Searchable encryption method based on wildcard identity
An encryption method and wildcard technology, which is applied to secure communication devices and key distribution, can solve the problems of high requirements for public key encryption, and achieve the effect of resisting malicious damage, data security and privacy leaks, and resisting quantum computing attacks
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0054] The technical solutions of the present invention will be clearly and completely described below with reference to the embodiments. Obviously, the described embodiments are only a part of the embodiments of the present invention, rather than all the embodiments. Based on the embodiments of the present invention, all other embodiments obtained by those skilled in the art without creative efforts shall fall within the protection scope of the present invention.
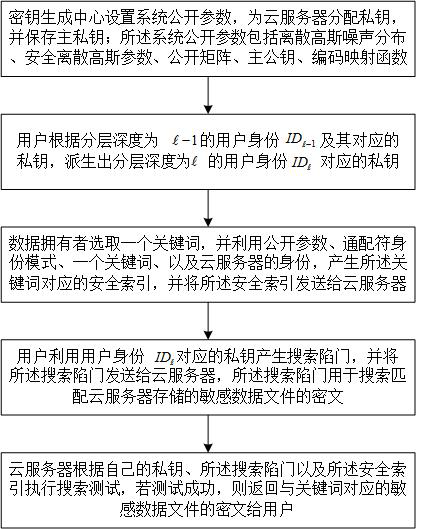
[0055] see figure 1 , this embodiment provides a searchable encryption method based on wildcard identity:
[0056] A searchable encryption method based on wildcard identity, applied to a cryptographic system, the cryptographic system includes a trusted center, a cloud server, a data owner and a user, and the cloud server communicates with the trusted center, the data owner and the user respectively connect.
[0057] The searchable encryption method includes:
[0058] S100. The key generation center sets public p...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More