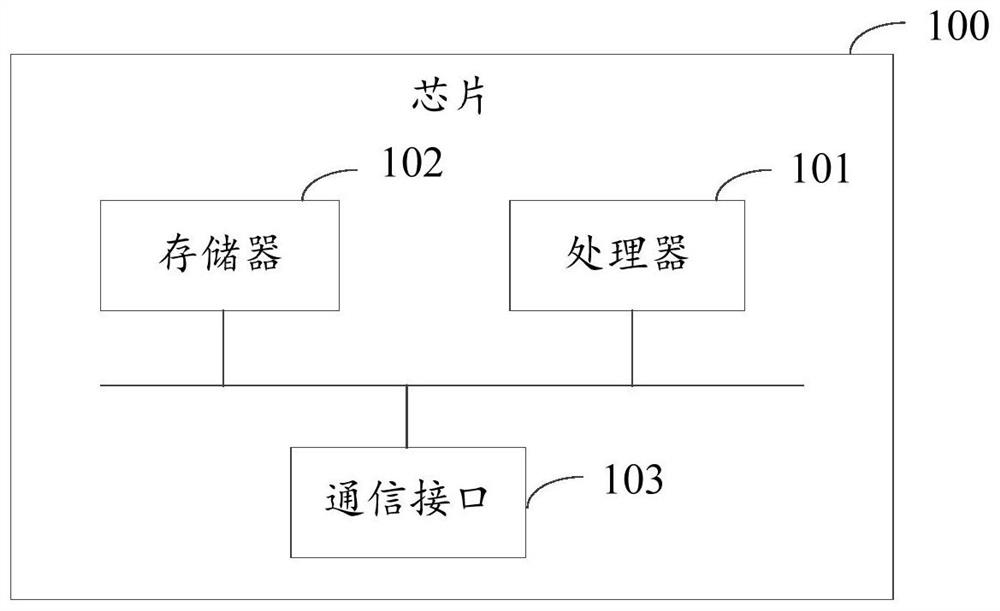
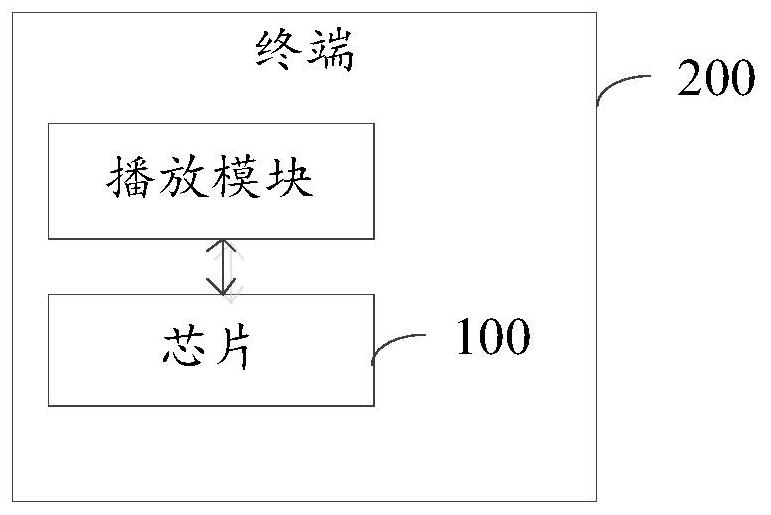
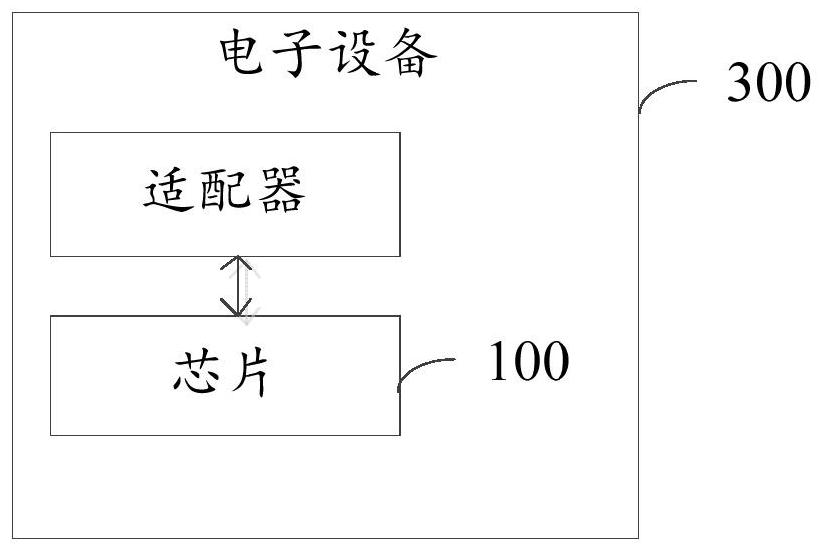
Information processing method and device, chip, terminal and electronic device
An information processing method and chip technology, applied in the field of information security, can solve problems such as failure of signature verification, easy existence of information security, problems, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment approach
[0063] In order to ensure subsequent signature verification using a certificate containing a trusted certificate number to ensure the legitimacy of the information broadcast by the broadcasting system, as an implementation manner, the method further includes steps: A1, A2 and A3.
[0064] A1: Receive the certificate number to be signed.
[0065] The information including the certificate numbers to be verified for signature is received in real time or irregularly, wherein the number of the certificate numbers to be verified may be one, two or more.
[0066] Wherein, the information includes: signature information and at least one certificate number to be verified; wherein, in this embodiment, the signature information is a signature operation performed on the certificate number to be verified by using the SM2-SM3 algorithm , the obtained signature information. In other embodiments, other signature algorithms may also be used to perform a signature operation on the certificate ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More