Vulnerability repairing method based on big data vulnerability mining and artificial intelligence mining system
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
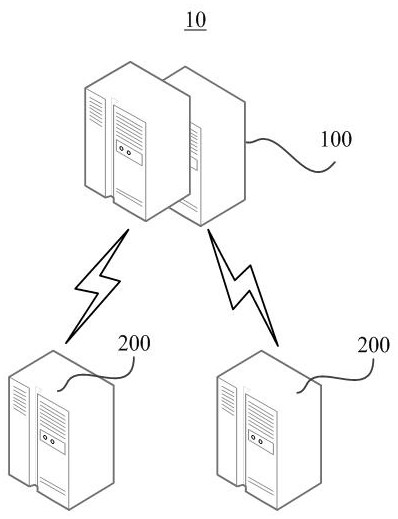
[0018] figure 1 It is a schematic diagram of an application scenario of a vulnerability repair system 10 based on big data vulnerability mining provided by an embodiment of the present application. The vulnerability repair system 10 based on big data vulnerability mining may include an artificial intelligence mining system 100 and a cloud service system 200 communicating with the artificial intelligence mining system 100 . figure 1 The shown vulnerability repair system 10 based on big data vulnerability mining is only a feasible example, and in other feasible embodiments, the vulnerability repair system 10 based on big data vulnerability mining may also only include figure 1 At least some of the components shown may also include other components.
[0019] In an embodiment that can be based on an independent idea, the artificial intelligence mining system 100 and the cloud service system 200 in the vulnerability repair system 10 based on big data vulnerability mining can coope...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com