Two-stage multi-layer resource scheduling method and system for mimicry defense
A resource scheduling and mimic system technology, applied in the field of network security, can solve the problems of small heterogeneous resource collection, loss randomness, limiting scheduling dynamics and heterogeneity, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0030] The present invention will be described in detail below in conjunction with specific embodiments. The following examples will help those skilled in the art to further understand the present invention, but do not limit the present invention in any form. It should be noted that those skilled in the art can make several changes and improvements without departing from the concept of the present invention. These all belong to the protection scope of the present invention.
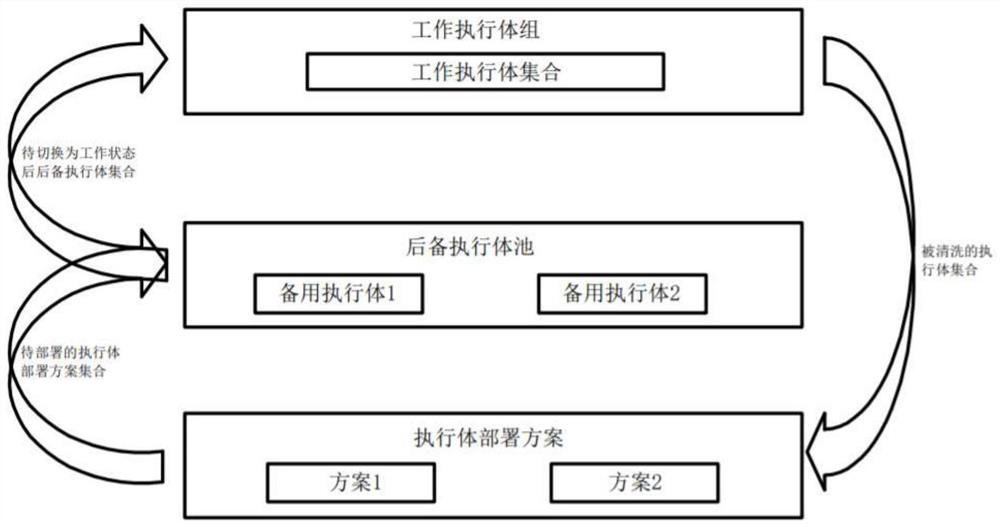
[0031] refer to figure 1 , a two-level and multi-layer resource scheduling method for mimicry defense, which ensures the dynamics and heterogeneity of the mimicry system by providing scheduling services for executives and resources during the stages of mimicry system creation, initialization, and executive cleaning and recovery. The method mainly includes a two-level scheduling process among the executive body deployment plan, backup executive body pool, and work executive body group, and a multi-layer ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More