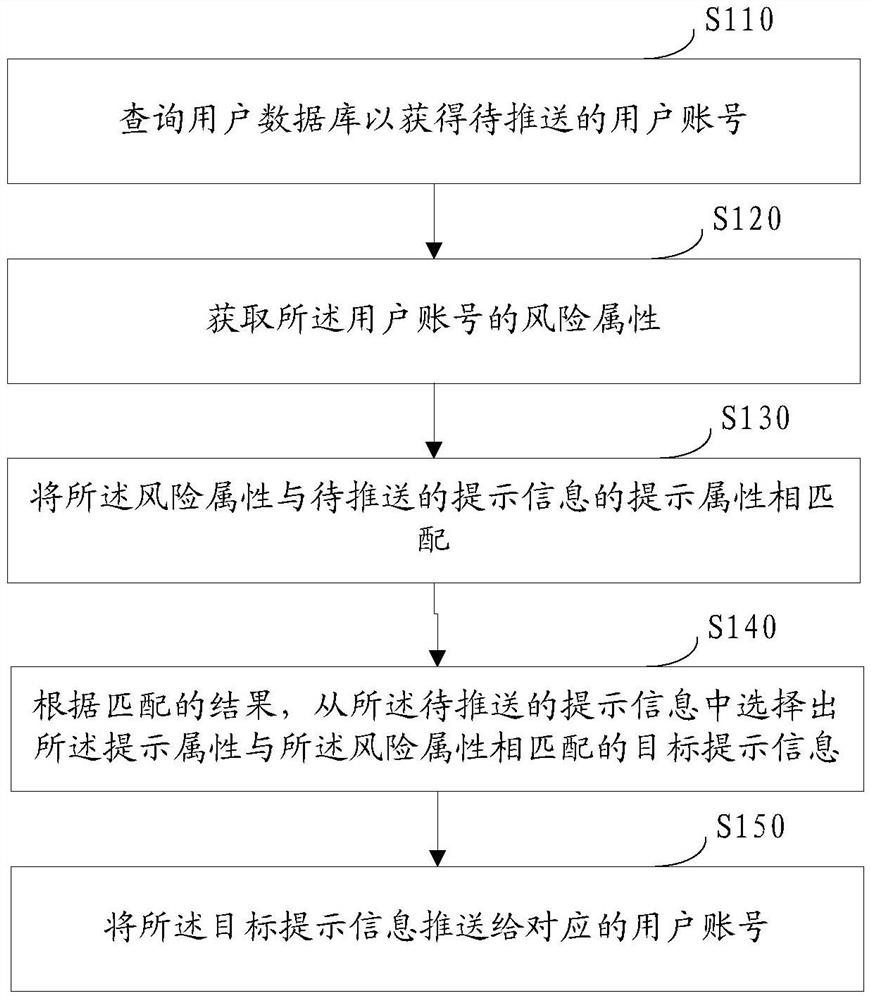
[0168] Such as Figure 7 As shown in the example, the prompt information push method implemented in this example includes:
[0169] Step S1: Report the detailed historical risk data (that is, the aforementioned predetermined type of data) through the risk monitoring platform and the mobile phone manager, which may specifically include: reporting the user's historical risk detailed data through the terminal of the risk monitoring platform and the mobile phone manager. The reported risk details data may include: attachments with records of fake base stations, receiving fraudulent calls, receiving fraudulent text messages, accessing malicious uniform resource addresses (URLs), and attachments with records of risky WiFi and mobile phone poisoning, etc. The risk detailed data here is one of the aforementioned predetermined types of data.
[0170] S2: Calculate the user's risk attributes through the susceptible population model, and dynamically update it, and maintain a user's risk...
example 2
[0178] Such as Figure 8 As shown, based on Example 1, this example provides a method for establishing a susceptible population model and generating a user risk attribute table, including:
[0179] S11: Risk monitoring platform detection, including: monitoring proprietary reporting channels, existing risk information databases and data exchange with partners;
[0180] S12: The mobile phone manager collects user operations.
[0181] S13: Report risk details data; susceptible population model;
[0182] S14: Establish a susceptible population model based on the reported risk details data, and obtain a user risk attribute table.
