A secure hss/udm design method and system for realizing privacy protection function
A privacy protection and functional technology, applied in digital data protection, computer security devices, computing, etc., can solve problems such as hidden dangers, small number of users, and difficulty in network access testing and maintenance for operators
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0054] In order to have a clearer understanding of the technical features, objects and effects of the present invention, the specific embodiments of the present invention will now be described. It should be understood that the specific embodiments described herein are only used to explain the present invention, but not to limit the present invention, that is, the described embodiments are only a part of the embodiments of the present invention, rather than all the embodiments. Based on the embodiments of the present invention, all other embodiments obtained by those skilled in the art without creative work fall within the protection scope of the present invention.
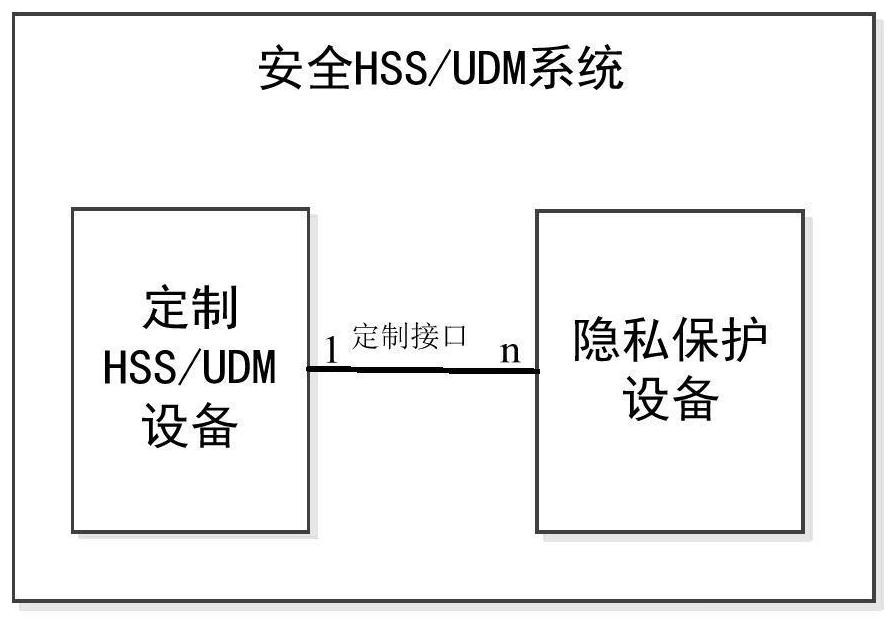
[0055] This embodiment provides a secure HSS / UDM design method and system for implementing a privacy protection function. The secure HSS / UDM system implants the protected IMSI / SUPI and the protected IMSI / SUPI in the generated authentication vector according to the customized IMSI / SUPI protection algorithm. Control ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More