Secure memory implementation method and system
A technology for realizing the system and method, which is applied in the field of computers, can solve the problems of high cost, the impossibility of using secure memory for low-end devices, and raise the threshold for mid-to-high-end devices, so as to reduce hardware dependence, wide application range, and improve security Effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0043] The technical solutions in the embodiments of the present invention are clearly and completely described below in conjunction with the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments are part of the embodiments of the present invention, but not all of them. Based on the embodiments of the present invention, all other embodiments obtained by those skilled in the art without making creative efforts belong to the protection scope of the present invention.
[0044] The purpose of this application is to provide a secure memory implementation method and its system, which has secure memory that can be quickly deployed, and reduces the dependence of security camera technology on hardware, so that security camera services can also be used on low-end devices that lack hardware protection The benefits brought about by the technical effect.
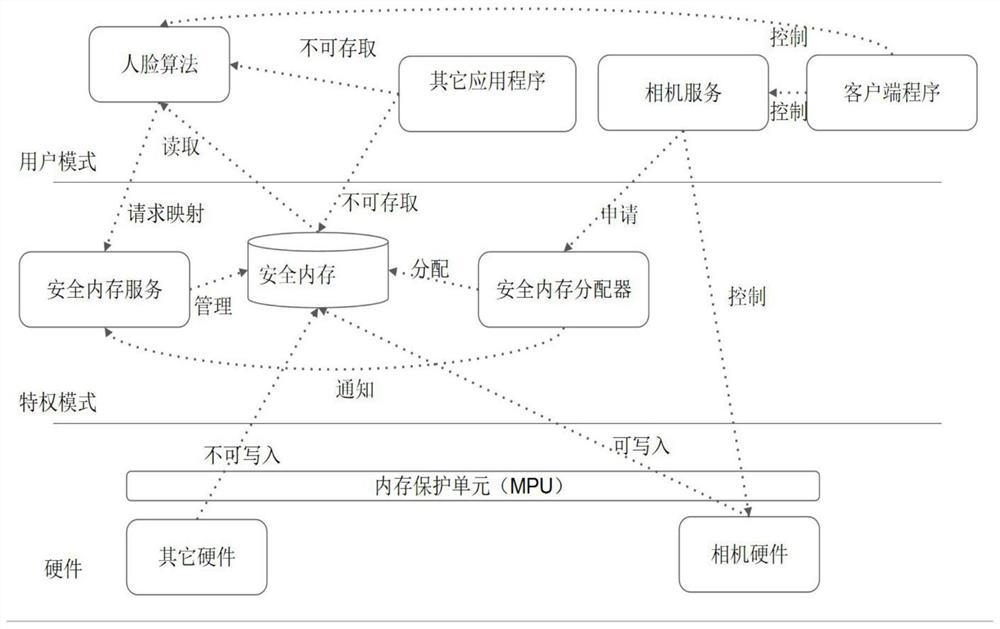
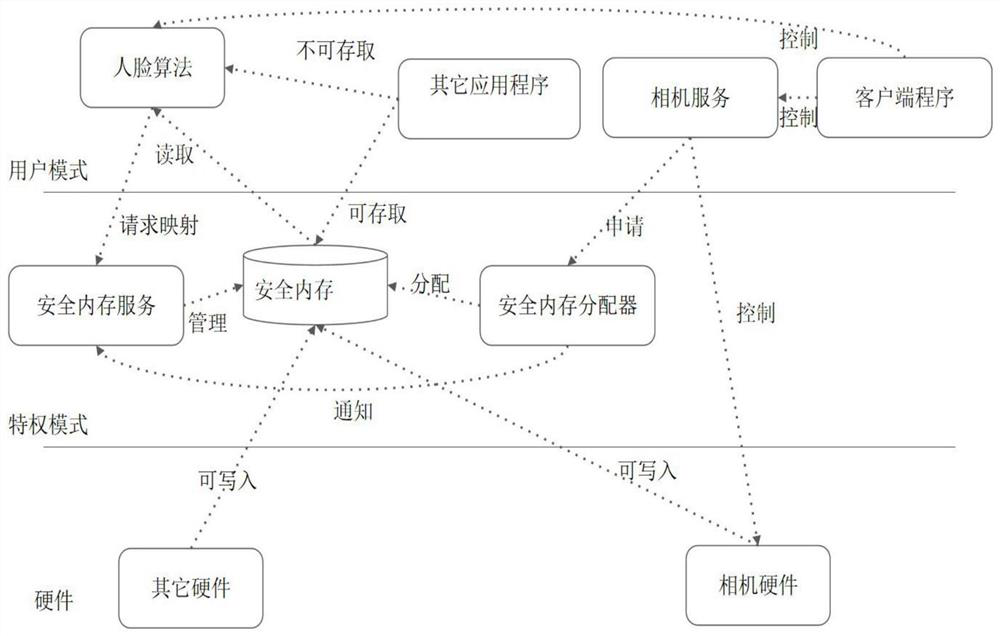
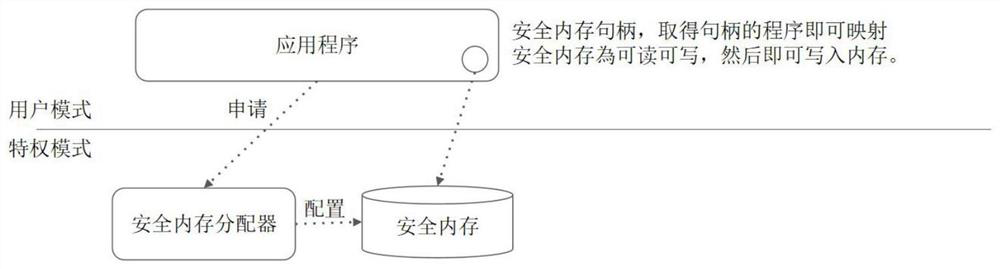
[0045] Such as Figure 5 As shown, the application provides a secure memory implemen...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More