Speech retrieval method and system
A retrieval system and voice technology, applied in audio data retrieval, speech analysis, transmission system, etc., can solve the problem of low security of hash summary, improve retrieval efficiency and retrieval accuracy, good robustness and differentiation , the effect of improving safety
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
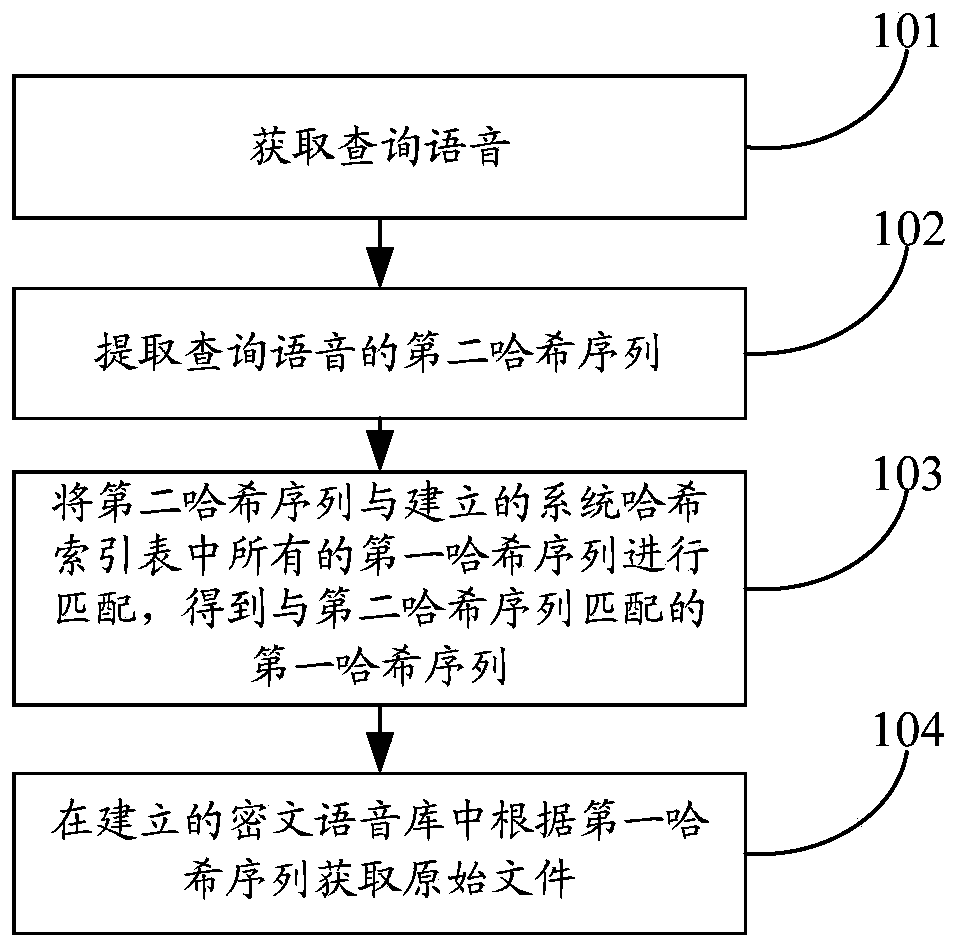
[0072] This embodiment provides a voice retrieval method. Before performing voice retrieval, a ciphertext voice database and system hash index table need to be established in the cloud.
