Method for designing event trigger filter of cyber-physical system under spoofing attack
A cyber-physical system and filter design technology, which is applied in the field of cyber-physical systems, can solve problems such as damage to the perception execution layer and data transmission layer of the cyber-physical system, increase in false triggers of data packets, and complex means of deception attacks, etc., to reduce the average The effect of data release rate, saving network communication resources, and improving bandwidth utilization
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
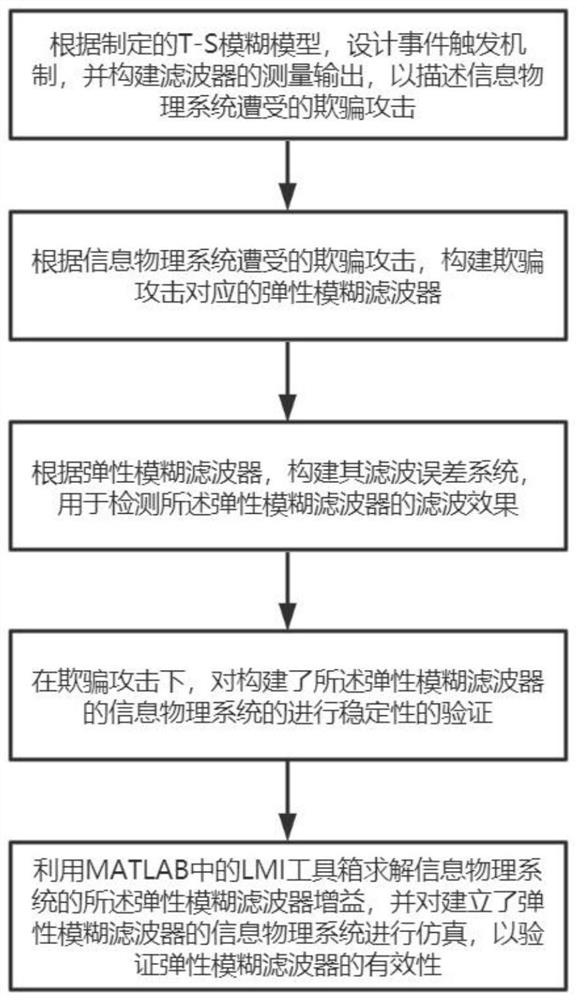
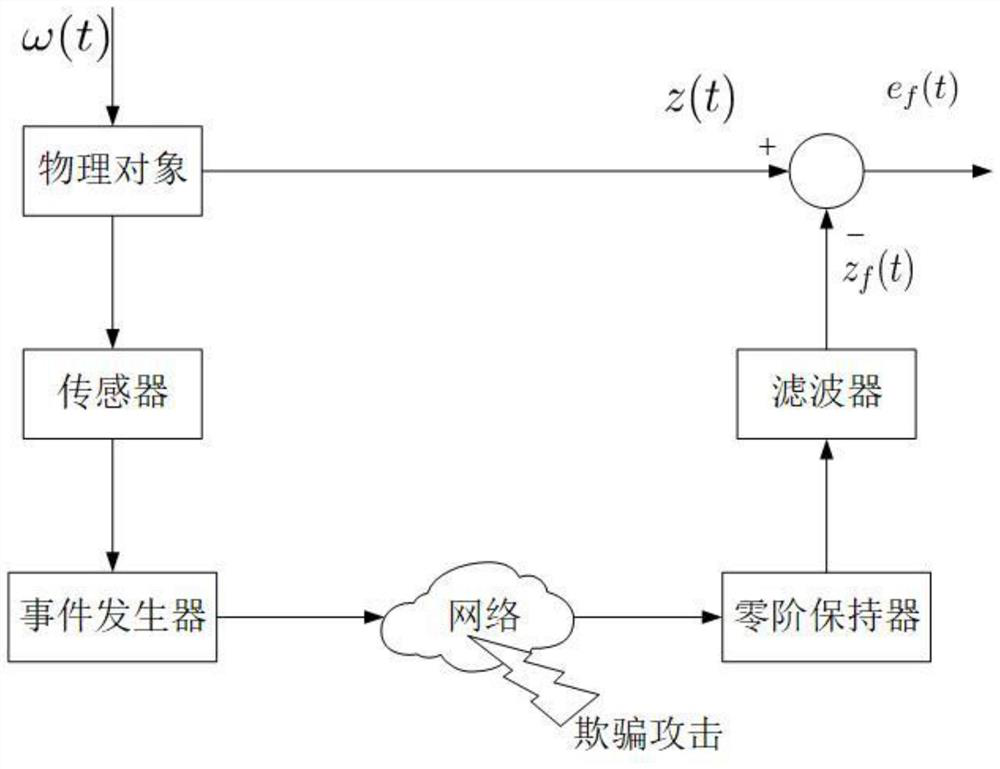
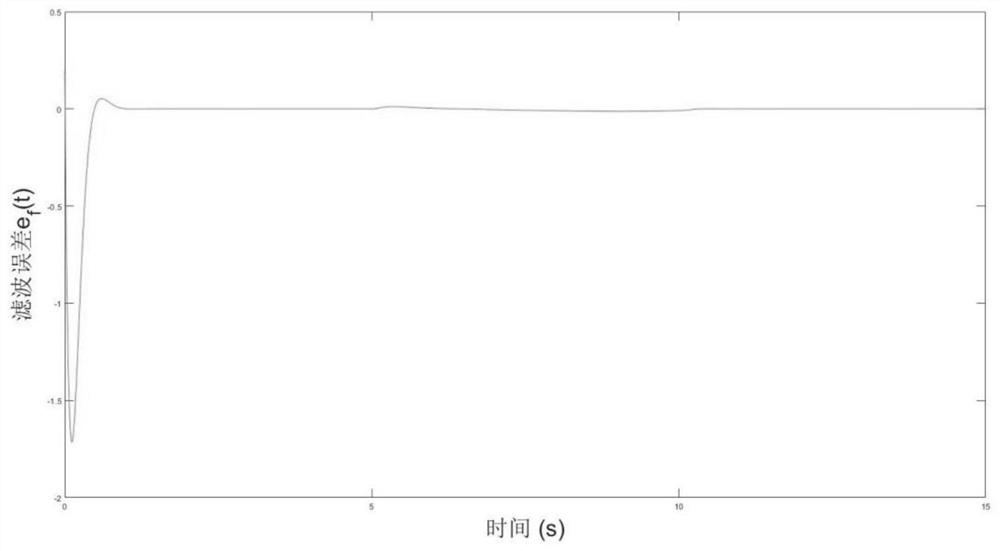
[0024] The following will clearly and completely describe the technical solutions in the embodiments of the present invention with reference to the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments are only some, not all, embodiments of the present invention. The components of the embodiments of the invention generally described and illustrated in the figures herein may be arranged and designed in a variety of different configurations. Accordingly, the following detailed description of the embodiments of the invention provided in the accompanying drawings is not intended to limit the scope of the claimed invention, but merely represents selected embodiments of the invention. Based on the embodiments of the present invention, all other embodiments obtained by those skilled in the art without making creative efforts belong to the protection scope of the present invention.
[0025] The present invention is realized through the...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More