A database access control method and system supporting business security marks
A security marking and access control technology, applied in relational databases, database models, digital data protection, etc., can solve problems such as narrow scope of application, no support for database objects, and increased system complexity, achieving wide applicability, reducing dependencies, The effect of reducing complexity
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
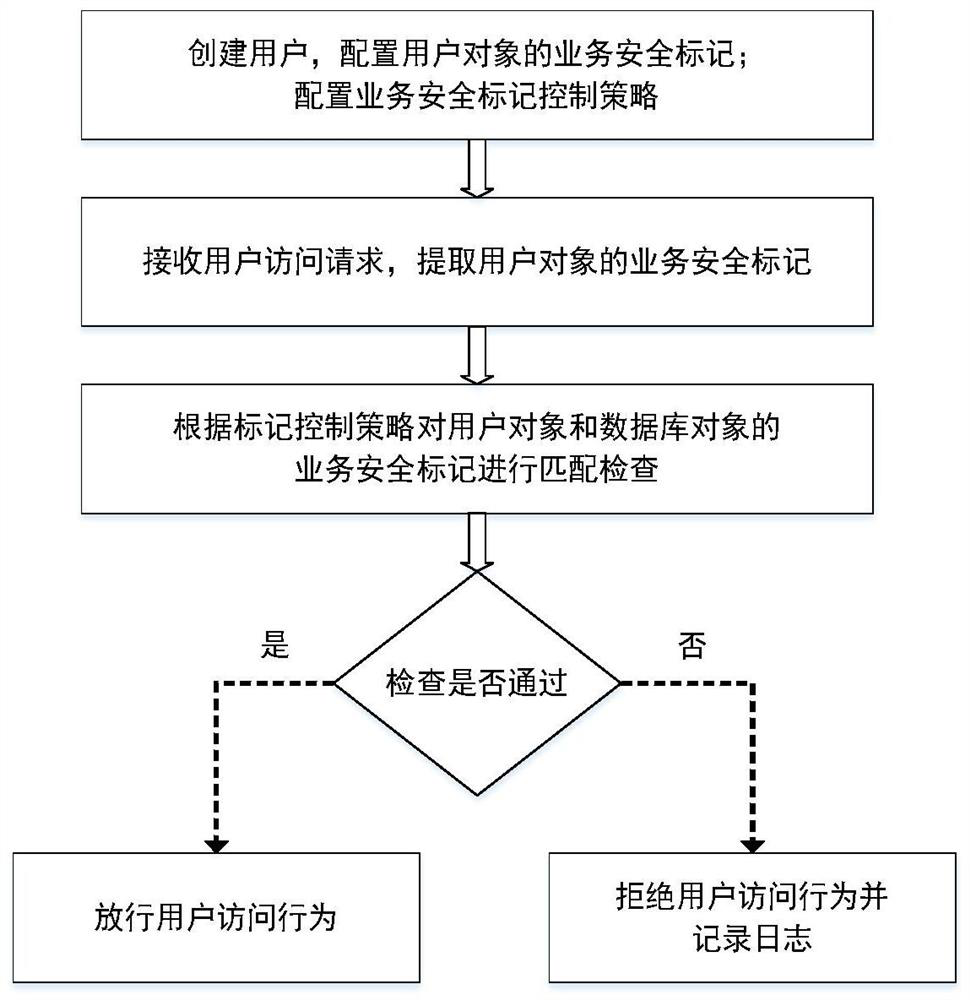
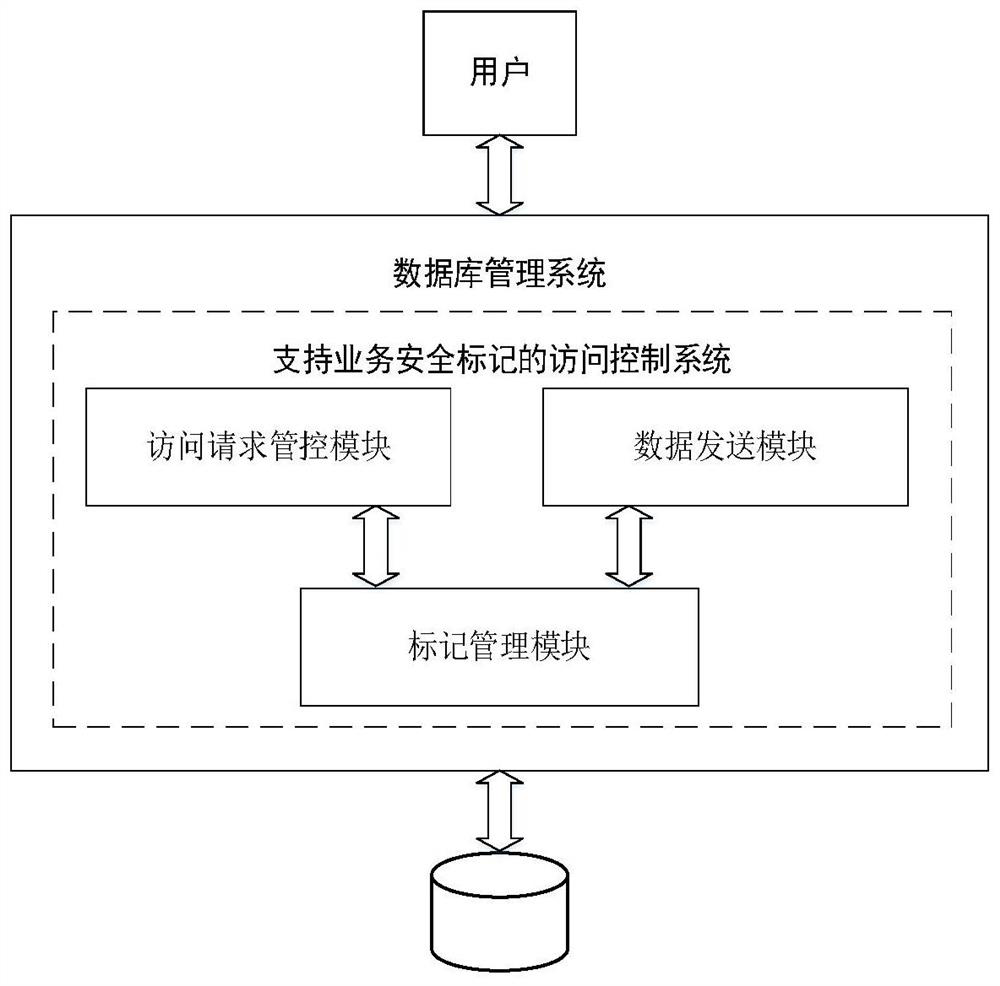
Method used
Image
Examples
Embodiment Construction
[0025] In order to make the objects and advantages of the invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings and embodiments. It should be understood that the embodiments described here are only used to illustrate and explain the present invention, not to limit the present invention.
[0026] 1. Business security flag configuration
[0027] The service security mark M is a tuple group including various service security attributes, M=. Where C is the security level; G is multiple business security attributes G i set of , G={g 1 , g 2 ,...g n}, g i It can be business security attributes such as business categories, work groups, roles, and environmental requirements; F is the operation control attribute f j set of , F={f 1 ,f 2 ,... f m}, f j It can be operational attributes such as read-write control, print control, burn control, and copy control.
[0028] The business security mark of the d...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More