Internet of Vehicles security data sharing method based on edge computing
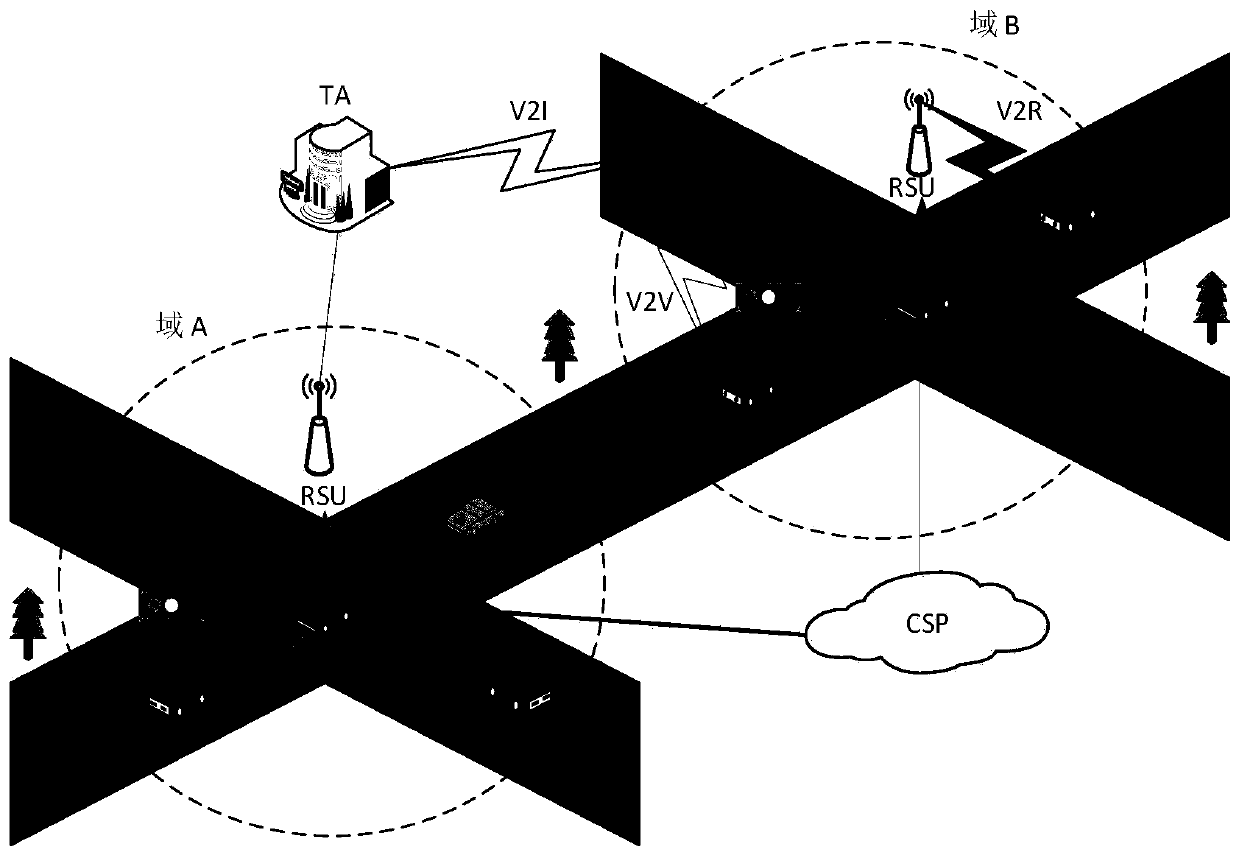
A technology for edge computing and secure data, applied in the field of vehicle network communication security, which can solve problems such as RSU delay and heavy load
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
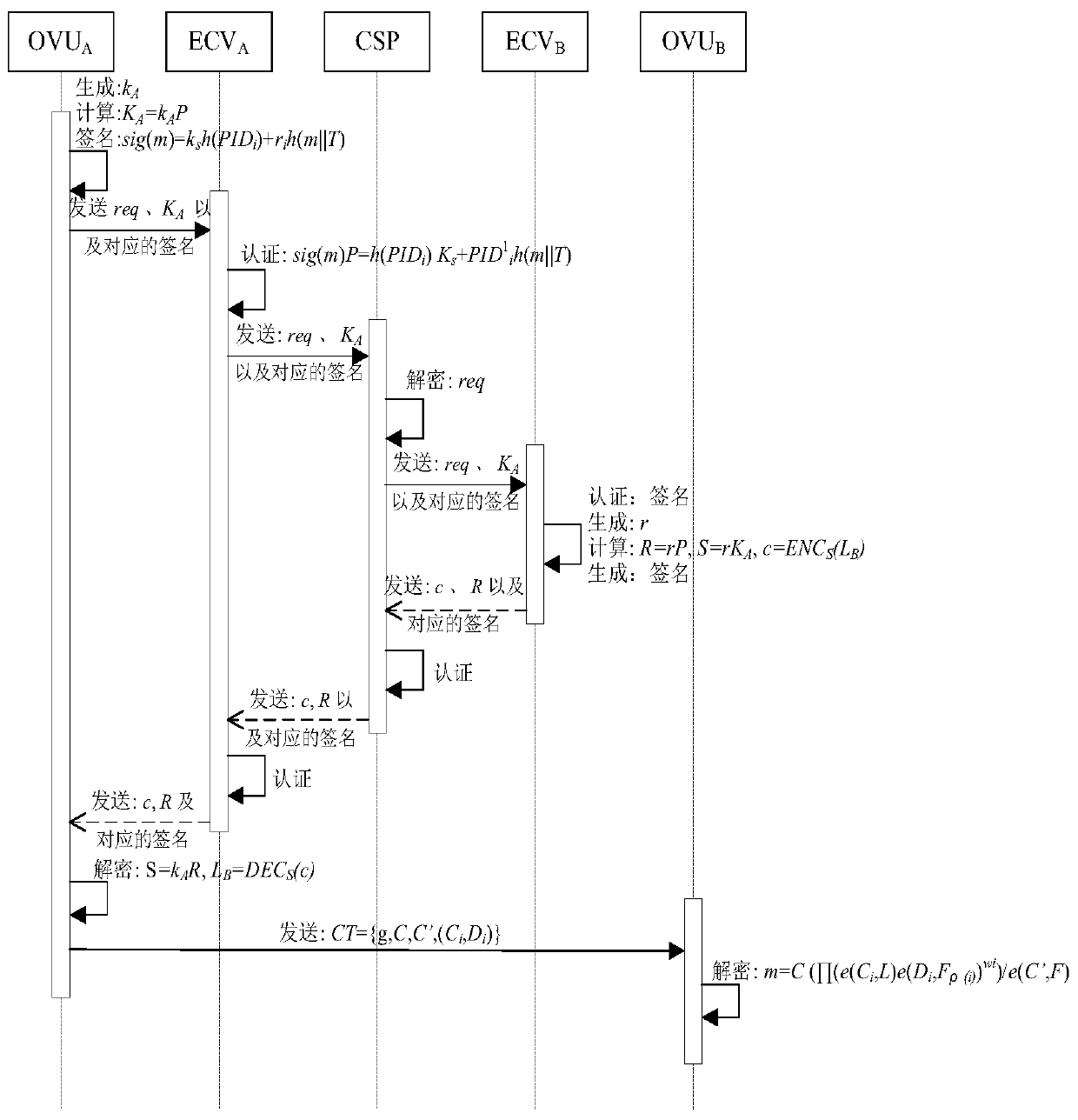
[0044] According to the edge computing-based security data sharing method for Internet of Vehicles in this embodiment, the interaction diagram is as follows figure 2 As shown, it mainly includes the following steps:
[0045] (1) Initialization of all entities in the Internet of Vehicles: TA generates system parameters, and TA issues necessary parameter information for each vehicle;
[0046] (2) Safe data sharing between vehicles: vehicle release request information, edge computing vehicle processing and forwarding request information, data release vehicle encrypted data, and data request vehicle decryption data.
