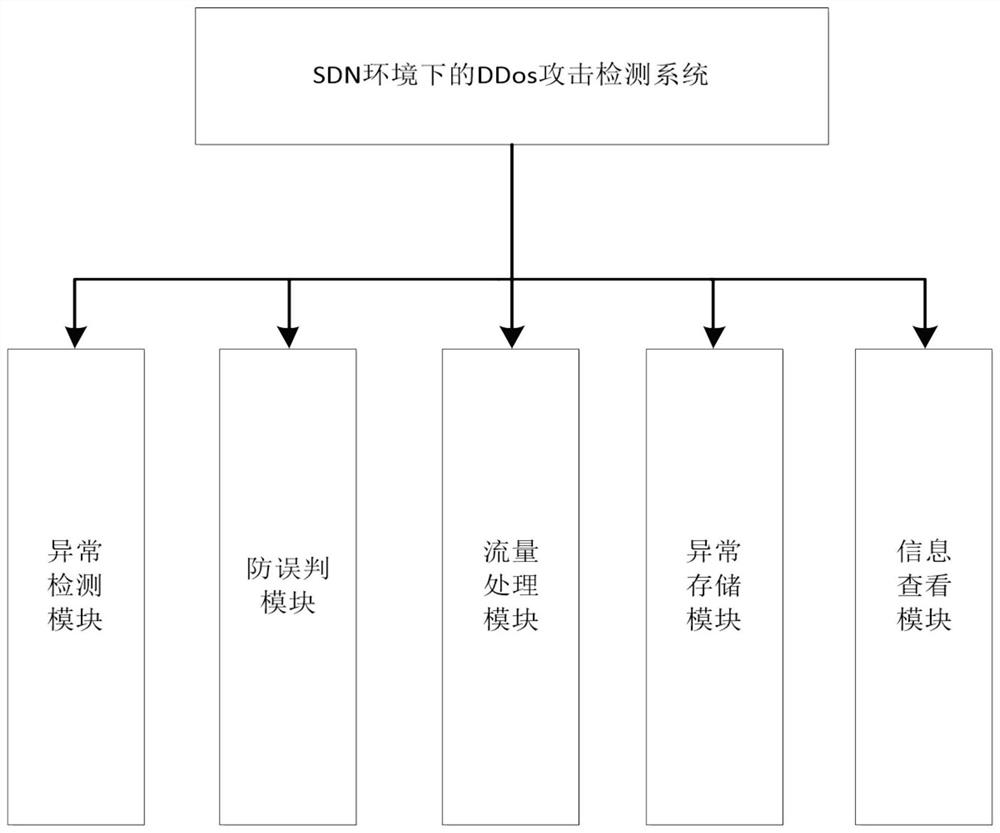
A ddos attack detection system and method in sdn environment
An attack detection and environment technology, applied in transmission systems, electrical components, etc., can solve problems such as network vulnerability and single-point failure, and achieve the effect of reducing pressure, reducing false alarm rate, and improving detection speed.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
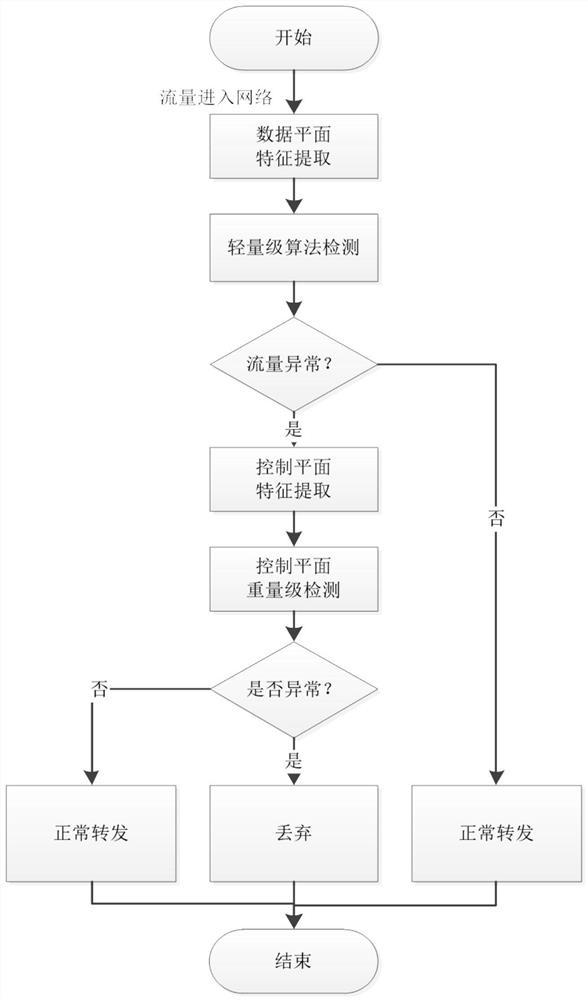
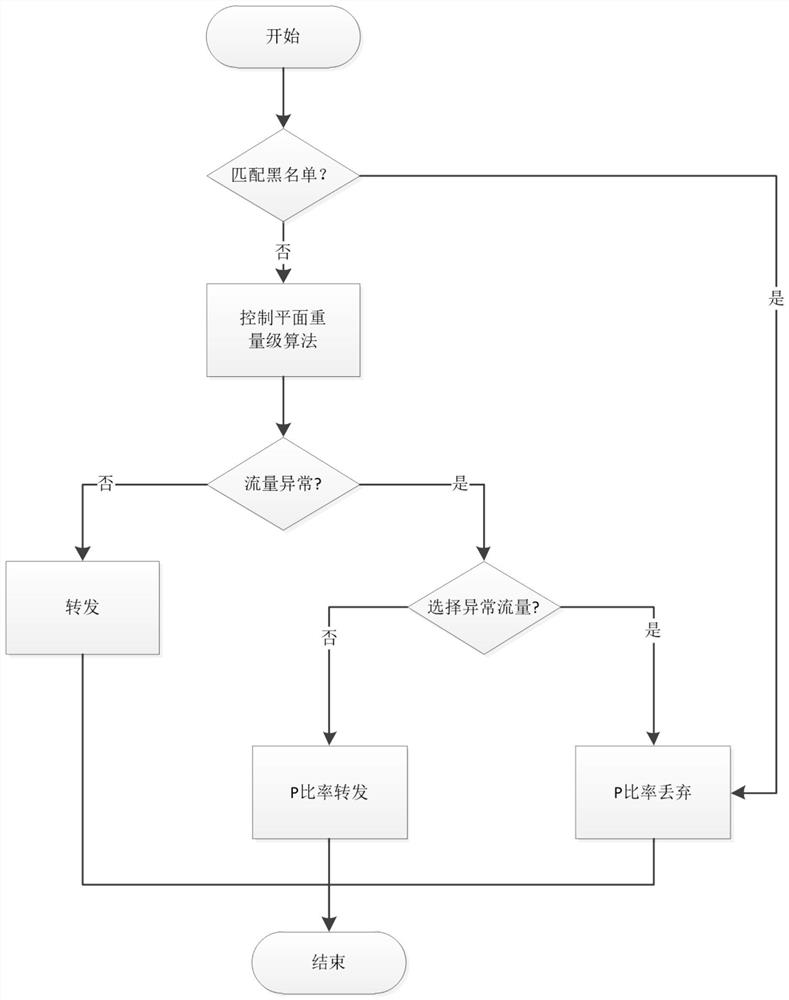
Method used
Image
Examples
Embodiment
[0037] The Mininet used in this embodiment is the virtual host required to create the topology in a standard Linux environment. The experimental environment uses ubuntu16.04. At the same time, Mininet also supports OpenFlow switches, OpenFlow controllers and secure link networks, and supports SDN and OpenFlow custom topology.
[0038] The present invention uses the OpenDaylight open source controller as the controller module under the SDN environment, and this controller is implemented based on the Java language, so before the design and development of the corresponding modules, it is necessary to install and configure the corresponding Java environment in the Ubuntu16.04 environment , that is, jdk, maven and other environments. In addition, before installing all software, you must first update apt, and then install git, which will be used as tools in subsequent installations.
[0039] The communication between two hosts requires a three-way TCP handshake. All requests from th...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More