AADL-based automatic generation method of attack defense tree
A technology for automatically generating and attacking paths, applied in the field of network security, can solve problems such as inability to form an architecture, difficult to solve, and difficult to model
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0021] The following will clearly and completely describe the technical solutions in the embodiments of the present invention with reference to the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments are only some, not all, embodiments of the present invention. Based on the embodiments of the present invention, all other embodiments obtained by those skilled in the art without creative efforts fall within the protection scope of the present invention.
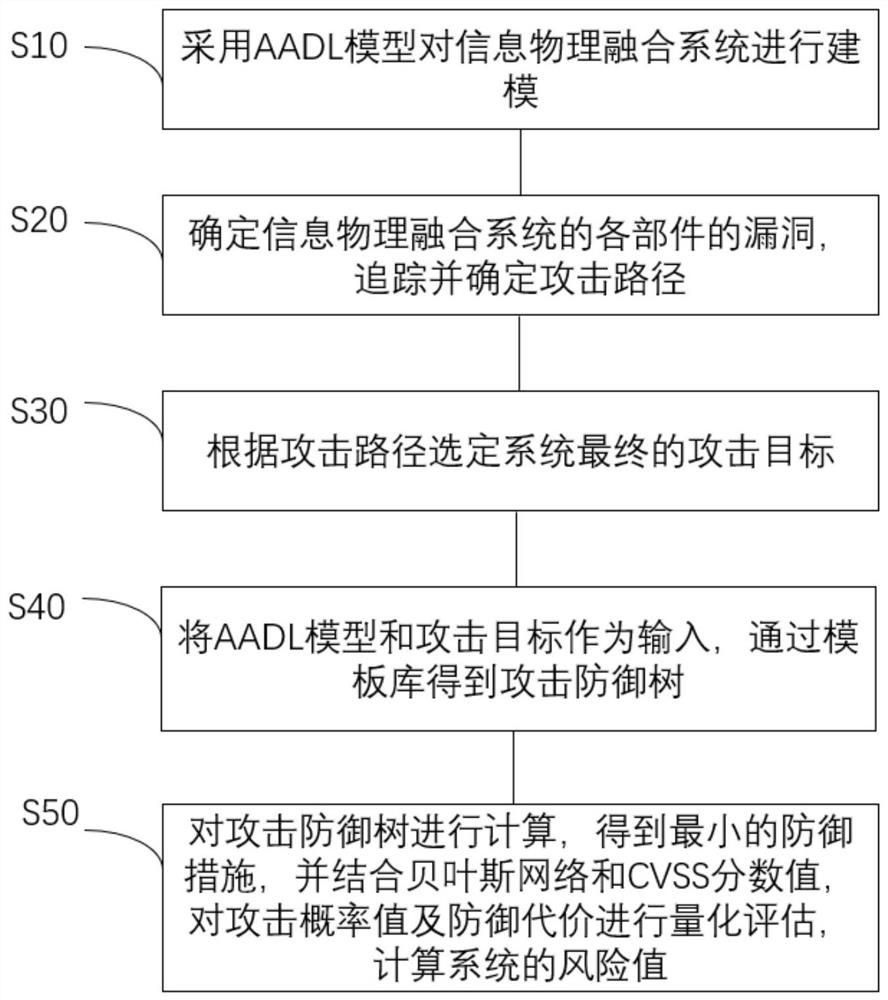
[0022] see figure 1 As shown, the present invention provides a kind of automatic generation method of the attack defense tree based on AADL, and described method comprises the steps:
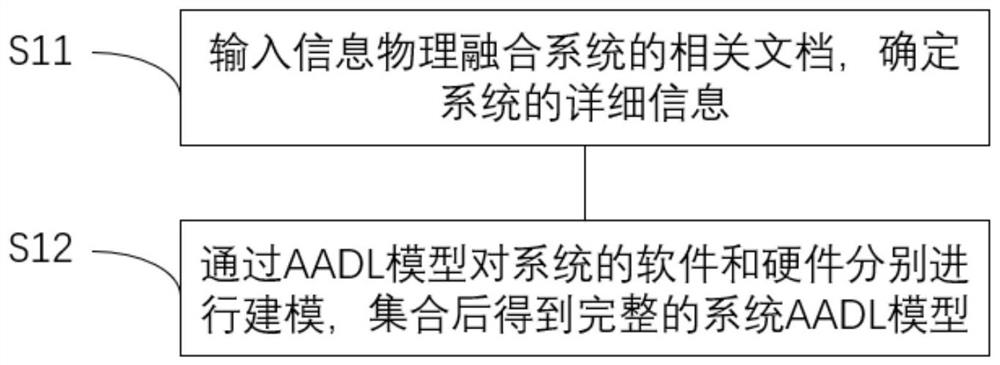
[0023] Step S10, using the AADL model to model the cyber-physical fusion system.
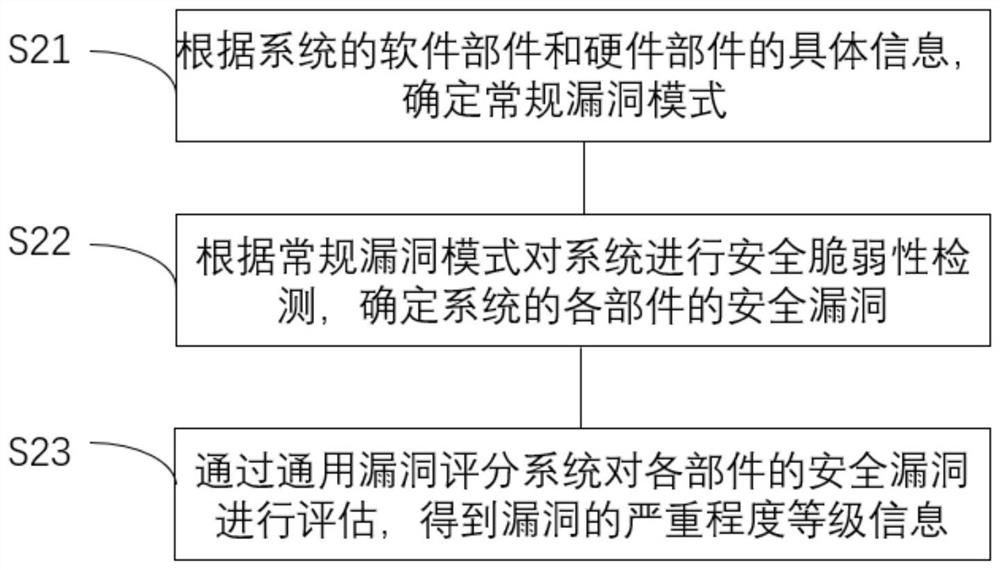
[0024] Determine all components (software and hardware) of the cyber-physical fusion system and their relationships, and use AADL to model the system architecture. With the development of technology, cyber-physi...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More