Self-hiding data transmission port data theft prevention encryption device for computer
A technology of hiding data and transmission ports, applied in the protection of internal/peripheral computer components, transmission systems, electrical components, etc., can solve problems affecting transmission efficiency and other issues
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0024] The following will clearly and completely describe the technical solutions in the embodiments of the present invention with reference to the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments are only some, not all, embodiments of the present invention. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts belong to the protection scope of the present invention.
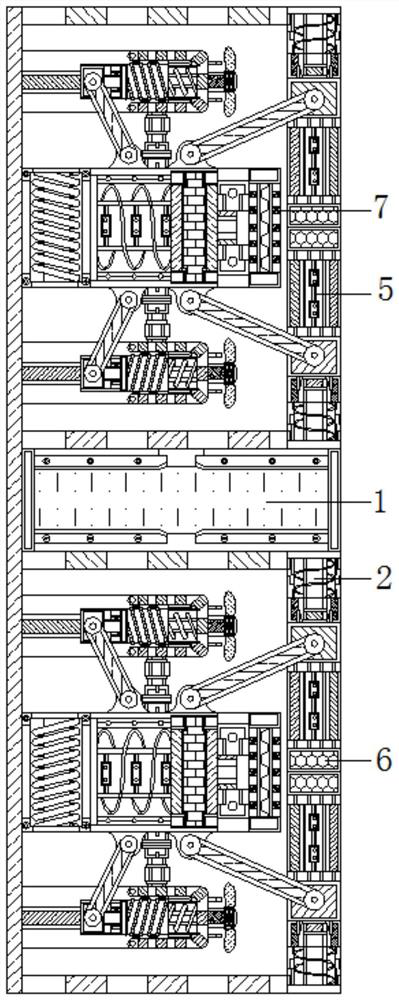
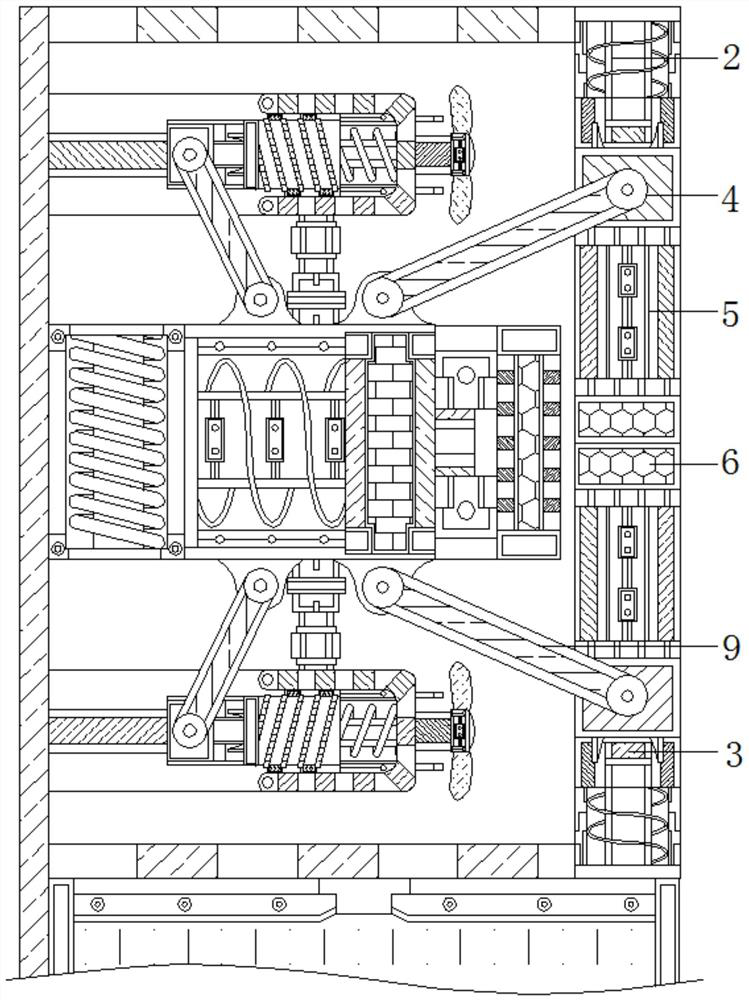
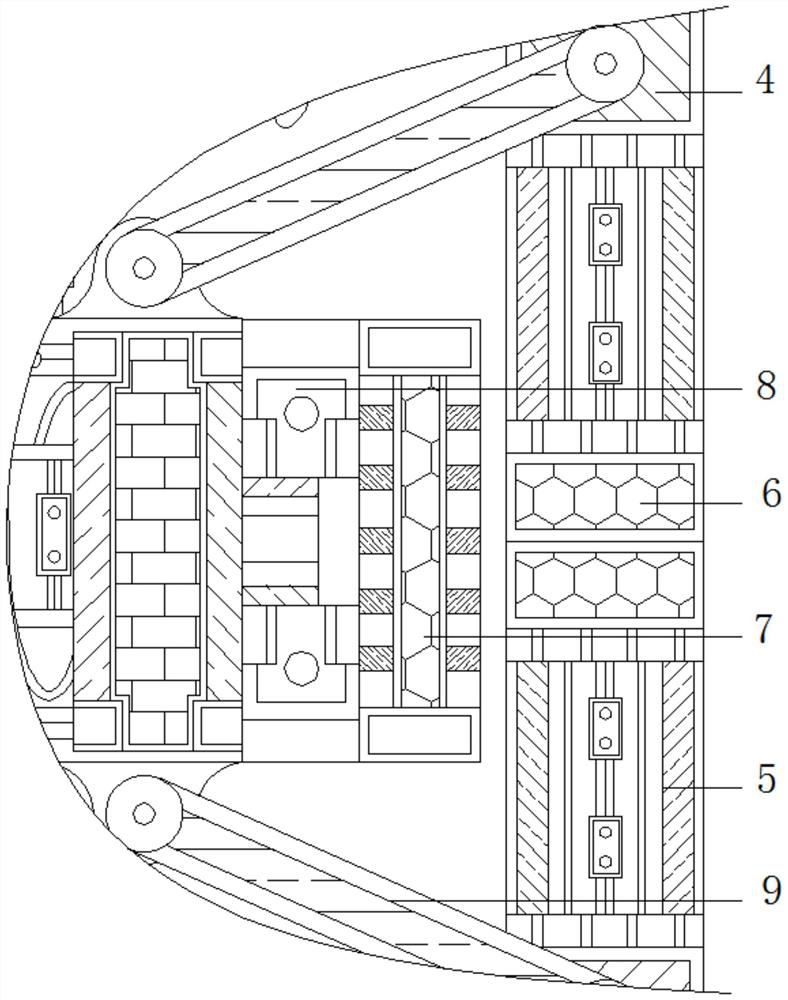
[0025] see Figure 1-5 , an encryption device for preventing data theft with a self-concealed data transmission port for a computer, comprising a mount 1, a return spring 2 is movably connected to the top of the mount 1, a connecting rod 3 is movably connected to the top of the return spring 2, and the top of the connecting rod 3 is movably connected Push block 4 is arranged, and explosion-proof plate 5 is movably connected to the top of push block 4, and stro...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More