Secure storage query and donation
A security, storage capacity technology, applied in the computer field
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0037] One or more embodiments of the invention provide additional security with efficient, lightweight secure interface controls between software and machines.
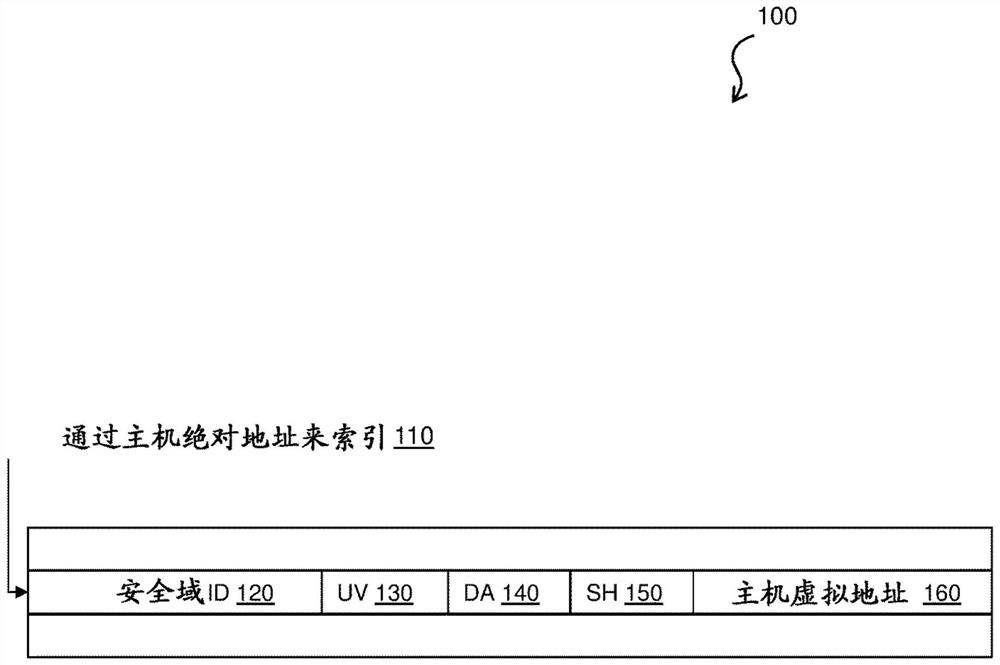
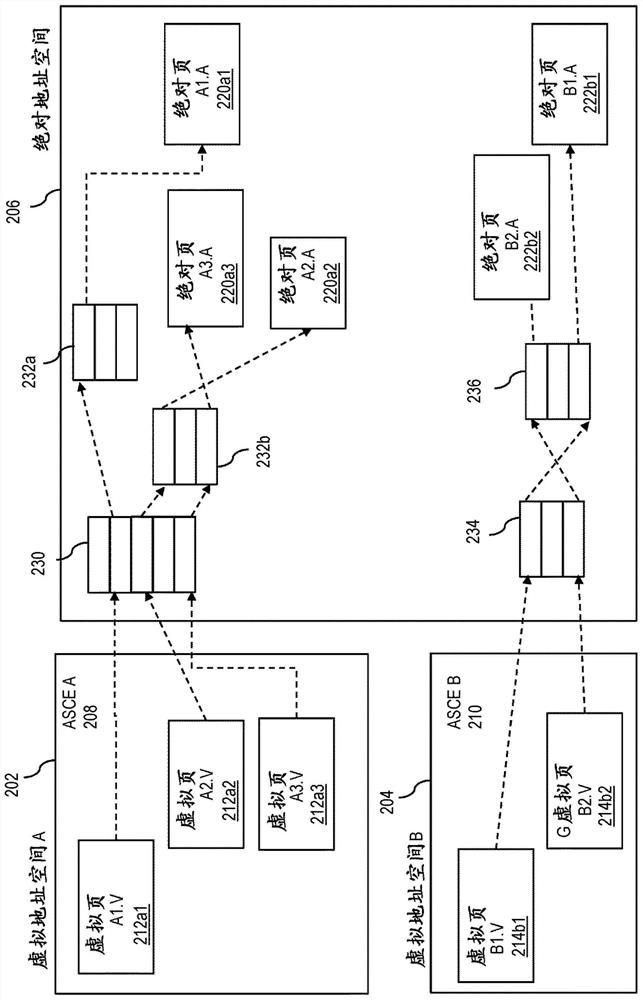
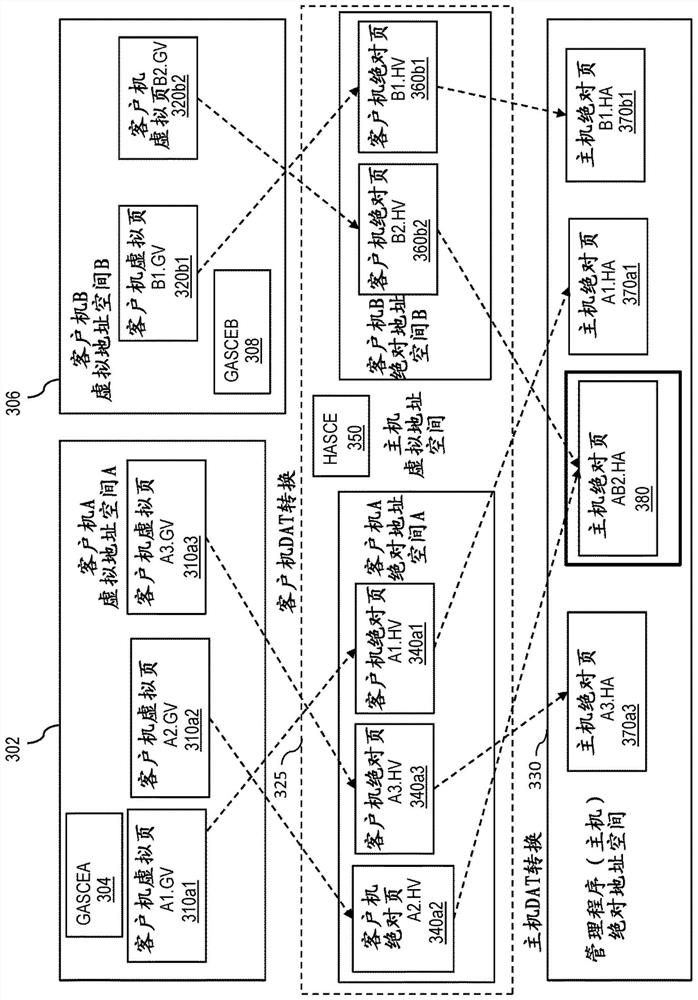
[0038]A virtual machine (VM) running as a guest under the control of a host hypervisor relies on the hypervisor to transparently provide virtualization services to the guest. These services can be applied to any interface between a secure entity and another untrusted entity that traditionally allows that other entity to access secure resources. As previously mentioned, these services may include, but are not limited to, memory management, instruction emulation, and interrupt handling. For example, for interrupt and exception injection, the hypervisor typically reads and / or writes to the guest's prefixed area (low core). The term "virtual machine" or "VM" as used herein refers to a logical representation of a physical machine (computing device, processor, etc.) and its processing environment (operating system (OS), s...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More