[0073] The establishment of ciphertext speech database includes:
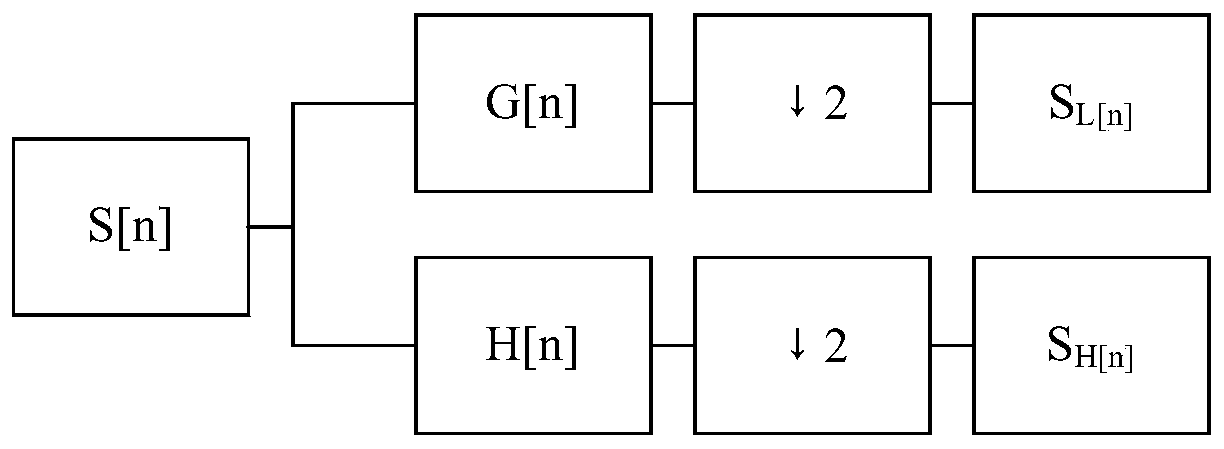
[0074] 1. Obtain the original file. The original file includes the speech signal s(t).
[0075] 2. Encrypt the original file to obtain the encrypted file and upload the encrypted file to the voice library in the cloud to obtain the ciphertext voice library. Specifically, it includes: encrypting the original file with a two-dimensional chaotic map encryption algorithm, obtaining the encrypted file and uploading the encrypted file to the voice database in the cloud, to obtain the ciphertext voice database.
[0076] Encrypting the original file using the two-dimensional chaotic map encryption algorithm specifically includes:
[0077] Set two initial values: when k = 1, x k-1 =1.0, x k = 1.2. Difference equation through two-dimensional ...
Embodiment 2
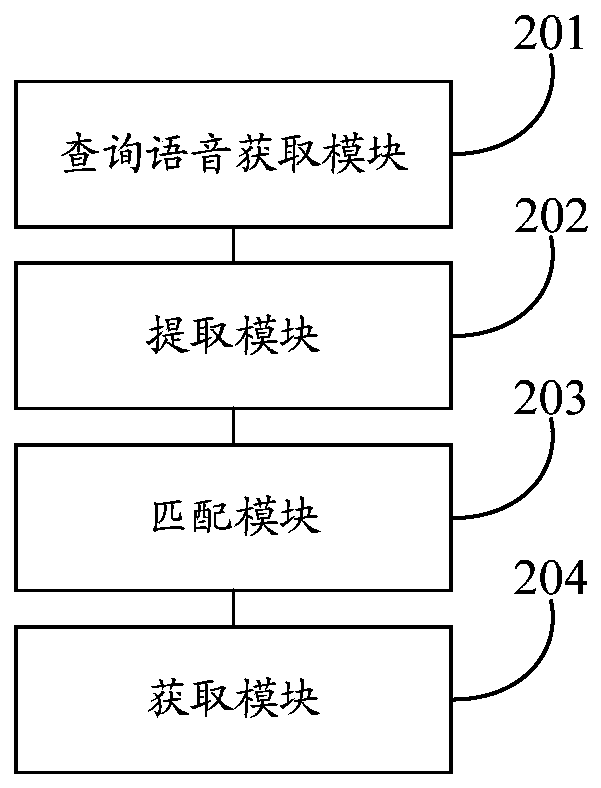
[0146] This embodiment provides a voice retrieval system. Before performing voice retrieval, it is necessary to establish a ciphertext speech database and a system hash index table, so first execute the ciphertext speech database establishment module and the system hash index table establishment module.
[0147] The ciphertext speech database establishment module is used to establish the ciphertext speech database.
[0148] The ciphertext speech library establishment module includes:
[0149] The original file obtaining unit is used to obtain the original file. The original file includes the speech signal s(t).
[0150] The encryption unit is used to encrypt the original file to obtain the encrypted file and upload the encrypted file to the voice library in the cloud to obtain the ciphertext voice library.
[0151] Encryption unit, including:
[0152] The encryption subunit is used to encrypt the original file using a two-dimensional chaotic map encryption algorithm to obtain the encry...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More