Method and system in a digital wireless data communication network for arranging data encryption and corresponding server
A data encryption and server technology, applied in the field of [0006], can solve problems such as implementation trouble, and achieve the effects of reduced data transmission, high security level, and simple implementation
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
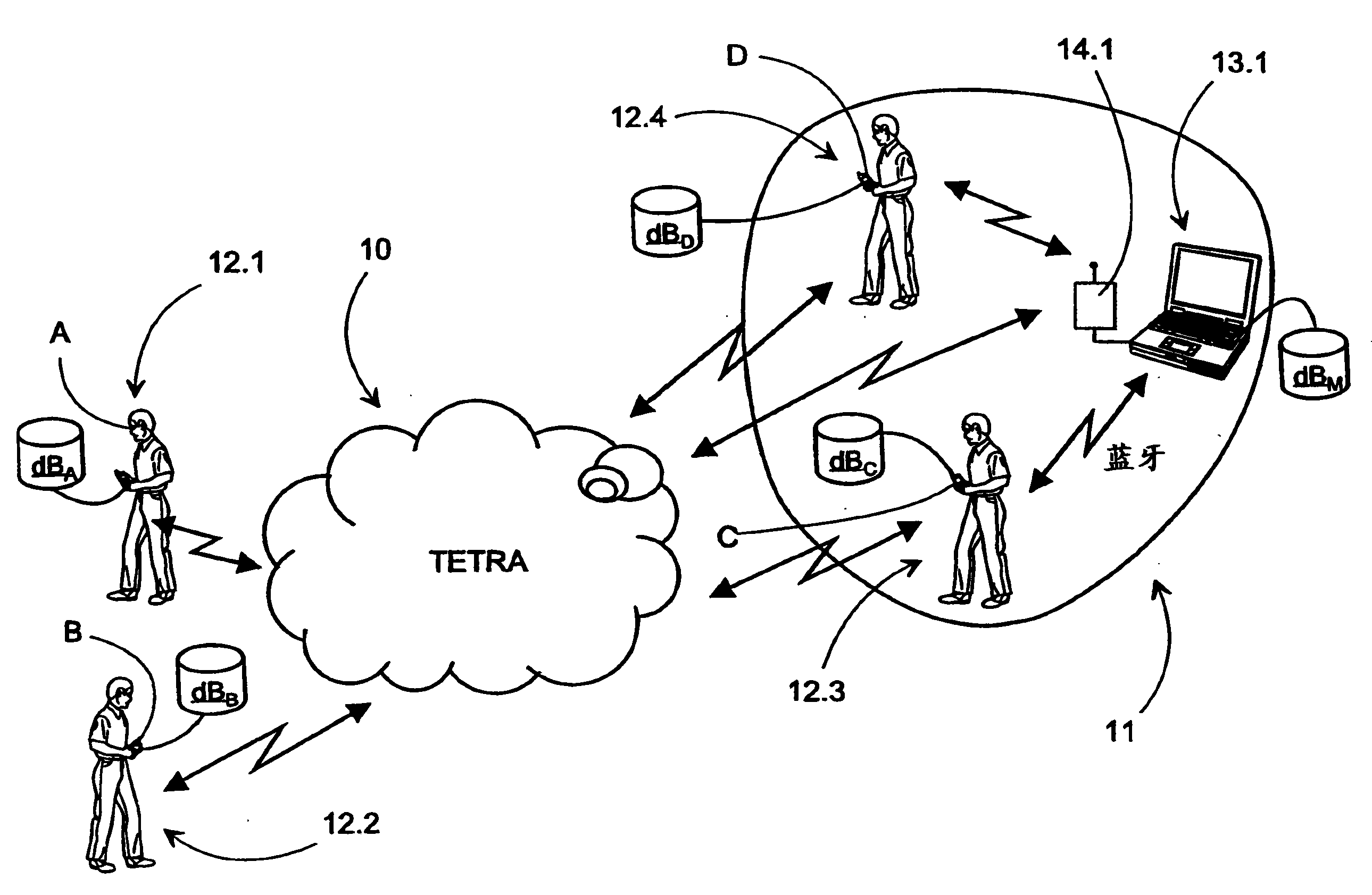
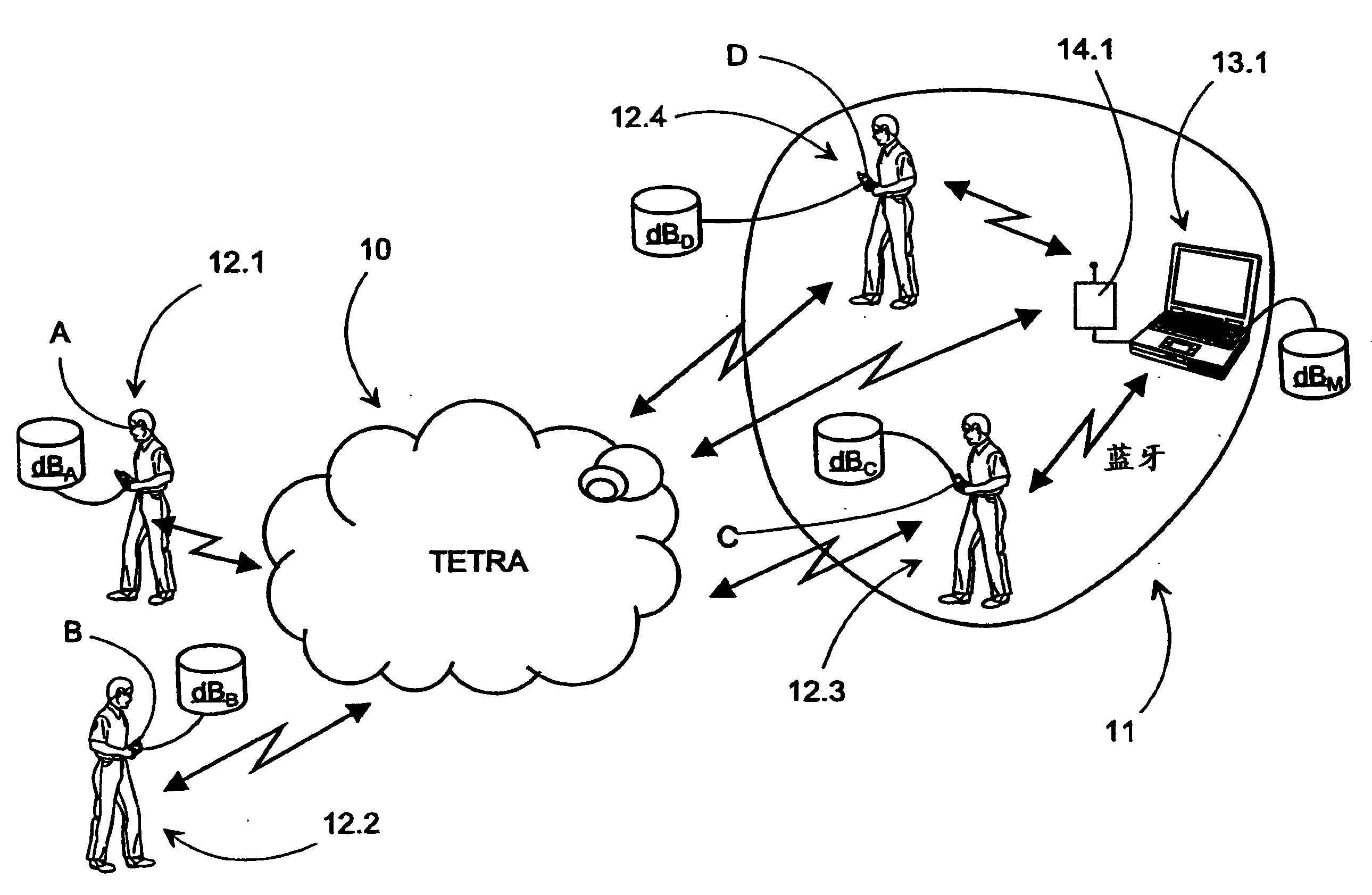
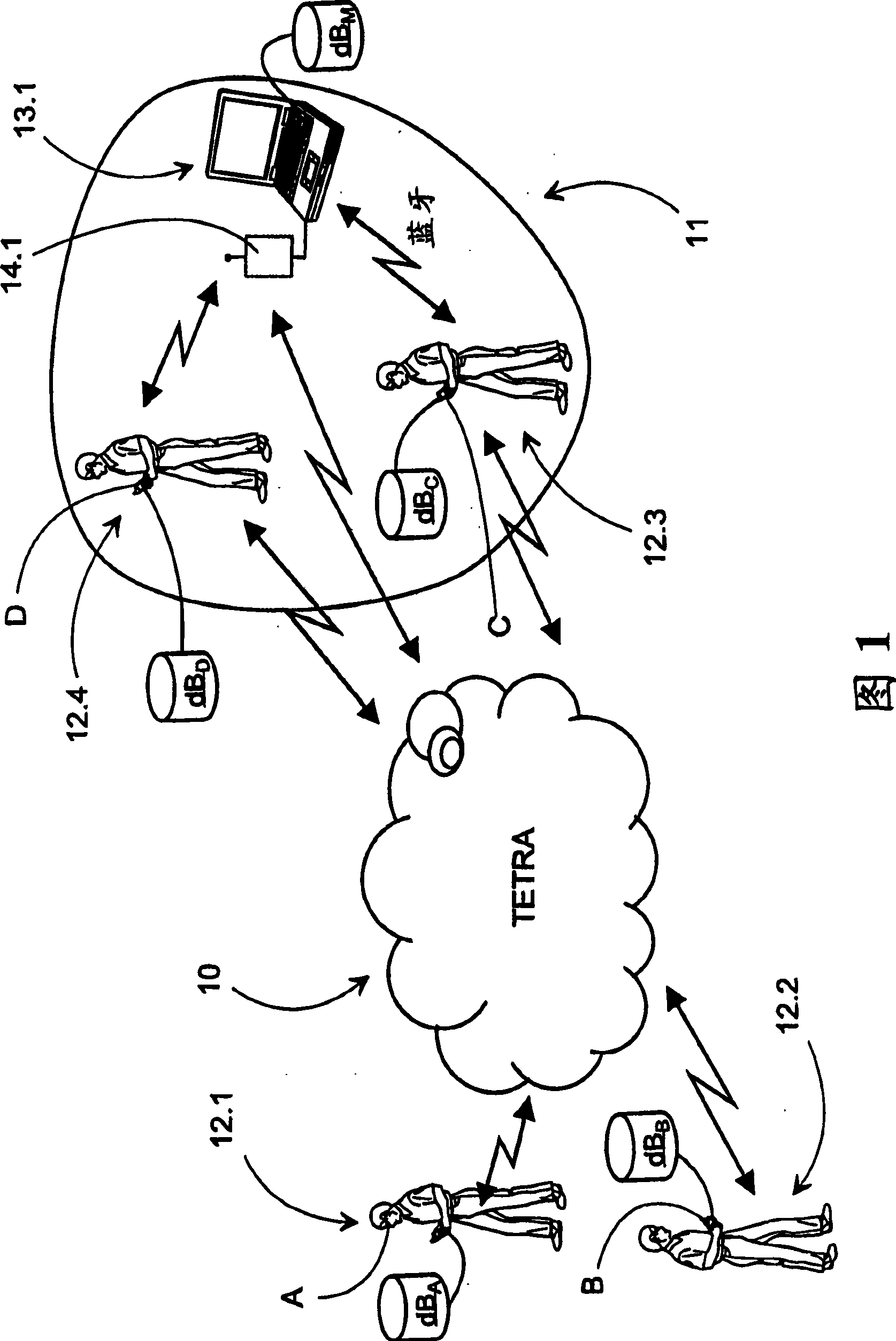
[0038] Figure 1 is a schematic diagram of an example of an embodiment of a system according to the invention. The system and method according to the present invention involves arranging data encryption in a digital wireless data communication network 10, 11 according to a one-time pad encryption model. The data communication network 10, 11 may be a wired network, such as an IP network (eg Internet, Intranet, Local Area Network), or wireless (eg WLAN, CDMA, TDMA, FDMA, Bluetooth).
[0039] The data communication network 10, 11, wireless in the case shown as an example, comprises at least two terminal devices A-D communicating with each other, wherein one terminal device A is used at least as a transmitter and the other terminal device B is used at least as a receiver machine. The communication between the terminal devices A, B may eg be directly in a data format, such as SMS messages, or e-mail, or indirectly in a data format, such as encoded speech.
[0040] Furthermore, the...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More