Verifiable outsourcing computing method for realizing safety and high efficiency of large-scale matrix multiplication, client and cloud computing system
A technology of matrix multiplication, calculation method, applied in the field of cloud computing
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
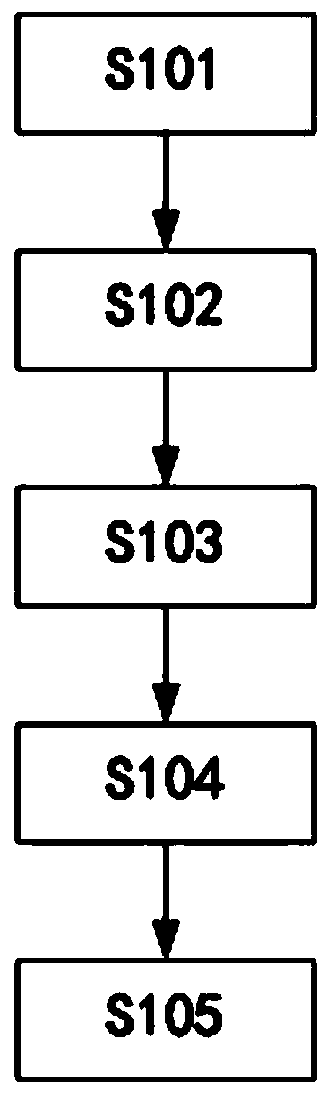
[0083] Such as figure 1 As shown, the safe and efficient verifiable outsourced computing method for realizing large-scale matrix multiplication provided in this embodiment may, but is not limited to, include the following steps S101-S105.
[0084] S101. Using a one-way trapdoor function to generate a public-private key pair where A represents the public key matrix and is the private key matrix and q represents a prime number greater than 2, express yes Each element in finds the remainder about q, Z q ∈{0,1,2,...,q-1}, m is a positive integer not less than 1000, n is a positive integer and n<
[0085] In the step S101, the one-way trapdoor function is a kind of special one-way function with a trapdoor, which includes two obvious features: one is one-way, and the other is that there is a trapdoor; the so-called one-way , also known as irreversibility, that is, for a function y=f(x), it is easy to calculate y if x is known, but it is easy to calculat...
Embodiment 2
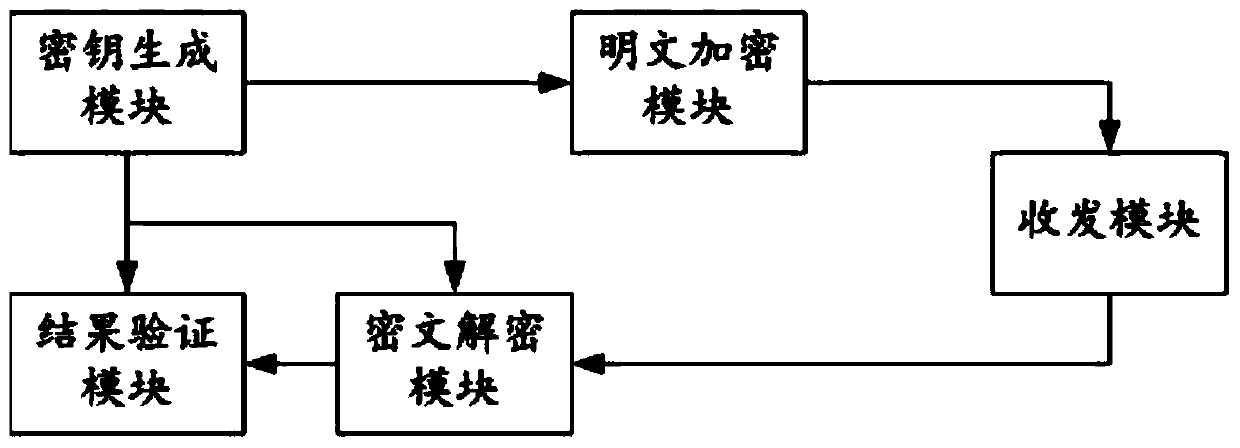
[0159] Such as figure 2 As shown, this embodiment provides a client that implements the first embodiment above, and is used to implement a safe and efficient verifiable outsourcing calculation method for large-scale matrix multiplication as described in the first embodiment, and includes a key generation module, Plaintext encryption module, transceiver module, ciphertext decryption module and result verification module;
[0160] The key generation module is used to generate a public-private key pair using a one-way trapdoor function where A represents the public key matrix and is the private key matrix and q represents a prime number greater than 2, express yes Each element in finds the remainder about q, Z q ∈{0,1,2,…,q-1}, m is a positive integer not less than 1000, n is a positive integer and n<<m;
[0161] The plaintext encryption module is connected to the key generation module in communication, and is used for importing the first plaintext mat...
Embodiment 3
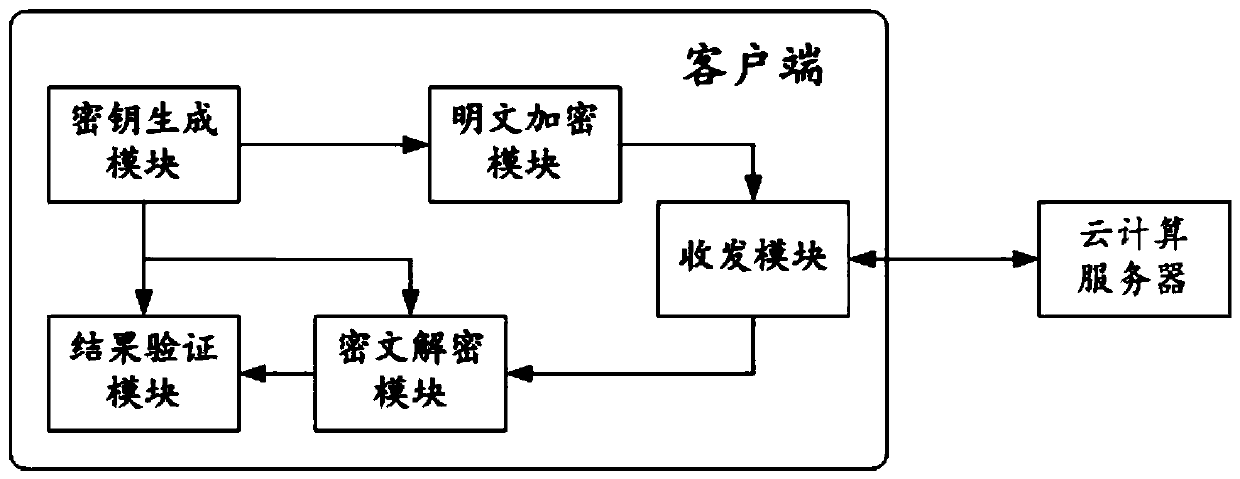
[0173] Such as image 3 As shown, this embodiment provides a cloud computing system including the foregoing embodiment two, including a cloud computing server and a client as described in embodiment two; the cloud computing server communicates with the transceiver module of the client, and uses After receiving the first ciphertext matrix set and the second set of ciphertext matrices Finally, through outsourcing computing, the cloud computing obtains the corresponding feedback matrix Φ, and feeds back the cloud computing result to the transceiver module. The working process and technical effects of this embodiment can also be deduced undoubtedly with reference to Embodiment 1, and will not be repeated here.
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More