Password protection method based on honeyword
A password protection and password technology, applied in the field of database password protection and identity authentication, can solve the problems of user honeyword conflict and weakened attack effect, and achieve the effect of defending against double leakage attacks and cross update attacks, eliminating distribution differences, and reliable security protection.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0028] The above solution will be further described below in conjunction with specific embodiments. It should be understood that these examples are used to illustrate the present invention and not to limit the scope of the present invention. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts belong to the protection scope of the present invention.
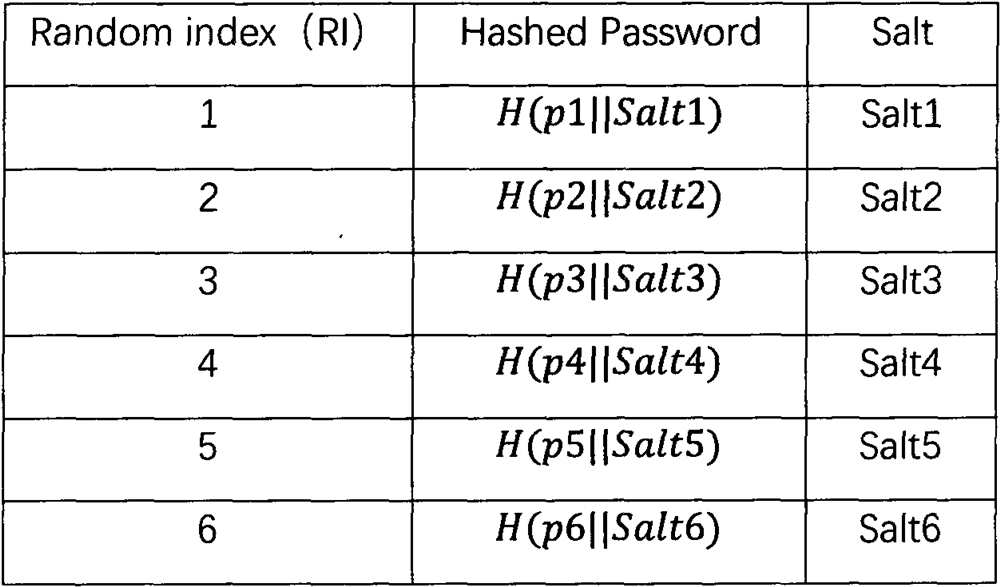
[0029] Usually the honeyword method sets G to 1000 and k to 20. For the convenience of the example, we set the example as follows: the number of a group of false users G=8, and the number of password values in each user's password group k=3. The table below is an example. The specific process is:
[0030] (1) Initialization.
[0031] (1.1) First, we need to generate a set of initialized fake user data. According to the settings, the main server generates 8 fake users, whose user names and passwords are constructed randomly. ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More