[0183] The establishment of the susceptible population model (equivalent to the aforementioned analysis model) is based on the details of the risk data of the user account. Only with sufficient data as the training set can the model be established more accurately. Data collection is divided into two parts. The first is the risk monitoring platform, wh...
example 3
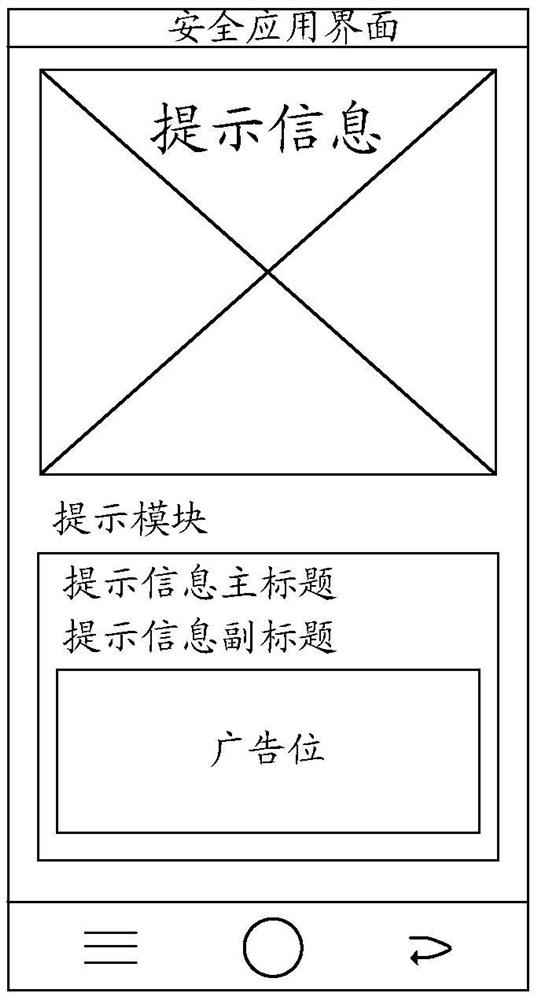
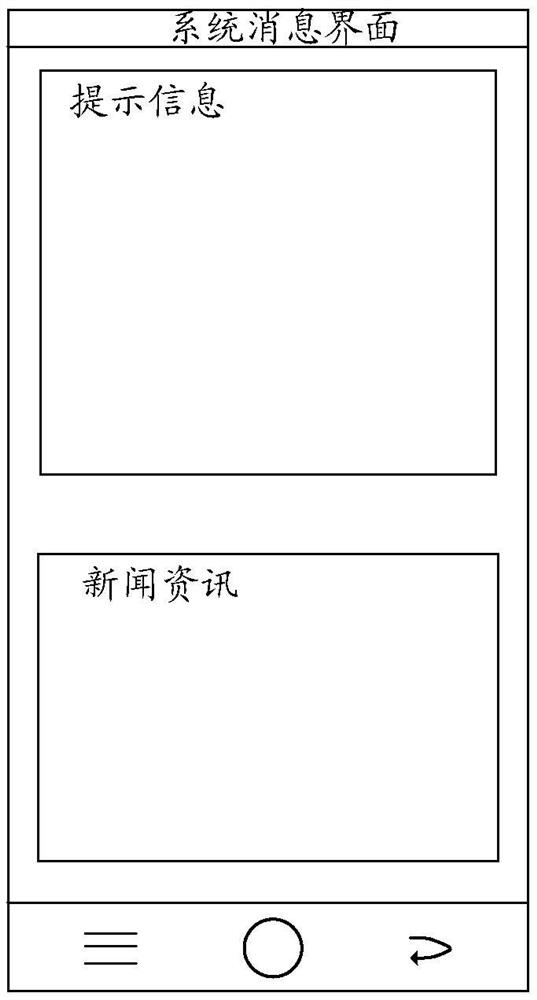
[0185] Such as Figure 9 As shown, based on Example 1, this example provides a method for managing security information of a security resource pool, including:
[0186] First of all, the security information content resource pool needs to collect security information. Information sources may include: original manuscripts, manuscript collection, and information provided by media cooperation. The security advisory here is one of the aforementioned prompt messages.
[0187] Secondly, the security information content resource pool needs to classify resources to form security information in various aspects such as security reports, fake base stations, risky WiFi, social worker fraud, fraudulent text messages, fraudulent calls, viruses, and phishing websites.
[0188] In short, the security information content resource pool covers all security-related information content such as security reports, fake base stations, risky WiFi, social worker fraud, etc. It can enrich the content of t...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More