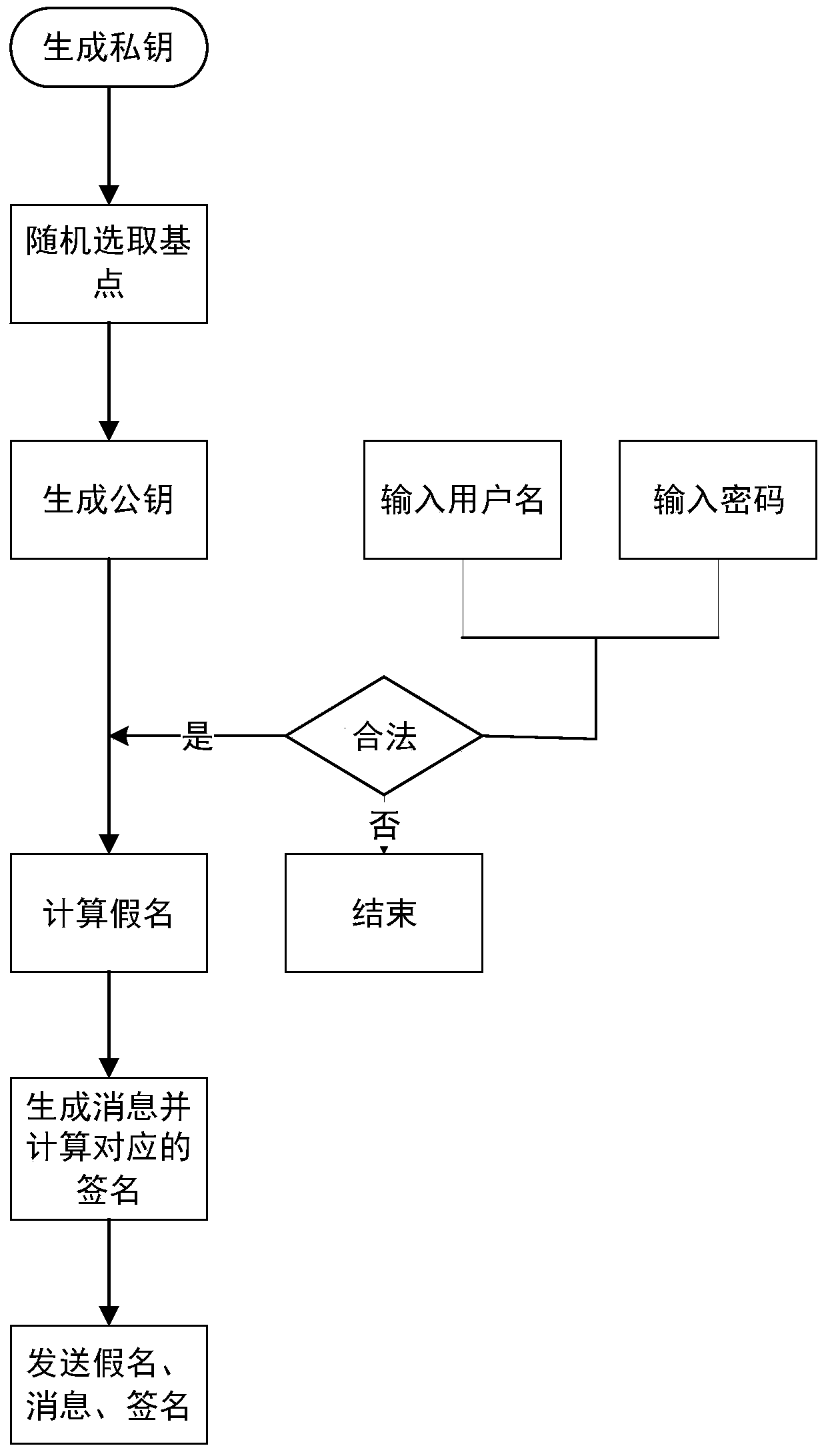
[0047] Step (1) TA generates system parameters, TA generates necessary system parameters, including elliptic curve parameters, system public key, master private key, etc. The specific steps are as follows:
[0048] 1) TA randomly selects q, and based on the finite field F q Select two random numbers a and b, generate one defined as y 2 =x 3 The non-singular elli...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More