UAV cluster access control method and device based on block chain, equipment and medium
An access control and block chain technology, applied in the direction of network data browsing optimization, digital data authentication, digital data protection, etc., can solve the problem of state information loss and achieve the effect of avoiding information loss
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
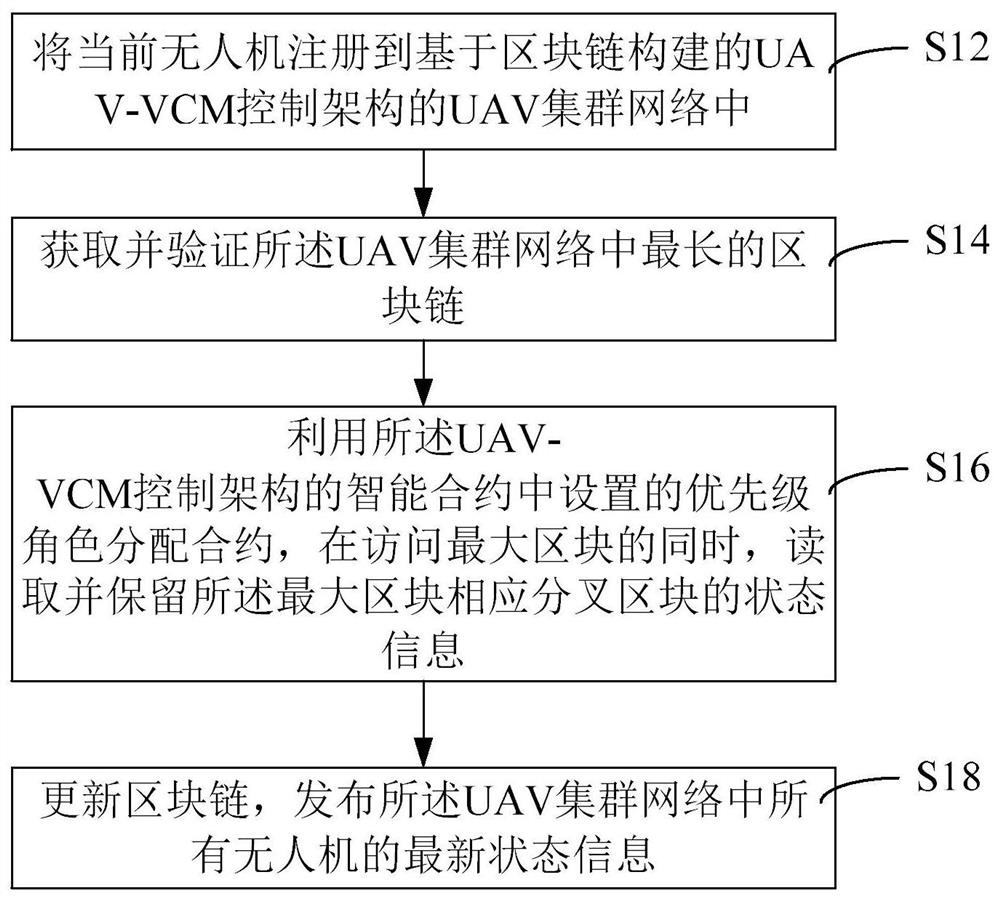
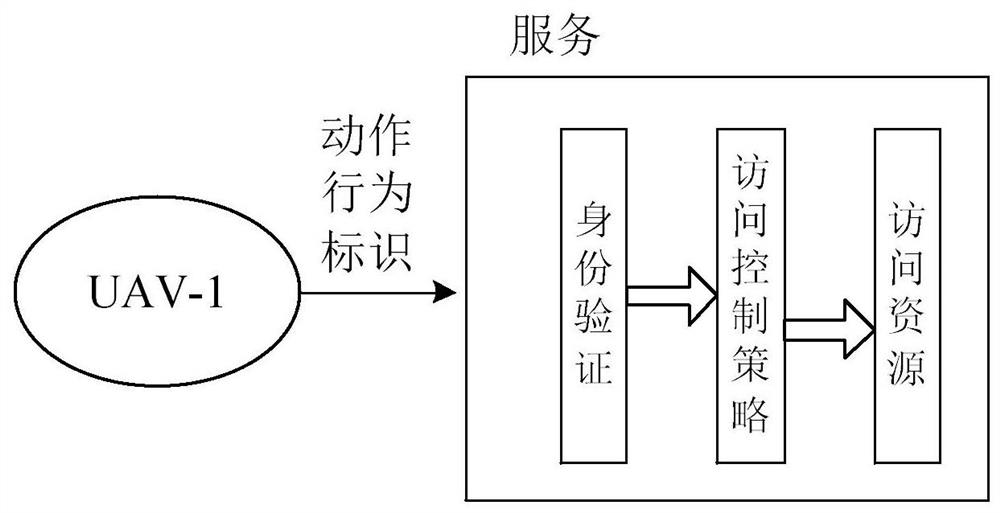
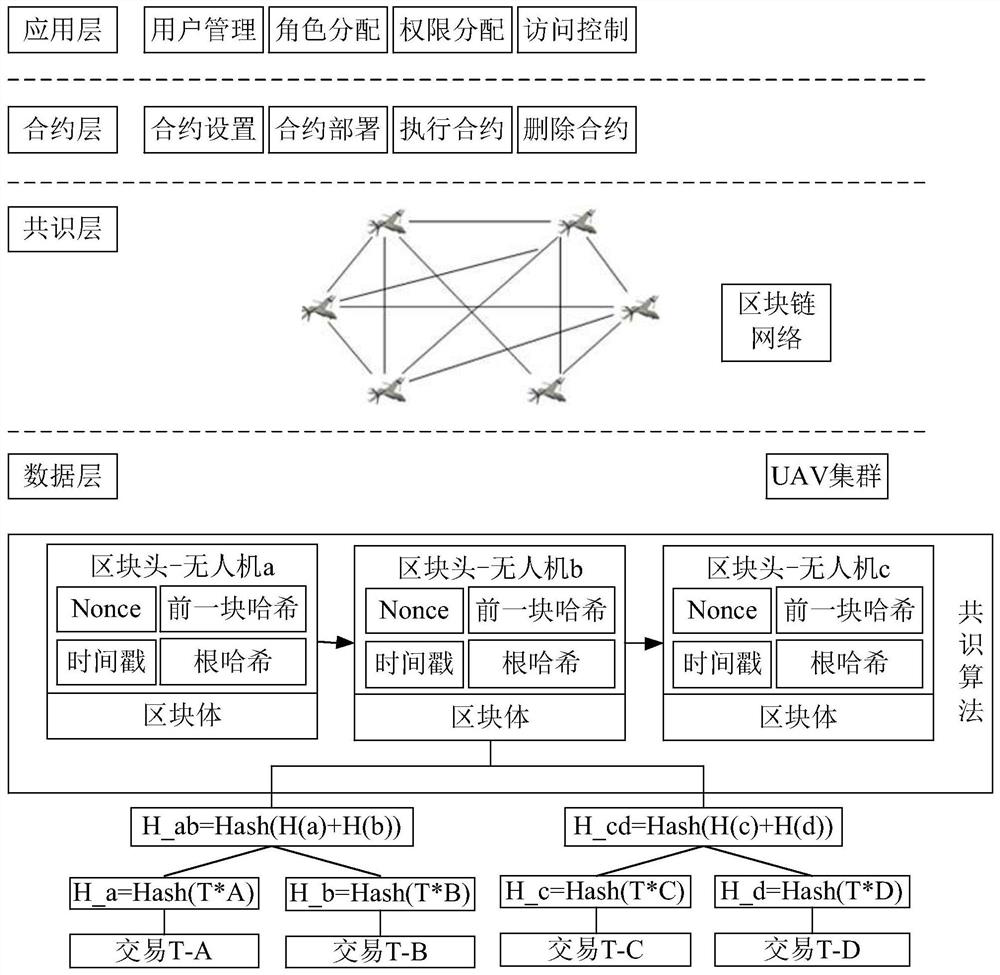
[0025] In order to make the purpose, technical solutions and advantages of the present application clearer, the present application will be described in further detail below in conjunction with the accompanying drawings and embodiments. It should be understood that the specific embodiments described here are only used to explain the present application, and are not intended to limit the present application.
[0026] Unless otherwise defined, all technical and scientific terms used herein have the same meaning as commonly understood by one of ordinary skill in the technical field to which this application belongs. The terms used herein in the description of the application are only for the purpose of describing specific embodiments, and are not intended to limit the application. As used herein, the term "and / or" includes any and all combinations of one or more of the associated listed items.
[0027] In addition, the technical solutions of the various embodiments of the presen...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More