Network attack monitoring method based on multi-source information analysis
A network attack and multi-source information technology, applied to electrical components, transmission systems, etc., can solve problems such as inability to do intrusion, powerlessness, loss assessment, etc., and achieve the effect of improving comprehensive analysis capabilities
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
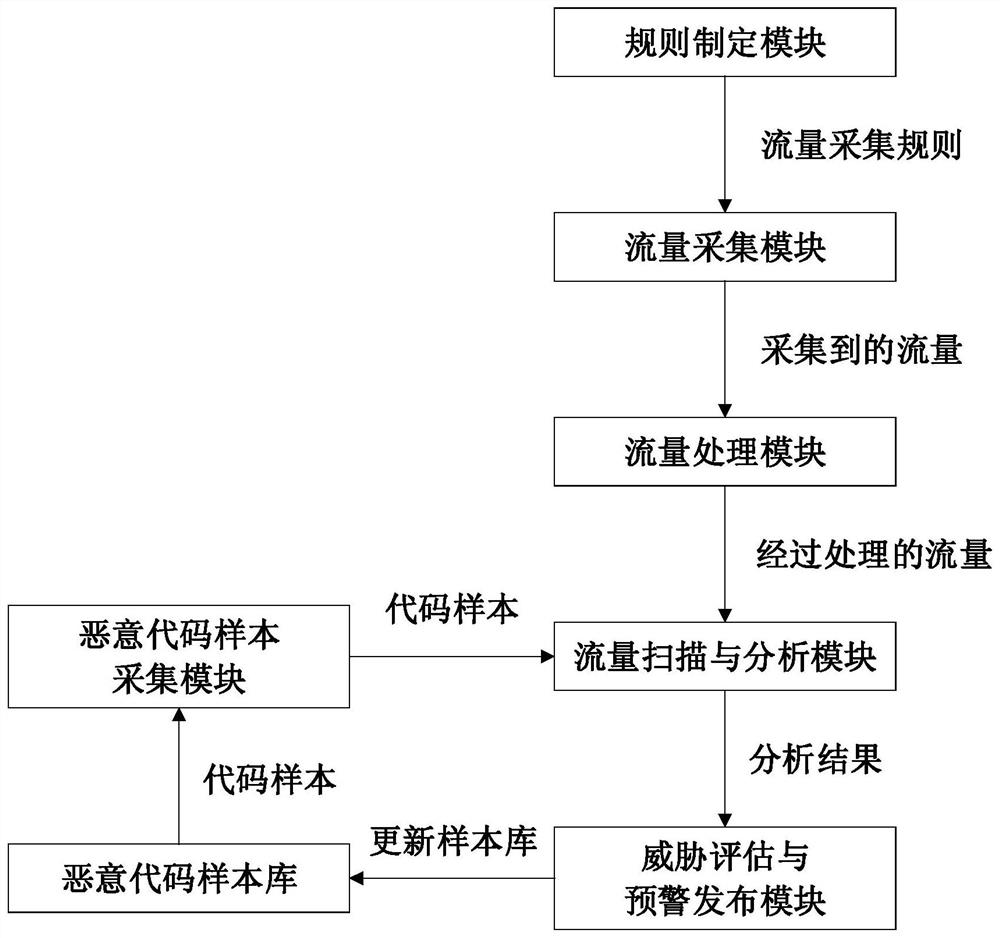
[0066] This embodiment provides a network attack monitoring system based on multi-source information analysis, which includes a traffic monitoring and collection module, a network attack analysis module, a malicious code analysis module, a threat assessment and early warning release module, and the like.
[0067] The workflow of the network attack monitoring system based on traffic analysis is as follows:
[0068] (1) Flow monitoring acquisition module
[0069] a) Collect and restore, collect and restore suspicious original traffic data monitored by network security monitoring probe equipment, standardize and store traffic data, and realize functions such as retrieval, traffic restoration, and file extraction.
[0070] b) Collection rules, for IP quintuples, fixed and floating location keywords, application protocols, etc., define in a visual way and deliver traffic collection rules to network security monitoring probe devices.
[0071] 1) IP quintuple refers to source IP add...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com